Difference between revisions of "Lilith2"
From Gender and Tech Resources
m (→Controlled folly) (Tag: VisualEditor) |
m (→Solidarity network) |
||
| (100 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
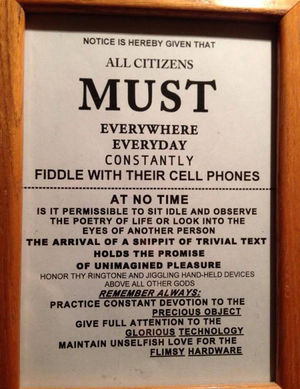
| + | [[File:fiddling.jpg|300px|thumb|right|Keep calm & Keep on fiddling]] | ||
== Narratives == | == Narratives == | ||
All of us, without exception, believe a mix of truth and misinformation, and often enough, disinformation. We strive to understand the world as it is, and not how it looks only according to our preconceptions, which are shaped by a multitude of forces, embedded as we are in our cultural matrix. Sometimes, the most unlikely seeming explanation turns out to be the correct one. In a warrior mindset we consider alternative views, but question everything. | All of us, without exception, believe a mix of truth and misinformation, and often enough, disinformation. We strive to understand the world as it is, and not how it looks only according to our preconceptions, which are shaped by a multitude of forces, embedded as we are in our cultural matrix. Sometimes, the most unlikely seeming explanation turns out to be the correct one. In a warrior mindset we consider alternative views, but question everything. | ||
| Line 4: | Line 5: | ||
Asking for details from ones own cultural matrix is not enough. Not even close. One needs to eat the local food, drink the water, breathe the air, listen to the stories, smell the earth, feel the bark of the trees, see local peoples, and experience local ways to catch what can only be described as a mere glimpse of the answer 42, the knowledge hidden in the trees and wheels in that specific locality on this beautiful planet. | Asking for details from ones own cultural matrix is not enough. Not even close. One needs to eat the local food, drink the water, breathe the air, listen to the stories, smell the earth, feel the bark of the trees, see local peoples, and experience local ways to catch what can only be described as a mere glimpse of the answer 42, the knowledge hidden in the trees and wheels in that specific locality on this beautiful planet. | ||
| − | People and communities use stories to understand the world and our place in it. These stories are embedded with power - the power to explain and justify the status quo as well as the power to make change imaginable and urgent. | + | People and communities use stories to understand the world and our place in it. These stories are embedded with power - the power to explain and justify the status quo as well as the power to make change imaginable and urgent. |
| − | + | ||
* [[Timeline merchants of death]] | * [[Timeline merchants of death]] | ||
* [[Timeline masters of the internet]] | * [[Timeline masters of the internet]] | ||
* [[Timeline that is soooo 1984 ...]] | * [[Timeline that is soooo 1984 ...]] | ||
| − | + | A narrative analysis of power encourages us to ask: Which stories define cultural norms? Where did these stories come from? Whose stories were ignored or erased to create these norms? And, most urgently, what new stories can we tell to help create the world we desire? <ref>Harnessing the power of narrative for social change https://www.newtactics.org/conversation/change-story-harnessing-power-narrative-social-change</ref><ref>Underminers Chapter Ten – Reclaiming Ourselves http://underminers.org/the-book/chapter-10/</ref> | |
== Mindmaps and mindsets == | == Mindmaps and mindsets == | ||
| + | If a mindmap is a cognitive "hathanger" then a mindset are the clothes hanging on the hathanger. Most traditions have mindmaps that have been and are evolving locally from the experiences of the previous generations on what worked and what didn't for them. Afaik, the oldest mindmaps use trees and wheels. And all mindmaps are generalisations in the wind without grounding details if not from there. The adversary grouping of the petty tyrants map is useful for gathering and interpreting data from narratives, questioning and timelines into a framework of possible threats. | ||
| − | |||
* [[Petty tyrants]] | * [[Petty tyrants]] | ||
| − | + | * [[Captivating capital and copyfighting]] | |
| − | + | * [[Encrypting everything]] | |
| − | + | * [[Arcane mixing techniques]] | |
| − | + | * [[Networking concepts]] | |
| − | + | * [[A typical linux distribution]] | |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
== Methodologies, processes and choreographies == | == Methodologies, processes and choreographies == | ||
| − | Most processes are adapted to allow for minimalist approaches and to minimalise the risk of unintentionally becoming the petty tyrants we fight. | + | Most processes are adapted to allow for minimalist approaches and to minimalise the risk of unintentionally becoming the petty tyrants we fight <ref>Portal 2 Soundtrack Cara Mia (Turret Opera) One Hour https://www.youtube.com/watch?v=wFKfkfCeFj4</ref>. |
| + | |||
* [[Shortest retrospective ever]] | * [[Shortest retrospective ever]] | ||
| − | + | * [[Scenario planning]] | |
| − | * [[Scenario planning]] | + | * [[Linux development process]] |
| − | * [[ | + | |
| − | + | ||
| − | + | ||
| − | + | ||
| − | == | + | == Edge == |
| − | + | ||
| − | + | ||
| − | + | ||
* [[Confusing surveillance systems]] | * [[Confusing surveillance systems]] | ||
| + | * [[Simulations]] | ||
| + | ** [[Simulation: Game of Goose]] | ||
| + | ** [[Simulation: Mixnets]] | ||
| + | * [[Linux virtualisation]] | ||
| − | == | + | == Getting started with linux == |
''Standing on a hilltop in a thunderstorm on bare feet, wearing wet copper armour, holding a lightning rod and shouting ... bring it on, ye gods and godesses!'' | ''Standing on a hilltop in a thunderstorm on bare feet, wearing wet copper armour, holding a lightning rod and shouting ... bring it on, ye gods and godesses!'' | ||
| − | We use lawful techniques and tools. And if need be we invent new (GNU and creative commons licensed) techniques and tools <ref>Portal - 'Still Alive' https://www.youtube.com/watch?v=Y6ljFaKRTrI | + | We use lawful techniques and tools. And if need be we invent new (GNU and creative commons licensed) techniques and tools <ref>Portal - 'Still Alive' https://www.youtube.com/watch?v=Y6ljFaKRTrI</ref>. |
| − | </ref>. | + | |
* [[Installing linux]] | * [[Installing linux]] | ||
| + | * [[Linux applications]] | ||
* [[Linux security]] | * [[Linux security]] | ||
* [[Kinky linux command-line]] | * [[Kinky linux command-line]] | ||
| + | * [[Object encryption on linux]] | ||
| + | * [[Anonymising your traffic with linux]] | ||
| + | * [[Clean up all the things]] | ||
| + | * [[Shell scripting]] | ||
| − | === | + | == Teacher inside == |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
* [[Self-dox]] | * [[Self-dox]] | ||
| − | + | * [[Reconnaissance]] | |
| + | * [[Network exploitation and monitoring]] | ||
| + | * [[Reverse engineering]] | ||
| + | * [[Roleplay]] | ||
* [[Trolling]] | * [[Trolling]] | ||
| + | * [[Elicitation]] | ||
| + | * [[Wordsmithing]] | ||
| + | * [[Take control of the tech]] | ||
| + | * [[Making our own linux images]] | ||
== Autonomy shaping infrastructure == | == Autonomy shaping infrastructure == | ||
| − | * | + | |
| − | * | + | * For setting up a home server see the [https://undisconnect.miraheze.org/wiki/Main_Page Servers Everywhere! section on UnDisConnect] |
| − | * | + | * For setting up a server see the documentation in the [http://anarchaserver.org/mediawiki/index.php/Anarcha_section Anarcha section on Alexandria] |
| − | * | + | * [[Linux server security]] |
| + | * Radio | ||
| + | * Libraries | ||
| + | * Meshnets | ||
| + | * Clusternets | ||
| + | |||
| + | == Solidarity network == | ||
| + | |||
| + | * [[Threats, detection, protection and (counter) moves]] | ||
== References == | == References == | ||
<references />. | <references />. | ||
Latest revision as of 14:02, 9 October 2015
Contents
Narratives
All of us, without exception, believe a mix of truth and misinformation, and often enough, disinformation. We strive to understand the world as it is, and not how it looks only according to our preconceptions, which are shaped by a multitude of forces, embedded as we are in our cultural matrix. Sometimes, the most unlikely seeming explanation turns out to be the correct one. In a warrior mindset we consider alternative views, but question everything.
Asking for details from ones own cultural matrix is not enough. Not even close. One needs to eat the local food, drink the water, breathe the air, listen to the stories, smell the earth, feel the bark of the trees, see local peoples, and experience local ways to catch what can only be described as a mere glimpse of the answer 42, the knowledge hidden in the trees and wheels in that specific locality on this beautiful planet.
People and communities use stories to understand the world and our place in it. These stories are embedded with power - the power to explain and justify the status quo as well as the power to make change imaginable and urgent.
A narrative analysis of power encourages us to ask: Which stories define cultural norms? Where did these stories come from? Whose stories were ignored or erased to create these norms? And, most urgently, what new stories can we tell to help create the world we desire? [1][2]
Mindmaps and mindsets
If a mindmap is a cognitive "hathanger" then a mindset are the clothes hanging on the hathanger. Most traditions have mindmaps that have been and are evolving locally from the experiences of the previous generations on what worked and what didn't for them. Afaik, the oldest mindmaps use trees and wheels. And all mindmaps are generalisations in the wind without grounding details if not from there. The adversary grouping of the petty tyrants map is useful for gathering and interpreting data from narratives, questioning and timelines into a framework of possible threats.
- Petty tyrants
- Captivating capital and copyfighting
- Encrypting everything
- Arcane mixing techniques
- Networking concepts
- A typical linux distribution
Methodologies, processes and choreographies
Most processes are adapted to allow for minimalist approaches and to minimalise the risk of unintentionally becoming the petty tyrants we fight [3].
Edge
Getting started with linux
Standing on a hilltop in a thunderstorm on bare feet, wearing wet copper armour, holding a lightning rod and shouting ... bring it on, ye gods and godesses!
We use lawful techniques and tools. And if need be we invent new (GNU and creative commons licensed) techniques and tools [4].
- Installing linux
- Linux applications
- Linux security
- Kinky linux command-line
- Object encryption on linux
- Anonymising your traffic with linux
- Clean up all the things
- Shell scripting
Teacher inside
- Self-dox
- Reconnaissance
- Network exploitation and monitoring
- Reverse engineering
- Roleplay
- Trolling
- Elicitation
- Wordsmithing
- Take control of the tech
- Making our own linux images
Autonomy shaping infrastructure
- For setting up a home server see the Servers Everywhere! section on UnDisConnect
- For setting up a server see the documentation in the Anarcha section on Alexandria
- Linux server security
- Radio
- Libraries
- Meshnets
- Clusternets
Solidarity network
References
- ↑ Harnessing the power of narrative for social change https://www.newtactics.org/conversation/change-story-harnessing-power-narrative-social-change
- ↑ Underminers Chapter Ten – Reclaiming Ourselves http://underminers.org/the-book/chapter-10/
- ↑ Portal 2 Soundtrack Cara Mia (Turret Opera) One Hour https://www.youtube.com/watch?v=wFKfkfCeFj4
- ↑ Portal - 'Still Alive' https://www.youtube.com/watch?v=Y6ljFaKRTrI