Difference between revisions of "Linux applications"
From Gender and Tech Resources
m (→apt) |
m |
||
| (29 intermediate revisions by 2 users not shown) | |||
| Line 1: | Line 1: | ||
| + | [[File:Repository2.jpg|640px|thumb|right|Caek repository]] | ||
| + | |||
Linux distributions include great software by default and their repositories. And with so many flavours of linux, finding the right application for getting things done can be tough. Hence my proposal to share interesting apps. The page was kicked off with a short explanation on installing, and a few categories. Add your 2 cents! If a fitting category is not available, create it. | Linux distributions include great software by default and their repositories. And with so many flavours of linux, finding the right application for getting things done can be tough. Hence my proposal to share interesting apps. The page was kicked off with a short explanation on installing, and a few categories. Add your 2 cents! If a fitting category is not available, create it. | ||
For each application its license is mentioned if found (others will still have to be added). For more on licensing see [[Captivating capital and copyfighting]]. | For each application its license is mentioned if found (others will still have to be added). For more on licensing see [[Captivating capital and copyfighting]]. | ||
| − | |||
| − | |||
| − | |||
There are many ways to install applications, via graphical front-ends and via the command-line. You can use all of them. It used to be a problem when apt-get did not track which packages were automatically installed while aptitude did, but now that both packages share this list, there is no reason to avoid switching back and forth between the two or between one and front-ends related to the other. | There are many ways to install applications, via graphical front-ends and via the command-line. You can use all of them. It used to be a problem when apt-get did not track which packages were automatically installed while aptitude did, but now that both packages share this list, there is no reason to avoid switching back and forth between the two or between one and front-ends related to the other. | ||
| − | + | == Graphical front-ends == | |
| − | + | ||
The Gnome PackageKit is one of two graphical package managers installed out of the box if and when you installed GNOME as desktop manager in Ubuntu. In older GNOME you can access it from the menu at ''Applications > System Tools > Add/Remove Software. ''PackageKit is designed to unify all the software graphical tools used in different distributions. It abstracts the various underlying package management technologies like yum, apt, smart etc. and provides unified graphical and command line frontends. | The Gnome PackageKit is one of two graphical package managers installed out of the box if and when you installed GNOME as desktop manager in Ubuntu. In older GNOME you can access it from the menu at ''Applications > System Tools > Add/Remove Software. ''PackageKit is designed to unify all the software graphical tools used in different distributions. It abstracts the various underlying package management technologies like yum, apt, smart etc. and provides unified graphical and command line frontends. | ||
| Line 25: | Line 23: | ||
[[File:Aptitude.png|640px||thumb|center]] | [[File:Aptitude.png|640px||thumb|center]] | ||
| − | + | == Command-line based package managers and apt front-ends == | |
In debian-based distributions, installing and managing software from the command-line can be done with <em>apt-get</em> and other components of the Advanced Packaging Tool (APT). For example, to install an application like Ubuntu’s Software Center, you can do: | In debian-based distributions, installing and managing software from the command-line can be done with <em>apt-get</em> and other components of the Advanced Packaging Tool (APT). For example, to install an application like Ubuntu’s Software Center, you can do: | ||
| Line 32: | Line 30: | ||
You can find out more by reading the man page. Just type ''man apt-get'' on the command-line. It's a handy tool if you know the exact package name of what you want to install and don't want to spend time clicking through a GUI to get it. | You can find out more by reading the man page. Just type ''man apt-get'' on the command-line. It's a handy tool if you know the exact package name of what you want to install and don't want to spend time clicking through a GUI to get it. | ||
| − | Some noteworthy alternatives to apt-get are cupt | + | Some noteworthy alternatives to apt-get are cupt, wajig and xbps. Cupt wraps several tools including apt-get, and wajig is a (partial) APT reimplementation. Xbps was written from scratch. |
| + | === xbps === | ||
| + | The X Binary Package System (in short XBPS) is a binary package system designed and implemented from scratch. Its goal is to be fast, easy to use, bug-free, featureful and portable as much as possible. The XBPS code is totally compatible with POSIX/SUSv2/C99 standards, and released with a Simplified BSD license (2 clause). There is a well documented API provided by the XBPS Library that is the basis for its frontends to handle binary packages and repositories. It is used in the voidlinux distro. | ||
| + | https://github.com/voidlinux/xbps/blob/master/README.md | ||
=== apt === | === apt === | ||
Apt makes collection of software available to the user and does the dirty work of downloading all the required packages and installing them by calling dpkg in the correct order to respect the dependencies. Apt is a library and several frontends have been developed on top of that library, of which apt-get is one. I not works, check internet connection. | Apt makes collection of software available to the user and does the dirty work of downloading all the required packages and installing them by calling dpkg in the correct order to respect the dependencies. Apt is a library and several frontends have been developed on top of that library, of which apt-get is one. I not works, check internet connection. | ||
| Line 63: | Line 64: | ||
For doing a "dry run" of a procedure in order to get an idea of what an action will do, you can pass the <code>-s</code> ('''s'''imulate) flag: | For doing a "dry run" of a procedure in order to get an idea of what an action will do, you can pass the <code>-s</code> ('''s'''imulate) flag: | ||
| − | $ sudo apt-get install -s | + | $ sudo apt-get install -s packagename |
=== dpkg === | === dpkg === | ||
| − | Package managers like apt-get, aptitude, synaptic, and the Ubuntu Software Center are all just front-ends to either dpkg or apt, which is in itself a front-end to dpkg. This is the low-level tool that takes a .deb file and extracts its content on the disk, or that takes the name of a package to remove the associated files, | + | Package managers like apt-get, aptitude, synaptic, and the Ubuntu Software Center are all just front-ends to either dpkg or apt, which is in itself a front-end to dpkg. This is the low-level tool that takes a .deb file and extracts its content on the disk, or that takes the name of a package to remove the associated files, etc. |
| − | + | For installing a <code>.deb</code> package use the command with <code>-i</code> option: | |
| − | + | # dpkg -i packagename.deb | |
| − | + | ||
| − | + | Listing all installed packages: | |
| − | + | ||
| − | + | # dpkg -l | |
| − | + | ||
| − | + | For removing a package (but not the configuration files): | |
| − | + | ||
| + | # dpkg -r packagename | ||
| + | |||
| + | For removing both configuration and package files: | ||
| + | |||
| + | # dpkg -p packagename | ||
| + | |||
| + | For showing whether a deb package is installed or not: | ||
| + | |||
| + | # dpkg -s packagename | ||
| + | |||
| + | == Verification with checksums == | ||
| + | For more on checksum concepts see [[Encrypting_everything#Checksums|encrypting everything: checksums]]. | ||
| + | |||
| + | === Package managers === | ||
| + | Integrity checks are integrated in debian package managers. Never ever continue with installation if you get a: | ||
| − | + | WARNING: The following packages cannot be authenticated! | |
| + | 0. It may be that your system is set to use a proxy server for a network you are not connected to. Set your Network Proxy method to None and Apply System Wide, and check if that helped. | ||
| + | |||
| + | 1. Check repositories are not corrupted in <code>/etc/apt/sources.list</code>. Try again. | ||
| + | |||
| + | 2. Check GPG keys (apt-key) | ||
| + | # apt-key list | ||
| + | 3. Update the local keyring with the keyring of archive keys and remove from the keyring the archive keys which are no longer valid: | ||
| + | |||
| + | <pre># apt-key update | ||
| + | # apt-get update</pre> | ||
| + | |||
| + | 4. If still not works, reinstall your archive-keyring. | ||
| + | |||
| + | # aptitude reinstall [distro]-archive-keyring | ||
| + | |||
| + | * Kali Keyring – kali-archive-keyring | ||
| + | * Debian Keyring – debian-archive-keyring | ||
| + | * Ubuntu Keyring – ubuntu-archive-keyring | ||
| + | 5. Still not works? Contact us on IRC. | ||
| + | |||
| + | === Download software === | ||
| + | And when downloading software, .iso's and .deb's and the like, download the xxxsum (choose from what is available) as well as the software and check. For example do: | ||
| + | |||
| + | $ md5sum some-file.iso | ||
| + | |||
| + | or | ||
| + | |||
| + | $ sha256sum some-file.iso | ||
| + | |||
| + | and compare the output from the command with the key listed in the associated md5 or sha256 file. | ||
| + | |||
| + | == Compiling source code == | ||
Source code usually comes in the form of compressed tar files (.tar.gz or .tar.bz2 extensions). Tools used for packing the source code into these tar balls are <code>tar</code> (used for combining multiple files into one) and <code>gzip</code> or <code>bzip2</code> (used for compression). To fetch the source code tarball for a particular software you need to know the URL to the tarball. | Source code usually comes in the form of compressed tar files (.tar.gz or .tar.bz2 extensions). Tools used for packing the source code into these tar balls are <code>tar</code> (used for combining multiple files into one) and <code>gzip</code> or <code>bzip2</code> (used for compression). To fetch the source code tarball for a particular software you need to know the URL to the tarball. | ||
| Line 89: | Line 137: | ||
3. Unpack the tarball in order to get access to the source code and other files: | 3. Unpack the tarball in order to get access to the source code and other files: | ||
| − | $ tar - | + | $ tar -zxvf tarballname.tar.gz |
or | or | ||
| − | $ tar - | + | $ tar -zxvf tarballname.tar.bz2 |
4. If present, the documentation in the extracted directories provides information about the software, changes since last version, links to more documentation, information regrading the author of the software, steps for compilation and installation of software etc. Name of the files (and case) may differ but usually the information is divided into two files, a "Readme" and an "Install". The last covers all the information required for compilation and installation, and all the other information is covered in the "Readme" file. | 4. If present, the documentation in the extracted directories provides information about the software, changes since last version, links to more documentation, information regrading the author of the software, steps for compilation and installation of software etc. Name of the files (and case) may differ but usually the information is divided into two files, a "Readme" and an "Install". The last covers all the information required for compilation and installation, and all the other information is covered in the "Readme" file. | ||
| Line 117: | Line 165: | ||
8. Remove the directory created while unpacking the software tarball. | 8. Remove the directory created while unpacking the software tarball. | ||
| − | == | + | == Stealth install of applications == |
| + | * Launch Synaptic on the off-line computer you wish to install software packages on. | ||
| + | * Mark the packages you wish to install. | ||
| + | * Choose File-> Generate package download script. | ||
| + | * Save the script to your USB stick. | ||
| + | * Take the USB stick to an online linux computer and run the script on the USB stick. It will download only the packages required by the offline computer to the USB stick. | ||
| + | * Insert the USB stick into the offline computer. | ||
| + | * Launch Synaptic and click on File-> Add downloaded packages | ||
| + | * Select the directory on your USB stick containing the downloaded *.deb files and click Open. The packages will be installed. | ||
| + | == Transferring application data to another distribution == <!--T:155--> | ||
| + | If you set up a separate <code>/home</code> during partitioning for your current system, when you perform the new installation, you can tell the installer to reformat the first partition <code>/</code> (to start from scratch), but leave the second partition alone and just mount it again to <code>/home</code>. Then, all you need to do is make sure that you set up the same username and password as before, and everything should be back to the way it was (later you can change them). | ||
| + | |||
| + | If you did not, go into <code>/home/user</code> and backup all personal and application data on for example, an external disk. Your personal files are probably all visible and easily copied. For the application data, use the View menu in your file manager to set Show hidden files and copy all <code>.application</code> directories you wish to keep. Mind dependencies. Especially keys. Those may need exporting and copy too. Then after installing the other distro or re-installing or upgrading the existing linux, put the <code>.application</code> directories in the new <code>/home/user</code> directory. | ||
| + | |||
| + | The only thing you’d still have to do is reinstall your applications. For many applications, the settings will be picked up on. Import the exported keys. | ||
| + | |||
| + | Word of warning: For some switches, like from Ubuntu to Fedora, this (either way) may not work well, even if both are using Gnome. Incompatabilities may arise. Good, that way we have to "sort it out" and dive into the peculiarities of the new distro immediately. :) Also, configurations in system files are not transferred (unless you thought of those and your external disk had enough space). | ||
| + | |||
| + | == Shell == | ||
Computers understand the language of zeros and ones known as binary language. If not familiar with number conversions, a decent tutorial can be found in http://www.cstutoringcenter.com/tutorials/general/convert.php In the early days of computing, instructions were provided using binary language, which is difficult for all of us to read and write. In linux, the shell accepts human readable commands and translates them into something the kernel can read and process. | Computers understand the language of zeros and ones known as binary language. If not familiar with number conversions, a decent tutorial can be found in http://www.cstutoringcenter.com/tutorials/general/convert.php In the early days of computing, instructions were provided using binary language, which is difficult for all of us to read and write. In linux, the shell accepts human readable commands and translates them into something the kernel can read and process. | ||
| Line 135: | Line 201: | ||
=== Shells === | === Shells === | ||
==== zsh ==== | ==== zsh ==== | ||
| − | |||
Zsh is a shell designed for interactive use, although it is also a powerful scripting language. Many of the useful features of bash, ksh, and tcsh were incorporated into zsh; many original features were added. The introductory document details some of the unique features of zsh. It assumes basic knowledge of the standard UNIX shells; the intent is to show a reader already familiar with one of the other major shells what makes zsh more useful or more powerful. This document is not at all comprehensive; read the manual entry for a description of the shell that is complete, concise and up-to-date, although somewhat overwhelming and devoid of examples. Alternatively, the user guide offers wordy explanations of many of the shell's features. | Zsh is a shell designed for interactive use, although it is also a powerful scripting language. Many of the useful features of bash, ksh, and tcsh were incorporated into zsh; many original features were added. The introductory document details some of the unique features of zsh. It assumes basic knowledge of the standard UNIX shells; the intent is to show a reader already familiar with one of the other major shells what makes zsh more useful or more powerful. This document is not at all comprehensive; read the manual entry for a description of the shell that is complete, concise and up-to-date, although somewhat overwhelming and devoid of examples. Alternatively, the user guide offers wordy explanations of many of the shell's features. | ||
| Line 144: | Line 209: | ||
== Graphical environment == | == Graphical environment == | ||
| − | |||
From the bottom up: | From the bottom up: | ||
| − | |||
* Xorg, XFree86 and X11 are display servers https://en.wikipedia.org/wiki/Display_server. This creates the graphical environment. | * Xorg, XFree86 and X11 are display servers https://en.wikipedia.org/wiki/Display_server. This creates the graphical environment. | ||
* [gkxsw]dm, lxdm, lightdm and nodm are display managers alias login managers https://wiki.debian.org/DisplayManager. This is the first X program run by the system if the system (not the user) is starting X and allows you to log on to the local system, or network systems. | * [gkxsw]dm, lxdm, lightdm and nodm are display managers alias login managers https://wiki.debian.org/DisplayManager. This is the first X program run by the system if the system (not the user) is starting X and allows you to log on to the local system, or network systems. | ||
| Line 156: | Line 219: | ||
=== Window managers === | === Window managers === | ||
| − | |||
==== openbox ==== | ==== openbox ==== | ||
Openbox is included in most popular linux distributions. It can be run within GNOME and KDE. And can also be used without a desktop environment (the lightweight approach). You can install additional features yourself, making it very customisable. It does not work well straight out of the box. You will probably need to install tools for power mangement, networking, managing displays, etc. Openbox comes with a default autostart which sets up an environment for both GNOME and KDE applications to run properly in (if you have them installed), as well as providing support for SCIM language input. See the autostart documentation for more details on setting it up. It is excellent for spending some experimentation time on, gaining insights in how window managers work and how else they could work. | Openbox is included in most popular linux distributions. It can be run within GNOME and KDE. And can also be used without a desktop environment (the lightweight approach). You can install additional features yourself, making it very customisable. It does not work well straight out of the box. You will probably need to install tools for power mangement, networking, managing displays, etc. Openbox comes with a default autostart which sets up an environment for both GNOME and KDE applications to run properly in (if you have them installed), as well as providing support for SCIM language input. See the autostart documentation for more details on setting it up. It is excellent for spending some experimentation time on, gaining insights in how window managers work and how else they could work. | ||
| Line 165: | Line 227: | ||
==== awesome ==== | ==== awesome ==== | ||
| − | |||
Awesome (''GNU GPLv2'') is a configurable framework window manager for X. It is primarly targeted at power users, developers and any people dealing with every day computing tasks and who want to have fine-grained control on their graphical environment using the Lua programming language. | Awesome (''GNU GPLv2'') is a configurable framework window manager for X. It is primarly targeted at power users, developers and any people dealing with every day computing tasks and who want to have fine-grained control on their graphical environment using the Lua programming language. | ||
| Line 173: | Line 234: | ||
=== Terminal emulator managers === | === Terminal emulator managers === | ||
| − | |||
==== terminator ==== | ==== terminator ==== | ||
| − | |||
Terminator (GPL-2.0+) is a useful tool for arranging terminals, inspired by programs such as gnome-multi-term, quadkonsole, etc. in that the main focus is arranging terminals in grids (tabs is the most common default method, which Terminator also supports). | Terminator (GPL-2.0+) is a useful tool for arranging terminals, inspired by programs such as gnome-multi-term, quadkonsole, etc. in that the main focus is arranging terminals in grids (tabs is the most common default method, which Terminator also supports). | ||
| Line 182: | Line 241: | ||
==== tmux ==== | ==== tmux ==== | ||
| − | |||
tmux is a terminal multiplexer and lets you switch easily between several programs in one terminal, detach them (they keep running in the background) and reattach them to a different terminal. | tmux is a terminal multiplexer and lets you switch easily between several programs in one terminal, detach them (they keep running in the background) and reattach them to a different terminal. | ||
| Line 189: | Line 247: | ||
=== GUI-based file managers === | === GUI-based file managers === | ||
| − | |||
==== xfe ==== | ==== xfe ==== | ||
| − | |||
X File Explorer (Xfe) is an M$-Explorer or Commander like file manager for X. It is based on the popular, but discontinued, X Win Commander, originally developed by Maxim Baranov. Xfe aims to be the file manager of choice for all light thinking Unix addicts! By default it presents a traditional tree view on the left and file panel on the right, but three other modes are available -- two panels, tree and two panels, or a single panel. ''Open With'' and ''Associate'' options are available from the right-click menu. Although it does not have a lot of the advanced features of Konqueror or Nautilus, it should be more than sufficient for the average user. Its speed and familiarity make it a good choice for older systems, newer users, or those of us who'd run filer.exe under Wine if it could handle file permissions. | X File Explorer (Xfe) is an M$-Explorer or Commander like file manager for X. It is based on the popular, but discontinued, X Win Commander, originally developed by Maxim Baranov. Xfe aims to be the file manager of choice for all light thinking Unix addicts! By default it presents a traditional tree view on the left and file panel on the right, but three other modes are available -- two panels, tree and two panels, or a single panel. ''Open With'' and ''Associate'' options are available from the right-click menu. Although it does not have a lot of the advanced features of Konqueror or Nautilus, it should be more than sufficient for the average user. Its speed and familiarity make it a good choice for older systems, newer users, or those of us who'd run filer.exe under Wine if it could handle file permissions. | ||
| Line 197: | Line 253: | ||
==== gentoo ==== | ==== gentoo ==== | ||
| − | |||
Gentoo is the GTK+ file manager (the name is not related to the Gentoo linux distribution) using a two-pane layout with icon associations for most file extensions. Gentoo also relies on a button bar, located below the file panes, for most operations, but each button may have a secondary function, accessed from the middle mouse button. A second, smaller button bar to the left provides shortcuts to specific directories. The configuration menu is not very extensive, and you can change options with the mouse. Gentoo also provides click-to-sort functionality in the file panes, mount and unmount capabilities, and display of file permissions by color. You can add and edit buttons and give them a specific color and tool tip. | Gentoo is the GTK+ file manager (the name is not related to the Gentoo linux distribution) using a two-pane layout with icon associations for most file extensions. Gentoo also relies on a button bar, located below the file panes, for most operations, but each button may have a secondary function, accessed from the middle mouse button. A second, smaller button bar to the left provides shortcuts to specific directories. The configuration menu is not very extensive, and you can change options with the mouse. Gentoo also provides click-to-sort functionality in the file panes, mount and unmount capabilities, and display of file permissions by color. You can add and edit buttons and give them a specific color and tool tip. | ||
| Line 203: | Line 258: | ||
==== gcmd ==== | ==== gcmd ==== | ||
| − | |||
GNOME Commander offers a small footprint and a polished GUI. It provides the more typical tool bar and menu system, in addition to mapping buttons to each function key. It also provides a command history, capacity for multiple predefined FTP sessions, filesearch, advanced rename tool - allowing for quick renaming of multiple files using regular expressions, counters, and case matching. A compact, polished file manager, especially suitable for those running the GNOME desktop. | GNOME Commander offers a small footprint and a polished GUI. It provides the more typical tool bar and menu system, in addition to mapping buttons to each function key. It also provides a command history, capacity for multiple predefined FTP sessions, filesearch, advanced rename tool - allowing for quick renaming of multiple files using regular expressions, counters, and case matching. A compact, polished file manager, especially suitable for those running the GNOME desktop. | ||
| Line 209: | Line 263: | ||
=== Desktop file managers === | === Desktop file managers === | ||
| − | |||
==== spacefm ==== | ==== spacefm ==== | ||
| − | |||
SpaceFM is a multi-panel tabbed file and desktop manager for Linux with built-in VFS, udev- or HAL-based device manager, customisable menu system, and bash integration. SpaceFM aims to provide a stable, capable file manager with significant customisation capabilities. SpaceFM & udevil '''can be used completely without systemd, consolekit, policykit, dbus, udisks, gvfs & fuse''' (although it can coexist with any of these). | SpaceFM is a multi-panel tabbed file and desktop manager for Linux with built-in VFS, udev- or HAL-based device manager, customisable menu system, and bash integration. SpaceFM aims to provide a stable, capable file manager with significant customisation capabilities. SpaceFM & udevil '''can be used completely without systemd, consolekit, policykit, dbus, udisks, gvfs & fuse''' (although it can coexist with any of these). | ||
| Line 217: | Line 269: | ||
== System tools == | == System tools == | ||
| − | |||
=== System monitoring === | === System monitoring === | ||
| − | |||
==== conky ==== | ==== conky ==== | ||
| − | |||
Conky is a free, light-weight system monitor for X, that displays any information on your desktop. Conky is licensed under the ''GPL'' and runs on Linux and BSD. | Conky is a free, light-weight system monitor for X, that displays any information on your desktop. Conky is licensed under the ''GPL'' and runs on Linux and BSD. | ||
| Line 227: | Line 276: | ||
* Documentation: http://conky.sourceforge.net/documentation.html | * Documentation: http://conky.sourceforge.net/documentation.html | ||
| − | == | + | == Research == |
| + | === Storing information === | ||
| + | Only use those fitting your desktop manager, or else you'll end up with a spaghetti distro. | ||
| + | ==== Basket (KDE) ==== | ||
| + | * Website http://basket.kde.org/ | ||
| − | === | + | ==== Tomboy (GNOME) ==== |
| + | * Website https://github.com/GNOME/tomboy | ||
| + | ==== KeepNote ==== | ||
| + | Windows, Linux, and MacOS X | ||
| − | + | * Website http://keepnote.org/ | |
| + | == Security applications == | ||
| + | === Anti-malware === | ||
| + | ==== rkhunter ==== | ||
Rootkit Hunter (GNU GPL) is a Unix-based tool that scans for rootkits, backdoors and possible local exploits. Specifically, rkhunter is a shell script which carries out various checks on the local system to try and detect known rootkits and malware. It also performs checks to see if commands have been modified, if the system startup files have been modified, and various checks on the network interfaces, including checks for listening applications. rkhunter has been written to be as generic as possible, and so should run on most Linux and UNIX systems. It is provided with some support scripts should certain commands be missing from the system, and some of these are Perl scripts. | Rootkit Hunter (GNU GPL) is a Unix-based tool that scans for rootkits, backdoors and possible local exploits. Specifically, rkhunter is a shell script which carries out various checks on the local system to try and detect known rootkits and malware. It also performs checks to see if commands have been modified, if the system startup files have been modified, and various checks on the network interfaces, including checks for listening applications. rkhunter has been written to be as generic as possible, and so should run on most Linux and UNIX systems. It is provided with some support scripts should certain commands be missing from the system, and some of these are Perl scripts. | ||
| Line 241: | Line 300: | ||
==== chrootkit ==== | ==== chrootkit ==== | ||
| − | |||
chkrootkit (Free software) is a tool to locally check for signs of a rootkit. It tests the following applications: aliens, asp, bindshell, lkm, rexedcs, sniffer, w55808, wted, scalper, slapper, z2, chkutmp, amd, basename, biff, chfn, chsh, cron, crontab, date, du, dirname, echo, egrep, env, find, fingerd, gpm, grep, hdparm, su, ifconfig, inetd, inetdconf, identd, init, killall, ldsopreload, login, ls, lsof, mail, mingetty, netstat, named, passwd, pidof, pop2, pop3, ps, pstree, rpcinfo, rlogind, rshd, slogin, sendmail, sshd, syslogd, tar, tcpd, tcpdump, top, telnetd, timed, traceroute, vdir, w, and write. | chkrootkit (Free software) is a tool to locally check for signs of a rootkit. It tests the following applications: aliens, asp, bindshell, lkm, rexedcs, sniffer, w55808, wted, scalper, slapper, z2, chkutmp, amd, basename, biff, chfn, chsh, cron, crontab, date, du, dirname, echo, egrep, env, find, fingerd, gpm, grep, hdparm, su, ifconfig, inetd, inetdconf, identd, init, killall, ldsopreload, login, ls, lsof, mail, mingetty, netstat, named, passwd, pidof, pop2, pop3, ps, pstree, rpcinfo, rlogind, rshd, slogin, sendmail, sshd, syslogd, tar, tcpd, tcpdump, top, telnetd, timed, traceroute, vdir, w, and write. | ||
| Line 250: | Line 308: | ||
=== Encryption === | === Encryption === | ||
| − | |||
==== gnupg ==== | ==== gnupg ==== | ||
GnuPG (GNU GPL v3+) stands for GNU Privacy Guard and is a tool for secure communication and data storage. The software has two main uses. The first is to encrypt data to ensure its privacy. The second is to "sign" data so that others can determine it is authentic and unmodified. It includes an advanced key management facility and is compliant with the proposed OpenPGP Internet standard as described in RFC 2440. GnuPG is a command line tool with features for easy integration with other applications. The default public key algorithms are DSA and Elgamal, but RSA is also supported. Symmetric algorithms available are AES (with 128, 192, and 256 bit keys), 3DES, Blowfish, CAST5 and Twofish. Digest algorithms available are MD5, RIPEMD/160, SHA-1, SHA-256, SHA-384, and SHA-512. Compression algorithms available are ZIP, ZLIB, and BZIP2 (with libbz2 installed). | GnuPG (GNU GPL v3+) stands for GNU Privacy Guard and is a tool for secure communication and data storage. The software has two main uses. The first is to encrypt data to ensure its privacy. The second is to "sign" data so that others can determine it is authentic and unmodified. It includes an advanced key management facility and is compliant with the proposed OpenPGP Internet standard as described in RFC 2440. GnuPG is a command line tool with features for easy integration with other applications. The default public key algorithms are DSA and Elgamal, but RSA is also supported. Symmetric algorithms available are AES (with 128, 192, and 256 bit keys), 3DES, Blowfish, CAST5 and Twofish. Digest algorithms available are MD5, RIPEMD/160, SHA-1, SHA-256, SHA-384, and SHA-512. Compression algorithms available are ZIP, ZLIB, and BZIP2 (with libbz2 installed). | ||
| Line 282: | Line 339: | ||
==== veracrypt ==== | ==== veracrypt ==== | ||
| − | |||
VeraCrypt is disk encryption software forked from the discontinued TrueCrypt software. VeraCrypt adds enhanced security to the algorithms used for system and partitions encryption, and solves many vulnerabilities and security issues found in TrueCrypt. | VeraCrypt is disk encryption software forked from the discontinued TrueCrypt software. VeraCrypt adds enhanced security to the algorithms used for system and partitions encryption, and solves many vulnerabilities and security issues found in TrueCrypt. | ||
| Line 288: | Line 344: | ||
* Documentation: https://veracrypt.codeplex.com/documentation | * Documentation: https://veracrypt.codeplex.com/documentation | ||
==== ciphershed ==== | ==== ciphershed ==== | ||
| − | |||
CipherShed (will carry an OSI approved license (probably either Apache or BSD)) is free (as in free-of-charge and free-speech) encryption software and was started in June 2014 as a response to the end of life announcement for TrueCrypt. As of October 2014 CipherShed source code is hosted at GitHub. CipherShed is a program that can be used to create encrypted files or encrypt entire drives (including USB flash drives and external HDDs). There’s no complicated commands or knowledge required; a simple wizard guides you step-by-step through every process. After creating an encrypted file or disk drive, the encrypted volume is mounted through CipherShed. The mounted volume shows up as a regular disk that can be read and written to on-the-fly. The encryption is transparent to the operating system and any programs. When finished, the volume can be unmounted, and stored or transported elsewhere, fully secured. Encryption volumes can be moved from OS-to-OS (eg, Windows to Mac) with full compatibility. | CipherShed (will carry an OSI approved license (probably either Apache or BSD)) is free (as in free-of-charge and free-speech) encryption software and was started in June 2014 as a response to the end of life announcement for TrueCrypt. As of October 2014 CipherShed source code is hosted at GitHub. CipherShed is a program that can be used to create encrypted files or encrypt entire drives (including USB flash drives and external HDDs). There’s no complicated commands or knowledge required; a simple wizard guides you step-by-step through every process. After creating an encrypted file or disk drive, the encrypted volume is mounted through CipherShed. The mounted volume shows up as a regular disk that can be read and written to on-the-fly. The encryption is transparent to the operating system and any programs. When finished, the volume can be unmounted, and stored or transported elsewhere, fully secured. Encryption volumes can be moved from OS-to-OS (eg, Windows to Mac) with full compatibility. | ||
| Line 295: | Line 350: | ||
=== Firewalls === | === Firewalls === | ||
| − | |||
==== gufw and ufw ==== | ==== gufw and ufw ==== | ||
Gufw (''GNU GPL v3'') is for users bamboozled by firewalls. It has an easy to use interface for setting up inbound and outbound traffic rules for apps/services and ports. It is designed for beginners. Gufw is a GUI front-end to <code>ufw</code>, which is in itself a front-end to <code>netfilter</code> and <code>iptables</code> | Gufw (''GNU GPL v3'') is for users bamboozled by firewalls. It has an easy to use interface for setting up inbound and outbound traffic rules for apps/services and ports. It is designed for beginners. Gufw is a GUI front-end to <code>ufw</code>, which is in itself a front-end to <code>netfilter</code> and <code>iptables</code> | ||
| Line 312: | Line 366: | ||
=== Intrusion detection === | === Intrusion detection === | ||
| + | One of the key differences between Tripwire and Aide is their commercial status. Tripwire was originally a free, open source product and is now a commercial product but a free version (branched in 2000) is still being developed at http://sourceforge.net/projects/tripwire/. Aide is entirely open source and licensed via the GPL and much, much easier in its configuration. Tripwire offers extended features that make it more secure than Aide, but storing aide databases on an encrypted filesystem on another machine (or an external drive) can be considered good enough to not need tripwire's extended feature(s) and opt for aide instead. Not that you can't sign the databases AND put them on another machine or external drive. | ||
| + | |||
==== aide ==== | ==== aide ==== | ||
| − | + | The Advanced Intrusion Detection Environment (''GPL''), for short ''aide'', is a file integrity checker (FIA). It creates a database from the regular expression rules that it finds from the config file(s). Once this database is initialized it can be used to verify the integrity of the files. It has several message digest algorithms (md5, sha1, rmd160, tiger, crc32, sha256, sha512, whirlpool (additionally with libmhash: gost, haval, crc32b)) that are used to check the integrity of the file. All of the usual file attributes (File type, Permissions, Inode, Uid, Gid, Link name, Size, Block count, Number of links, Mtime, Ctime and Atime) can also be checked for inconsistencies. It can read databases from older or newer versions. | |
| − | The Advanced Intrusion Detection Environment (''GPL''), | + | |
* Website: http://aide.sourceforge.net | * Website: http://aide.sourceforge.net | ||
* Manual: http://aide.sourceforge.net/stable/manual.html | * Manual: http://aide.sourceforge.net/stable/manual.html | ||
* Available from repository. | * Available from repository. | ||
| + | * Example install and configuration of aide on debian: [[Linux security#Installing intrusion detection|Linux security: Installing intrusion detection]] | ||
| − | === | + | ==== tripwire ==== |
| + | Open Source Tripwire is a free software security and data integrity tool useful for monitoring and alerting on specific file change(s) on a range of systems. Open Source Tripwire functions as a host-based intrusion detection system. It is suitable for monitoring a small number of servers where centralized control and reporting is not needed and professional support is not a requirement. | ||
| + | * Website: http://www.tripwire.com | ||
| + | * Mailinglists: http://sourceforge.net/p/tripwire/mailman/ | ||
| + | * Available from repository. | ||
| + | * Example install and configuration of tripwire on debian: [[Linux security#Installing intrusion detection|Linux security: Installing intrusion detection]] and [[Linux server security#Installing intrusion detection|Linux server security: Installing intrusion detection]] | ||
| + | |||
| + | === Traffic capture === | ||
| + | === Traffic analysis === | ||
==== kismet ==== | ==== kismet ==== | ||
Kismet (''GNU GPL'') is an 802.11 layer2 wireless network detector, sniffer, and intrusion detection system. Kismet will work with any wireless card which supports raw monitoring (rfmon) mode, and can sniff 802.11b, 802.11a, and 802.11g traffic. Kismet identifies networks by passively collecting packets and detecting standard named networks, detecting (and given time, decloaking) hidden networks, and inferring the presence of nonbeaconing networks via data traffic. | Kismet (''GNU GPL'') is an 802.11 layer2 wireless network detector, sniffer, and intrusion detection system. Kismet will work with any wireless card which supports raw monitoring (rfmon) mode, and can sniff 802.11b, 802.11a, and 802.11g traffic. Kismet identifies networks by passively collecting packets and detecting standard named networks, detecting (and given time, decloaking) hidden networks, and inferring the presence of nonbeaconing networks via data traffic. | ||
| Line 330: | Line 394: | ||
* Available from repository. Requirements: Libpcap, GPSD, Imagemagick, Expat, GMP. '''Optional: DBUS''' (but not required) | * Available from repository. Requirements: Libpcap, GPSD, Imagemagick, Expat, GMP. '''Optional: DBUS''' (but not required) | ||
==== wireshark ==== | ==== wireshark ==== | ||
| − | |||
Wireshark (''GNU GPL v2'') is a network packet analyzer. A network packet analyzer captures network packets and tries to display that packet data as detailed as possible. A network packet analyzer can be regarded as a measuring device to examine what's going on inside a network cable, just like a voltmeter is used by an electrician to examine what's going on inside an electric cable (but at a higher level, of course). It is developed and maintained by a global team of protocol experts. It used to be known as Ethereal, and was renamed to Wireshark in May 2006. | Wireshark (''GNU GPL v2'') is a network packet analyzer. A network packet analyzer captures network packets and tries to display that packet data as detailed as possible. A network packet analyzer can be regarded as a measuring device to examine what's going on inside a network cable, just like a voltmeter is used by an electrician to examine what's going on inside an electric cable (but at a higher level, of course). It is developed and maintained by a global team of protocol experts. It used to be known as Ethereal, and was renamed to Wireshark in May 2006. | ||
| Line 339: | Line 402: | ||
=== Packet crafting === | === Packet crafting === | ||
==== hping ==== | ==== hping ==== | ||
| − | |||
Hping3 (''GNU GPL v2'') is a command-line oriented TCP/IP packet assembler/analyser. The interface is inspired from the ping unix command, but hping isn't only able to send ICMP echo requests. It supports TCP, UDP, ICMP and RAW-IP protocols, has a traceroute mode, the ability to send files between a covered channel, and many other features. hping3 can handle fragmentation, and almost arbitrary packet size and content, using the command line interface. | Hping3 (''GNU GPL v2'') is a command-line oriented TCP/IP packet assembler/analyser. The interface is inspired from the ping unix command, but hping isn't only able to send ICMP echo requests. It supports TCP, UDP, ICMP and RAW-IP protocols, has a traceroute mode, the ability to send files between a covered channel, and many other features. hping3 can handle fragmentation, and almost arbitrary packet size and content, using the command line interface. | ||
| Line 347: | Line 409: | ||
==== scapy ==== | ==== scapy ==== | ||
| − | |||
Scapy (''GNU GPL v2'') is a powerful interactive packet manipulation program. It is able to forge or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and replies, etc. It can handle most classical tasks like scanning, tracerouting, probing, unit tests, attacks or network discovery (it can replace hping, 85% of nmap, arpspoof, arp-sk, arping, tcpdump, tethereal, p0f, etc.). | Scapy (''GNU GPL v2'') is a powerful interactive packet manipulation program. It is able to forge or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and replies, etc. It can handle most classical tasks like scanning, tracerouting, probing, unit tests, attacks or network discovery (it can replace hping, 85% of nmap, arpspoof, arp-sk, arping, tcpdump, tethereal, p0f, etc.). | ||
| Line 355: | Line 416: | ||
=== Port scanning === | === Port scanning === | ||
| − | |||
==== ipscan ==== | ==== ipscan ==== | ||
Angry IP Scanner (''GNU GPL v2'') is an open-source and cross-platform network scanner designed to be fast and simple to use. It scans IP addresses and ports. | Angry IP Scanner (''GNU GPL v2'') is an open-source and cross-platform network scanner designed to be fast and simple to use. It scans IP addresses and ports. | ||
| Line 364: | Line 424: | ||
=== Vulnerability scanning === | === Vulnerability scanning === | ||
| − | |||
==== tiger ==== | ==== tiger ==== | ||
| − | |||
Tiger (''GNU GPL'') is a security tool that can be use both as a security audit and intrusion detection system. It is a set of scripts that scan a Un*x system looking for security problems, in the same fashion as Dan Farmer's COPS. It was originally developed to provide a check of UNIX systems on the A&M campus that want to be accessed from off campus (clearance through the packet filter). Unlike other tools, Tiger needs only of POSIX tools and is written entirely in shell language. | Tiger (''GNU GPL'') is a security tool that can be use both as a security audit and intrusion detection system. It is a set of scripts that scan a Un*x system looking for security problems, in the same fashion as Dan Farmer's COPS. It was originally developed to provide a check of UNIX systems on the A&M campus that want to be accessed from off campus (clearance through the packet filter). Unlike other tools, Tiger needs only of POSIX tools and is written entirely in shell language. | ||
| Line 376: | Line 434: | ||
=== Data removal === | === Data removal === | ||
| − | |||
==== bleachbit ==== | ==== bleachbit ==== | ||
| − | |||
BleachBit deletes unnecessary files to free valuable disk space, maintain privacy, and remove junk. It removes cache, Internet history, temporary files, cookies, and broken shortcuts. It handles cleaning of Adobe Reader, Bash, Beagle, Epiphany, Firefox, Flash, GIMP, Google Earth, Java, KDE, OpenOffice.org, Opera, RealPlayer, rpmbuild, Second Life Viewer, VIM, XChat, and more. Beyond simply erasing junk files, BleachBit wipes free disk space (to hide previously deleted files for privacy and to improve compression of images), vacuums Firefox databases (to improve performance without deleting data), and securely shreds arbitrary files. | BleachBit deletes unnecessary files to free valuable disk space, maintain privacy, and remove junk. It removes cache, Internet history, temporary files, cookies, and broken shortcuts. It handles cleaning of Adobe Reader, Bash, Beagle, Epiphany, Firefox, Flash, GIMP, Google Earth, Java, KDE, OpenOffice.org, Opera, RealPlayer, rpmbuild, Second Life Viewer, VIM, XChat, and more. Beyond simply erasing junk files, BleachBit wipes free disk space (to hide previously deleted files for privacy and to improve compression of images), vacuums Firefox databases (to improve performance without deleting data), and securely shreds arbitrary files. | ||
| Line 387: | Line 443: | ||
=== Password management === | === Password management === | ||
| − | |||
==== keepassx ==== | ==== keepassx ==== | ||
| − | |||
KeePassX (''GNU GPL v2'') is a multi-platform port of KeePass, an open source and cross-platform password manager. This utility helps you to manage your passwords in a secure way. You can put all your passwords in one database, which is locked with one master key or a key-disk. This lets users only need to remember one single master password or insert the key-disk to unlock the whole database. The databases are encrypted using the algorithms AES (alias Rijndael) or Twofish using a 256 bit key. KeePassX currently uses same the database file format as the KeePass 1.x (Classic) password manager software for Windows. | KeePassX (''GNU GPL v2'') is a multi-platform port of KeePass, an open source and cross-platform password manager. This utility helps you to manage your passwords in a secure way. You can put all your passwords in one database, which is locked with one master key or a key-disk. This lets users only need to remember one single master password or insert the key-disk to unlock the whole database. The databases are encrypted using the algorithms AES (alias Rijndael) or Twofish using a 256 bit key. KeePassX currently uses same the database file format as the KeePass 1.x (Classic) password manager software for Windows. | ||
| Line 397: | Line 451: | ||
=== VPN === | === VPN === | ||
| − | |||
==== openvpn ==== | ==== openvpn ==== | ||
OpenVPN (GNU GPL v2) is a full-featured virtual private network (VPN) solution accomodating a wide range of configurations, including remote access, site-to-site VPNs, WiFi security, and enterprise-scale remote access solutions with load balancing, failover, and fine-grained access-controls. OpenVPN implements OSI layer 2 or 3 secure network extension using the industry standard SSL/TLS protocol, supports flexible client authentication methods based on certificates, smart cards, and/or 2-factor authentication, and allows user or group-specific access control policies using firewall rules applied to the VPN virtual interface. | OpenVPN (GNU GPL v2) is a full-featured virtual private network (VPN) solution accomodating a wide range of configurations, including remote access, site-to-site VPNs, WiFi security, and enterprise-scale remote access solutions with load balancing, failover, and fine-grained access-controls. OpenVPN implements OSI layer 2 or 3 secure network extension using the industry standard SSL/TLS protocol, supports flexible client authentication methods based on certificates, smart cards, and/or 2-factor authentication, and allows user or group-specific access control policies using firewall rules applied to the VPN virtual interface. | ||
| Line 407: | Line 460: | ||
== Desktop applications == | == Desktop applications == | ||
| − | |||
=== Graphics editors === | === Graphics editors === | ||
| − | |||
==== GIMP ==== | ==== GIMP ==== | ||
| − | |||
The GNU Image Manipulation Program (''GNU GPL v2'') is a freely distributed raster graphic editor for photo retouching, image composition and image authoring. It can be used as a simple paint program, an expert quality photo retouching program, an online batch processing system, a mass production image renderer, an image format converter, etc. It also makes the task of screenshots easy. It is designed to be augmented with plug-ins and extensions. The advanced scripting interface allows simple tasks as well as complex image manipulation procedures to scripted. | The GNU Image Manipulation Program (''GNU GPL v2'') is a freely distributed raster graphic editor for photo retouching, image composition and image authoring. It can be used as a simple paint program, an expert quality photo retouching program, an online batch processing system, a mass production image renderer, an image format converter, etc. It also makes the task of screenshots easy. It is designed to be augmented with plug-ins and extensions. The advanced scripting interface allows simple tasks as well as complex image manipulation procedures to scripted. | ||
| Line 430: | Line 480: | ||
==== Xara Xtreme ==== | ==== Xara Xtreme ==== | ||
| − | |||
Xara (''GPL'') is a general purpose graphics program for Unix platforms including Linux, FreeBSD and (in development) OS X. It is a port of Xara's flagship software package, renowed for being the fastest vector package available, combined with an efficient working environment. May need a bit of tweaking to install. | Xara (''GPL'') is a general purpose graphics program for Unix platforms including Linux, FreeBSD and (in development) OS X. It is a port of Xara's flagship software package, renowed for being the fastest vector package available, combined with an efficient working environment. May need a bit of tweaking to install. | ||
| Line 437: | Line 486: | ||
=== Image processing === | === Image processing === | ||
| − | |||
==== gm ==== | ==== gm ==== | ||
GraphicsMagick (''MIT X11 style license'') provides a collection of tools and libraries which support reading, writing, and manipulating an image in over 88 major formats including important formats like DPX, GIF, JPEG, JPEG-2000, PNG, PDF, PNM, and TIFF. Similar as imagemagick. | GraphicsMagick (''MIT X11 style license'') provides a collection of tools and libraries which support reading, writing, and manipulating an image in over 88 major formats including important formats like DPX, GIF, JPEG, JPEG-2000, PNG, PDF, PNM, and TIFF. Similar as imagemagick. | ||
| Line 445: | Line 493: | ||
== Minimalist applications == | == Minimalist applications == | ||
| − | |||
=== Text editors === | === Text editors === | ||
| − | |||
==== vi and vim ==== | ==== vi and vim ==== | ||
| − | |||
Yes, even if you can't believe it, there are a lot fans of the 30-years-old vi editor (or its more recent, just-15-years-old, best clone & great improvement, vim). No, they are not dinosaurs who don't want to catch up with the times - the community of vi users just keeps growing. Yes, there are definite reasons why the vi/vim editing model is just superior to any other out there. And you don't need to be a Unix whiz to use it, either: vim is available for free for almost any platform out there, and there are plug-ins to get the functionality inside all major IDEs. <ref>Why, oh WHY, do those #?@! nutheads use vi? http://www.viemu.com/a-why-vi-vim.html</ref> | Yes, even if you can't believe it, there are a lot fans of the 30-years-old vi editor (or its more recent, just-15-years-old, best clone & great improvement, vim). No, they are not dinosaurs who don't want to catch up with the times - the community of vi users just keeps growing. Yes, there are definite reasons why the vi/vim editing model is just superior to any other out there. And you don't need to be a Unix whiz to use it, either: vim is available for free for almost any platform out there, and there are plug-ins to get the functionality inside all major IDEs. <ref>Why, oh WHY, do those #?@! nutheads use vi? http://www.viemu.com/a-why-vi-vim.html</ref> | ||
| Line 457: | Line 502: | ||
=== Console-based file managers === | === Console-based file managers === | ||
| − | |||
Servers often boot to run level 3, which provides no X display, but a good file manager can be crucial to administration. | Servers often boot to run level 3, which provides no X display, but a good file manager can be crucial to administration. | ||
==== mc ==== | ==== mc ==== | ||
| − | |||
Midnight Commander is one of the best-known console file managers. Midnight Commander allows you to view two directories, a directory with file attributes, or a directory and file preview at the same time. On curses-based systems file types and permissions are shown by color, but you can specify "slow" and "ASCII-only" display modes from the command line. These are especially valuable for slow connections and on very old systems. Midnight Commander's help system is well-written, and invaluable, as Ctrl and Alt key combinations make up the bulk of functions. Pull-down menus are also available, and some functions are mapped to function keys, listed at the bottom of the display. | Midnight Commander is one of the best-known console file managers. Midnight Commander allows you to view two directories, a directory with file attributes, or a directory and file preview at the same time. On curses-based systems file types and permissions are shown by color, but you can specify "slow" and "ASCII-only" display modes from the command line. These are especially valuable for slow connections and on very old systems. Midnight Commander's help system is well-written, and invaluable, as Ctrl and Alt key combinations make up the bulk of functions. Pull-down menus are also available, and some functions are mapped to function keys, listed at the bottom of the display. | ||
| Line 470: | Line 513: | ||
==== vifm ==== | ==== vifm ==== | ||
| − | |||
Vifm lets you cut with dd, paste with p, and rename a file with cw. Movement keys are the standard <code>vi</code> hjkl, with h and l ascending and descending the directory tree. The right panel toggles between a display of a second directory and file properties. You can call shell commands from the command line with :!, with %f and %F corresponding to highlighted files in the left and right pane. Vifm also mirrors its treatment of bookmarks, visual file selection, and user-defined macros from vi. Most importantly, :help opens an extensive help file with more options. Like Midnight Commander vifm displays file properties by color, and it can set permissions and ownership; unlike Midnight Commander it does not offer file preview, although pressing Enter or l on a file will open it in vi. :apropos brings up a menu of all matching man pages, from which you can invoke man for the selected entry. If you like vi, try vifm. | Vifm lets you cut with dd, paste with p, and rename a file with cw. Movement keys are the standard <code>vi</code> hjkl, with h and l ascending and descending the directory tree. The right panel toggles between a display of a second directory and file properties. You can call shell commands from the command line with :!, with %f and %F corresponding to highlighted files in the left and right pane. Vifm also mirrors its treatment of bookmarks, visual file selection, and user-defined macros from vi. Most importantly, :help opens an extensive help file with more options. Like Midnight Commander vifm displays file properties by color, and it can set permissions and ownership; unlike Midnight Commander it does not offer file preview, although pressing Enter or l on a file will open it in vi. :apropos brings up a menu of all matching man pages, from which you can invoke man for the selected entry. If you like vi, try vifm. | ||
| Line 478: | Line 520: | ||
==== ranger ==== | ==== ranger ==== | ||
| − | |||
Ranger is a terminal based file manager with vi style keybindings and many features including 'rifle' file opener, previewing, tabs, bookmarks, tagging. ranger is not a two pane file manager like mc or vifm, but uses 'miller columns' showing the directory hierarchy (similar to mac os 'finder'). The centre column is active, the left column the higher level directory, and the right column shows either a deeper directory or file information or preview. | Ranger is a terminal based file manager with vi style keybindings and many features including 'rifle' file opener, previewing, tabs, bookmarks, tagging. ranger is not a two pane file manager like mc or vifm, but uses 'miller columns' showing the directory hierarchy (similar to mac os 'finder'). The centre column is active, the left column the higher level directory, and the right column shows either a deeper directory or file information or preview. | ||
| Line 484: | Line 525: | ||
=== Websearch === | === Websearch === | ||
| − | |||
==== surfraw ==== | ==== surfraw ==== | ||
| − | |||
Shell Users' Revolutionary Front Rage Against the Web, surfraw for short, provides a fast unix command line interface to a variety of popular WWW search engines and other artifacts of power. It reclaims google, altavista, babelfish, dejanews, freshmeat, research index, slashdot and many others from the false-prophet, pox-infested heathen lands of html-forms, placing these wonders where they belong, deep in unix heartland, as god loving extensions to the shell. Surfraw abstracts the browser away from input. Doing so lets it get on with what it's good at. Browsing. Interpretation of linguistic forms is handed back to the shell, which is what it, and human beings are good at. Combined with netscape-remote or incremental text browsers, such as lynx, links or w3m, along with screen a surfraw liberateur is capable of navigating speeds that leave GUI tainted idolaters agape with fear and wonder. | Shell Users' Revolutionary Front Rage Against the Web, surfraw for short, provides a fast unix command line interface to a variety of popular WWW search engines and other artifacts of power. It reclaims google, altavista, babelfish, dejanews, freshmeat, research index, slashdot and many others from the false-prophet, pox-infested heathen lands of html-forms, placing these wonders where they belong, deep in unix heartland, as god loving extensions to the shell. Surfraw abstracts the browser away from input. Doing so lets it get on with what it's good at. Browsing. Interpretation of linguistic forms is handed back to the shell, which is what it, and human beings are good at. Combined with netscape-remote or incremental text browsers, such as lynx, links or w3m, along with screen a surfraw liberateur is capable of navigating speeds that leave GUI tainted idolaters agape with fear and wonder. | ||
| Line 495: | Line 534: | ||
==== vimperator firefox extension ==== | ==== vimperator firefox extension ==== | ||
| − | |||
Vimperator is a Firefox browser extension with strong inspiration from the Vim text editor, with a mind towards faster and more efficient browsing. It has similar key bindings and you could call it a modal web browser, as key bindings differ according to which mode you are in. For example, it has a special Hint mode, where you can follow links easily with the keyboard only. Also most functionality is available as commands, typing :back will go back within the current page history, just like hitting the back button in the toolbar. In case you wish to control the web browser without using the mouse. | Vimperator is a Firefox browser extension with strong inspiration from the Vim text editor, with a mind towards faster and more efficient browsing. It has similar key bindings and you could call it a modal web browser, as key bindings differ according to which mode you are in. For example, it has a special Hint mode, where you can follow links easily with the keyboard only. Also most functionality is available as commands, typing :back will go back within the current page history, just like hitting the back button in the toolbar. In case you wish to control the web browser without using the mouse. | ||
| Line 501: | Line 539: | ||
=== Email === | === Email === | ||
| − | |||
==== mutt ==== | ==== mutt ==== | ||
| − | |||
Mutt is a small but very powerful text-based mail client for Unix operating systems. | Mutt is a small but very powerful text-based mail client for Unix operating systems. | ||
| Line 514: | Line 550: | ||
==== mu ==== | ==== mu ==== | ||
| − | |||
With the enormous amounts of e-mail many people gather and the importance of e-mail messages in our daily work-flow, it is very important to be able to quickly deal with all that - in particular, to instantly find that one important e-mail you need right now. For that, mu was created. mu is a tool for dealing with e-mail messages stored in the Maildir-format, on Unix-like systems. mu's main purpose is to help you to find the messages you need, quickly; in addition, it allows you to view messages, extract attachments, create new maildirs,... | With the enormous amounts of e-mail many people gather and the importance of e-mail messages in our daily work-flow, it is very important to be able to quickly deal with all that - in particular, to instantly find that one important e-mail you need right now. For that, mu was created. mu is a tool for dealing with e-mail messages stored in the Maildir-format, on Unix-like systems. mu's main purpose is to help you to find the messages you need, quickly; in addition, it allows you to view messages, extract attachments, create new maildirs,... | ||
| Line 525: | Line 560: | ||
== Library == | == Library == | ||
| − | |||
== Development == | == Development == | ||
| − | |||
=== Development environments === | === Development environments === | ||
| − | |||
==== vagrant ==== | ==== vagrant ==== | ||
| Line 538: | Line 570: | ||
== Server administration == | == Server administration == | ||
| − | |||
=== File managers === | === File managers === | ||
| − | |||
==== sshfs ==== | ==== sshfs ==== | ||
| Line 550: | Line 580: | ||
=== Intrusion detection === | === Intrusion detection === | ||
| + | There are two major types of Intrusion Detection Systems: network-based and host-based. Tripwire is host-based and Snort is a network-based IDS/IPS. Two side of a coin working in tandem. | ||
==== tripwire ==== | ==== tripwire ==== | ||
| Line 559: | Line 590: | ||
==== snort ==== | ==== snort ==== | ||
| − | + | Snort (''GNU GPL v2'') is an open source network intrusion prevention and detection system sing a rule-driven language, which combines the benefits of signature, protocol and anomaly based inspection methods. It can perform real-time traffic analysis, alerting, blocking and packet logging on IP networks. It utilizes a combination of protocol analysis and pattern matching in order to detect anomalies, misuse and attacks. It detects a variety of attacks and probes, such as buffer overflows, stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more. Snort uses a flexible rules language to describe activity that can be considered malicious or anomalous as well as an analysis engine that incorporates a modular plugin architecture. Snort is capable of detecting and responding in real-time, sending alerts, performing session sniping, logging packets, or dropping sessions/packets when deployed in-line. | |
| − | Snort (''GNU GPL v2'') is an open source network intrusion prevention and detection system sing a rule-driven language, which combines the benefits of signature, protocol and anomaly based inspection methods. It can perform real-time traffic analysis, alerting, blocking and packet logging on IP networks. It utilizes a combination of protocol analysis and pattern matching in order to detect | + | |
* Website: http://www.snort.org/ | * Website: http://www.snort.org/ | ||
| Line 585: | Line 615: | ||
=== Traffic analysis === | === Traffic analysis === | ||
| − | |||
==== tcptrace ==== | ==== tcptrace ==== | ||
| Line 596: | Line 625: | ||
=== System tools === | === System tools === | ||
| − | |||
==== ncdu ==== | ==== ncdu ==== | ||
| Line 605: | Line 633: | ||
=== Backups === | === Backups === | ||
| − | |||
==== rsync ==== | ==== rsync ==== | ||
| Line 614: | Line 641: | ||
==== unison ==== | ==== unison ==== | ||
| − | |||
Unison (''GPL v3'') is a file-synchronization tool for OSX, Unix, and Windows. Unison is written in OCaml. It allows two replicas of a collection of files and directories to be stored on different hosts (or different disks on the same host), modified separately, and then brought up to date by propagating the changes in each replica to the other. Unison can run on and synchronize between Windows and many UNIX platforms. Unison requires no root privileges, system access or kernel changes to function. Unison can synchronize changes to files and directories in both directions, on the same machine, or across a network using ssh or a direct socket connection. Transfers are optimised using a version of the rsync protocol, making it ideal for slower links. Unison has a clear and precise specification, and is resilient to failure due to its careful handling of the replicas and its private structures. | Unison (''GPL v3'') is a file-synchronization tool for OSX, Unix, and Windows. Unison is written in OCaml. It allows two replicas of a collection of files and directories to be stored on different hosts (or different disks on the same host), modified separately, and then brought up to date by propagating the changes in each replica to the other. Unison can run on and synchronize between Windows and many UNIX platforms. Unison requires no root privileges, system access or kernel changes to function. Unison can synchronize changes to files and directories in both directions, on the same machine, or across a network using ssh or a direct socket connection. Transfers are optimised using a version of the rsync protocol, making it ideal for slower links. Unison has a clear and precise specification, and is resilient to failure due to its careful handling of the replicas and its private structures. | ||
| Line 622: | Line 648: | ||
== Services == | == Services == | ||
| − | |||
=== Mailing lists === | === Mailing lists === | ||
==== mailman ==== | ==== mailman ==== | ||
| Line 630: | Line 655: | ||
== Related == | == Related == | ||
| − | |||
* [[Installing linux]] | * [[Installing linux]] | ||
* [[Linux security]] | * [[Linux security]] | ||
| Line 640: | Line 664: | ||
== References == | == References == | ||
| + | |||
| + | [[Category:How_To]] | ||
Latest revision as of 09:38, 24 September 2015
Linux distributions include great software by default and their repositories. And with so many flavours of linux, finding the right application for getting things done can be tough. Hence my proposal to share interesting apps. The page was kicked off with a short explanation on installing, and a few categories. Add your 2 cents! If a fitting category is not available, create it.
For each application its license is mentioned if found (others will still have to be added). For more on licensing see Captivating capital and copyfighting.
There are many ways to install applications, via graphical front-ends and via the command-line. You can use all of them. It used to be a problem when apt-get did not track which packages were automatically installed while aptitude did, but now that both packages share this list, there is no reason to avoid switching back and forth between the two or between one and front-ends related to the other.
Contents
- 1 Graphical front-ends
- 2 Command-line based package managers and apt front-ends
- 3 Verification with checksums
- 4 Compiling source code
- 5 Stealth install of applications
- 6 Transferring application data to another distribution
- 7 Shell
- 8 Graphical environment
- 9 System tools
- 10 Research
- 11 Security applications
- 12 Desktop applications
- 13 Minimalist applications
- 14 Library
- 15 Development
- 16 Server administration
- 17 Services
- 18 Related
- 19 References
Graphical front-ends
The Gnome PackageKit is one of two graphical package managers installed out of the box if and when you installed GNOME as desktop manager in Ubuntu. In older GNOME you can access it from the menu at Applications > System Tools > Add/Remove Software. PackageKit is designed to unify all the software graphical tools used in different distributions. It abstracts the various underlying package management technologies like yum, apt, smart etc. and provides unified graphical and command line frontends.
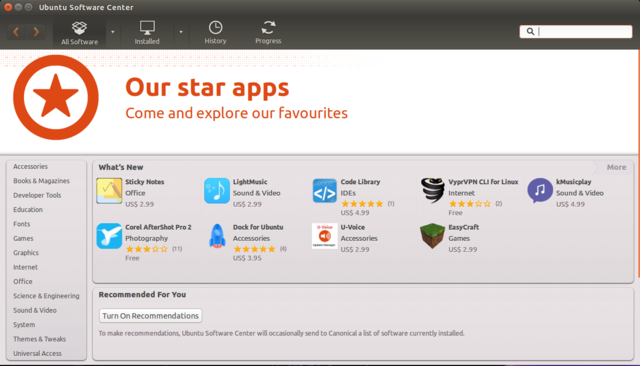
The Software Center is the graphical package manager developed by and default available on Ubuntu. You can access it from Applications > System Tools > Administration > Software Center in GNOME. It is a very high-level, new-user-friendly GUI. It will hide most of the packaging details and will only present installed/available applications. Software is nicely categorized so that, if you're not exactly sure what app you want, you can find what you need quickly. The Software Center also allows you to purchase commercial applications, just in case you wish to roleplay "consumer".
Update-manager is a simple front-end for installing security updates and other daily upgrades (especially useful if you are running testing versions). When the upgrade is too complicated for update-manager, it will suggest to run synaptic.
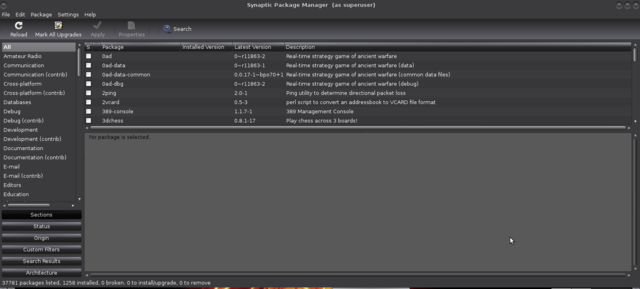
Synaptic used to be the graphical package managers on debian-based distributions. You can start it from the menu: Applications > System Tools > Administration > Synaptic Package Manager in GNOME or System -> Administration -> Synaptic Package Manager in MATE.
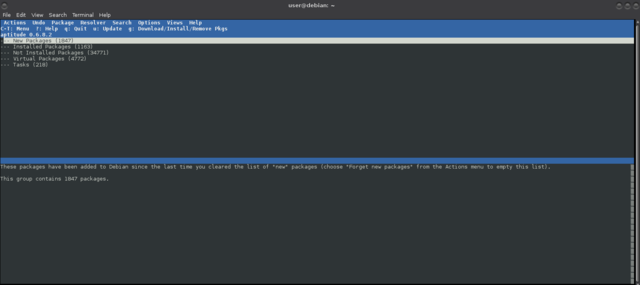
Aptitude is a console-based GUI APT front-end. Run aptitude from the command-line without parameter, and it will start a powerful console-based GUI. Much like synaptic, you can have multiple views of the installed/available packages and mark packages for installation/upgrade/removal/purge before executing everything at once. It is very similar to apt-get and on occasion seems to deal better with odd and unexpected dependency situations. So if you have a problem with that for a particular application, you can try aptitude.
Command-line based package managers and apt front-ends
In debian-based distributions, installing and managing software from the command-line can be done with apt-get and other components of the Advanced Packaging Tool (APT). For example, to install an application like Ubuntu’s Software Center, you can do:
$ sudo apt-get install software-center
You can find out more by reading the man page. Just type man apt-get on the command-line. It's a handy tool if you know the exact package name of what you want to install and don't want to spend time clicking through a GUI to get it.
Some noteworthy alternatives to apt-get are cupt, wajig and xbps. Cupt wraps several tools including apt-get, and wajig is a (partial) APT reimplementation. Xbps was written from scratch.
xbps
The X Binary Package System (in short XBPS) is a binary package system designed and implemented from scratch. Its goal is to be fast, easy to use, bug-free, featureful and portable as much as possible. The XBPS code is totally compatible with POSIX/SUSv2/C99 standards, and released with a Simplified BSD license (2 clause). There is a well documented API provided by the XBPS Library that is the basis for its frontends to handle binary packages and repositories. It is used in the voidlinux distro.
https://github.com/voidlinux/xbps/blob/master/README.md
apt
Apt makes collection of software available to the user and does the dirty work of downloading all the required packages and installing them by calling dpkg in the correct order to respect the dependencies. Apt is a library and several frontends have been developed on top of that library, of which apt-get is one. I not works, check internet connection.
For installing (multiple) packages:
$ sudo apt-get install packagename1 packagename2 packagename3
If a package is already installed, apt will try to upgrade it to the latest version. If it isn't already installed, apt-get will also try to install any software needed to install or run it, the so-called dependencies.
For removing an installed package (except its configuration files):
$ sudo apt-get remove packagename
For cleaning out the configuration files as well as the package:
$ sudo apt-get purge packagename
For resynchronising package index files and upgrading (including security updates):
$ sudo apt-get update $ sudo apt-get upgrade
You can also let apt-get handle changing dependencies with new versions of packages; apt-get has a "smart" conflict resolution system, and it will attempt to upgrade the most important packages at the expense of less important ones if necessary if you use:
$ sudo apt-get update $ sudo apt-get dist-upgrade
For doing a "dry run" of a procedure in order to get an idea of what an action will do, you can pass the -s (simulate) flag:
$ sudo apt-get install -s packagename
dpkg
Package managers like apt-get, aptitude, synaptic, and the Ubuntu Software Center are all just front-ends to either dpkg or apt, which is in itself a front-end to dpkg. This is the low-level tool that takes a .deb file and extracts its content on the disk, or that takes the name of a package to remove the associated files, etc.
For installing a .deb package use the command with -i option:
# dpkg -i packagename.deb
Listing all installed packages:
# dpkg -l
For removing a package (but not the configuration files):
# dpkg -r packagename
For removing both configuration and package files:
# dpkg -p packagename
For showing whether a deb package is installed or not:
# dpkg -s packagename
Verification with checksums
For more on checksum concepts see encrypting everything: checksums.
Package managers
Integrity checks are integrated in debian package managers. Never ever continue with installation if you get a:
WARNING: The following packages cannot be authenticated!
0. It may be that your system is set to use a proxy server for a network you are not connected to. Set your Network Proxy method to None and Apply System Wide, and check if that helped.
1. Check repositories are not corrupted in /etc/apt/sources.list. Try again.
2. Check GPG keys (apt-key)
# apt-key list
3. Update the local keyring with the keyring of archive keys and remove from the keyring the archive keys which are no longer valid:
# apt-key update # apt-get update
4. If still not works, reinstall your archive-keyring.
# aptitude reinstall [distro]-archive-keyring
- Kali Keyring – kali-archive-keyring
- Debian Keyring – debian-archive-keyring
- Ubuntu Keyring – ubuntu-archive-keyring
5. Still not works? Contact us on IRC.
Download software
And when downloading software, .iso's and .deb's and the like, download the xxxsum (choose from what is available) as well as the software and check. For example do:
$ md5sum some-file.iso
or
$ sha256sum some-file.iso
and compare the output from the command with the key listed in the associated md5 or sha256 file.
Compiling source code
Source code usually comes in the form of compressed tar files (.tar.gz or .tar.bz2 extensions). Tools used for packing the source code into these tar balls are tar (used for combining multiple files into one) and gzip or bzip2 (used for compression). To fetch the source code tarball for a particular software you need to know the URL to the tarball.
1. Get the url of the tarball
2. Fetch it using wget or curl (both download it in current directory):
$ wget tarballurl
3. Unpack the tarball in order to get access to the source code and other files:
$ tar -zxvf tarballname.tar.gz
or
$ tar -zxvf tarballname.tar.bz2
4. If present, the documentation in the extracted directories provides information about the software, changes since last version, links to more documentation, information regrading the author of the software, steps for compilation and installation of software etc. Name of the files (and case) may differ but usually the information is divided into two files, a "Readme" and an "Install". The last covers all the information required for compilation and installation, and all the other information is covered in the "Readme" file.
5. Most source code packages also come with a configuration script that can be used for configuring the environment. Again, names may differ, but usually it is named configure and accepts parameters used to control features of the software. The script also makes sure all the tools required for compilation are present in the system. Most have a "help". Try:
$ configure --help
For configuring the build environment, execute the configure script:
$ ./configure
If the script does not crash, throw a fit, or runs off into a black hole, it creates a makefile.
6. The makefile is used in the compilation of the software:
$ make
If compilation encounters a problem an error is thrown on the console. If compilation successfully jumped through all of the hoops, the binaries are created.
7. Install the binaries in the standard paths so they can be invoked from anywhere in the filesystem (this may require root privileges):
# make install
8. Remove the directory created while unpacking the software tarball.
Stealth install of applications
- Launch Synaptic on the off-line computer you wish to install software packages on.
- Mark the packages you wish to install.
- Choose File-> Generate package download script.
- Save the script to your USB stick.
- Take the USB stick to an online linux computer and run the script on the USB stick. It will download only the packages required by the offline computer to the USB stick.
- Insert the USB stick into the offline computer.
- Launch Synaptic and click on File-> Add downloaded packages
- Select the directory on your USB stick containing the downloaded *.deb files and click Open. The packages will be installed.
Transferring application data to another distribution
If you set up a separate /home during partitioning for your current system, when you perform the new installation, you can tell the installer to reformat the first partition / (to start from scratch), but leave the second partition alone and just mount it again to /home. Then, all you need to do is make sure that you set up the same username and password as before, and everything should be back to the way it was (later you can change them).
If you did not, go into /home/user and backup all personal and application data on for example, an external disk. Your personal files are probably all visible and easily copied. For the application data, use the View menu in your file manager to set Show hidden files and copy all .application directories you wish to keep. Mind dependencies. Especially keys. Those may need exporting and copy too. Then after installing the other distro or re-installing or upgrading the existing linux, put the .application directories in the new /home/user directory.
The only thing you’d still have to do is reinstall your applications. For many applications, the settings will be picked up on. Import the exported keys.
Word of warning: For some switches, like from Ubuntu to Fedora, this (either way) may not work well, even if both are using Gnome. Incompatabilities may arise. Good, that way we have to "sort it out" and dive into the peculiarities of the new distro immediately. :) Also, configurations in system files are not transferred (unless you thought of those and your external disk had enough space).
Shell
Computers understand the language of zeros and ones known as binary language. If not familiar with number conversions, a decent tutorial can be found in http://www.cstutoringcenter.com/tutorials/general/convert.php In the early days of computing, instructions were provided using binary language, which is difficult for all of us to read and write. In linux, the shell accepts human readable commands and translates them into something the kernel can read and process.
- The shell is a user program or it is an environment provided for user interaction.
- It is a command language interpreter that executes commands read from the standard input device such as keyboard or from a file.
- The shell gets started when you log in or open a console (terminal).
- Quick and dirty way to execute utilities.
- The shell is not part of system kernel, but uses the system kernel to execute programs, create files etc.
- Common shells available for linux are:
-
bash( Bourne-Again SHell ) - Most common shell in Linux. It's Open Source. -
csh(C SHell) - The C shell's syntax and usage are very similar to the C programming language. -
ksh(Korn SHell) - Created by David Korn at AT & T Bell Labs. The Korn Shell also was the base for the POSIX Shell standard specifications. -
tcsh- an enhanced but completely compatible version of the Berkeley UNIX C shell (CSH).
-
Each shell does the same job, but each understands different command syntax and provides different built-in functions. The Kinky linux command-line page is based on bash.
Shells
zsh
Zsh is a shell designed for interactive use, although it is also a powerful scripting language. Many of the useful features of bash, ksh, and tcsh were incorporated into zsh; many original features were added. The introductory document details some of the unique features of zsh. It assumes basic knowledge of the standard UNIX shells; the intent is to show a reader already familiar with one of the other major shells what makes zsh more useful or more powerful. This document is not at all comprehensive; read the manual entry for a description of the shell that is complete, concise and up-to-date, although somewhat overwhelming and devoid of examples. Alternatively, the user guide offers wordy explanations of many of the shell's features.
- Website: http://zsh.sourceforge.net/
- Documentation: http://zsh.sourceforge.net/Doc/
- Tips, tricks and examples: http://grml.org/zsh/zsh-lovers.html
- Available from repository.
Graphical environment
From the bottom up:
- Xorg, XFree86 and X11 are display servers https://en.wikipedia.org/wiki/Display_server. This creates the graphical environment.
- [gkxsw]dm, lxdm, lightdm and nodm are display managers alias login managers https://wiki.debian.org/DisplayManager. This is the first X program run by the system if the system (not the user) is starting X and allows you to log on to the local system, or network systems.
- A window manager controls the placement and decoration of windows http://xwinman.org/intro.php. That is, the window border and controls are the decoration. Some of these are stand alone (WindowMaker, sawfish, fvwm, etc). Some depend on an accompanying desktop environment.
- A desktop environment such as XFCE, CINNAMON, MATE, KDE or GNOME are a suite of applications designed to integrate well with each other to provide a consistent experience http://www.linux.org/resources/categories/linux-desktop-environments.22/.
- A terminal emulator, terminal application, term, or tty for short, is a program that emulates a video terminal within some other display architecture.
In theory (and mostly so in practice) any of those components are interchangeable.
Window managers
openbox
Openbox is included in most popular linux distributions. It can be run within GNOME and KDE. And can also be used without a desktop environment (the lightweight approach). You can install additional features yourself, making it very customisable. It does not work well straight out of the box. You will probably need to install tools for power mangement, networking, managing displays, etc. Openbox comes with a default autostart which sets up an environment for both GNOME and KDE applications to run properly in (if you have them installed), as well as providing support for SCIM language input. See the autostart documentation for more details on setting it up. It is excellent for spending some experimentation time on, gaining insights in how window managers work and how else they could work.
- Website: http://openbox.org/wiki/Main_Page
- Autostart documentation http://openbox.org/wiki/Help:Autostart
- FAQ: http://openbox.org/wiki/Help:FAQ
awesome
Awesome (GNU GPLv2) is a configurable framework window manager for X. It is primarly targeted at power users, developers and any people dealing with every day computing tasks and who want to have fine-grained control on their graphical environment using the Lua programming language.
- Website: http://awesome.naquadah.org/
- Documentation: http://awesome.naquadah.org/wiki/Main_Page
- Community: http://awesome.naquadah.org/community/ (IRC and mailinglists)
Terminal emulator managers
terminator
Terminator (GPL-2.0+) is a useful tool for arranging terminals, inspired by programs such as gnome-multi-term, quadkonsole, etc. in that the main focus is arranging terminals in grids (tabs is the most common default method, which Terminator also supports).
- Website: https://www.openhub.net/p/gnome-terminator
- Available from repository.
tmux
tmux is a terminal multiplexer and lets you switch easily between several programs in one terminal, detach them (they keep running in the background) and reattach them to a different terminal.
- Website: http://tmux.github.io/
- Available from repository. Requirements: libevent and ncurses.
GUI-based file managers
xfe
X File Explorer (Xfe) is an M$-Explorer or Commander like file manager for X. It is based on the popular, but discontinued, X Win Commander, originally developed by Maxim Baranov. Xfe aims to be the file manager of choice for all light thinking Unix addicts! By default it presents a traditional tree view on the left and file panel on the right, but three other modes are available -- two panels, tree and two panels, or a single panel. Open With and Associate options are available from the right-click menu. Although it does not have a lot of the advanced features of Konqueror or Nautilus, it should be more than sufficient for the average user. Its speed and familiarity make it a good choice for older systems, newer users, or those of us who'd run filer.exe under Wine if it could handle file permissions.
- Website: http://roland65.free.fr/xfe/
gentoo
Gentoo is the GTK+ file manager (the name is not related to the Gentoo linux distribution) using a two-pane layout with icon associations for most file extensions. Gentoo also relies on a button bar, located below the file panes, for most operations, but each button may have a secondary function, accessed from the middle mouse button. A second, smaller button bar to the left provides shortcuts to specific directories. The configuration menu is not very extensive, and you can change options with the mouse. Gentoo also provides click-to-sort functionality in the file panes, mount and unmount capabilities, and display of file permissions by color. You can add and edit buttons and give them a specific color and tool tip.
- Wesite: http://www.obsession.se/gentoo/
gcmd
GNOME Commander offers a small footprint and a polished GUI. It provides the more typical tool bar and menu system, in addition to mapping buttons to each function key. It also provides a command history, capacity for multiple predefined FTP sessions, filesearch, advanced rename tool - allowing for quick renaming of multiple files using regular expressions, counters, and case matching. A compact, polished file manager, especially suitable for those running the GNOME desktop.
- Website: http://gcmd.github.io/
Desktop file managers
spacefm
SpaceFM is a multi-panel tabbed file and desktop manager for Linux with built-in VFS, udev- or HAL-based device manager, customisable menu system, and bash integration. SpaceFM aims to provide a stable, capable file manager with significant customisation capabilities. SpaceFM & udevil can be used completely without systemd, consolekit, policykit, dbus, udisks, gvfs & fuse (although it can coexist with any of these).
System tools
System monitoring
conky
Conky is a free, light-weight system monitor for X, that displays any information on your desktop. Conky is licensed under the GPL and runs on Linux and BSD.
- Website: http://conky.sourceforge.net/
- Documentation: http://conky.sourceforge.net/documentation.html
Research
Storing information
Only use those fitting your desktop manager, or else you'll end up with a spaghetti distro.
Basket (KDE)
- Website http://basket.kde.org/
Tomboy (GNOME)
- Website https://github.com/GNOME/tomboy
KeepNote
Windows, Linux, and MacOS X
- Website http://keepnote.org/
Security applications
Anti-malware
rkhunter
Rootkit Hunter (GNU GPL) is a Unix-based tool that scans for rootkits, backdoors and possible local exploits. Specifically, rkhunter is a shell script which carries out various checks on the local system to try and detect known rootkits and malware. It also performs checks to see if commands have been modified, if the system startup files have been modified, and various checks on the network interfaces, including checks for listening applications. rkhunter has been written to be as generic as possible, and so should run on most Linux and UNIX systems. It is provided with some support scripts should certain commands be missing from the system, and some of these are Perl scripts.
- Website: http://rkhunter.sourceforge.net/
- FAQ: http://rkhunter.cvs.sourceforge.net/viewvc/rkhunter/rkhunter/files/FAQ
- Mailing list: http://sourceforge.net/p/rkhunter/mailman/
- Available from repository. Requirements: Bourne Again Shell (Bash) and exim
chrootkit
chkrootkit (Free software) is a tool to locally check for signs of a rootkit. It tests the following applications: aliens, asp, bindshell, lkm, rexedcs, sniffer, w55808, wted, scalper, slapper, z2, chkutmp, amd, basename, biff, chfn, chsh, cron, crontab, date, du, dirname, echo, egrep, env, find, fingerd, gpm, grep, hdparm, su, ifconfig, inetd, inetdconf, identd, init, killall, ldsopreload, login, ls, lsof, mail, mingetty, netstat, named, passwd, pidof, pop2, pop3, ps, pstree, rpcinfo, rlogind, rshd, slogin, sendmail, sshd, syslogd, tar, tcpd, tcpdump, top, telnetd, timed, traceroute, vdir, w, and write.
- Website: http://www.chkrootkit.org/
- README: http://chkrootkit.org/README
- FAQ: http://chkrootkit.org/faq/
- Available from repository.
Encryption
gnupg
GnuPG (GNU GPL v3+) stands for GNU Privacy Guard and is a tool for secure communication and data storage. The software has two main uses. The first is to encrypt data to ensure its privacy. The second is to "sign" data so that others can determine it is authentic and unmodified. It includes an advanced key management facility and is compliant with the proposed OpenPGP Internet standard as described in RFC 2440. GnuPG is a command line tool with features for easy integration with other applications. The default public key algorithms are DSA and Elgamal, but RSA is also supported. Symmetric algorithms available are AES (with 128, 192, and 256 bit keys), 3DES, Blowfish, CAST5 and Twofish. Digest algorithms available are MD5, RIPEMD/160, SHA-1, SHA-256, SHA-384, and SHA-512. Compression algorithms available are ZIP, ZLIB, and BZIP2 (with libbz2 installed).
- Website: https://www.gnupg.org/
- Documentation: https://www.gnupg.org/documentation/index.html (includes guides, FAQ's and mailinglists)
- Available from repository.
mcrypt
mcrypt (GPLv2) is a replacement for the old crypt package and crypt command, with extensions. It allows developers to use a wide range of encryption functions, without making drastic changes to their code. It allows users to encrypt files or data streams without having to be cryptographers. The companion to mCrypt is libmcrypt, which contains the actual encryption functions themselves, and provides a standardized mechanism for accessing them.
- Website http://mcrypt.sourceforge.net/
- Available from repository.
steghide
steghide (GNU GPL) is a steganography program that is able to hide data in various kinds of image- and audio-files. Steghide employs an algorithm which is undetectable by color-frequency based statistical tests. Steghide uses a graph-theoretic approach to steganography. The default encryption algorithm is Rijndael with a key size of 128 bits (which is AES - the advanced encryption standard) in the cipher block chaining mode.
- Website: http://steghide.sourceforge.net/
- Documentation: http://steghide.sourceforge.net/documentation.php (english and spanish)
- Manual: http://steghide.sourceforge.net/documentation/manpage.php (english and spanish)
- Mailing lists: http://sourceforge.net/p/steghide/mailman/
- Available from repository. Requirements: libmhash, libmcrypt, libjpeg, zlib
stunnel
Stunnel (GNU GPL v2) is a program that allows you to encrypt arbitrary TCP connections inside SSL (Secure Sockets Layer). It allows for securing non-SSL aware daemons and protocols (like POP, IMAP, LDAP, etc) by having Stunnel provide the encryption, requiring no changes to the daemon's code. Stunnel does not contain any crytographic code itself -- instead it relies on external SSL libraries.
- Website: https://www.stunnel.org/index.html
- Documentation: http://www.stunnel.org/docs.html (english and polish)
- HowTo: http://www.stunnel.org/howto.html (Installation and Authentication)
- FAQ: http://www.stunnel.org/faq.html (Troubleshooting and Applications)
- Available from repository as stunnel4.
veracrypt
VeraCrypt is disk encryption software forked from the discontinued TrueCrypt software. VeraCrypt adds enhanced security to the algorithms used for system and partitions encryption, and solves many vulnerabilities and security issues found in TrueCrypt.
- Website: https://veracrypt.codeplex.com/
- Documentation: https://veracrypt.codeplex.com/documentation
ciphershed
CipherShed (will carry an OSI approved license (probably either Apache or BSD)) is free (as in free-of-charge and free-speech) encryption software and was started in June 2014 as a response to the end of life announcement for TrueCrypt. As of October 2014 CipherShed source code is hosted at GitHub. CipherShed is a program that can be used to create encrypted files or encrypt entire drives (including USB flash drives and external HDDs). There’s no complicated commands or knowledge required; a simple wizard guides you step-by-step through every process. After creating an encrypted file or disk drive, the encrypted volume is mounted through CipherShed. The mounted volume shows up as a regular disk that can be read and written to on-the-fly. The encryption is transparent to the operating system and any programs. When finished, the volume can be unmounted, and stored or transported elsewhere, fully secured. Encryption volumes can be moved from OS-to-OS (eg, Windows to Mac) with full compatibility.
- Website: https://ciphershed.org/
- Forum: https://forum.ciphershed.org/
Firewalls
gufw and ufw
Gufw (GNU GPL v3) is for users bamboozled by firewalls. It has an easy to use interface for setting up inbound and outbound traffic rules for apps/services and ports. It is designed for beginners. Gufw is a GUI front-end to ufw, which is in itself a front-end to netfilter and iptables
- Website: http://gufw.org/
netfilter and iptables
Netfilter (GNU GPL v2) is a framework that provides a set of hooks inside the Linux kernel that allows kernel modules to register callback functions with the network stack. A registered callback function is then called back for every packet that traverses the respective hook within the network stack. Software inside this framework enables packet filtering, network address [and port] translation (NA[P]T) and other packet mangling. iptables is a generic table structure for the definition of rulesets. Each rule within an IP table consists of a number of classifiers (iptables matches) and one connected action (iptables target).
iptables (GNU GPL v2) is a user space application program that allows a system administrator to configure the Netfilter tables, chains, and rules. The iptables package also includes ip6tables. ip6tables is used for configuring the IPv6 packet filter.
- Website: http://www.netfilter.org/
- HOWTOs http://www.netfilter.org/documentation/index.html#documentation-howto
- FAQ http://www.netfilter.org/documentation/index.html#documentation-faq
- Mailing lists http://www.netfilter.org/mailinglists.html
Intrusion detection
One of the key differences between Tripwire and Aide is their commercial status. Tripwire was originally a free, open source product and is now a commercial product but a free version (branched in 2000) is still being developed at http://sourceforge.net/projects/tripwire/. Aide is entirely open source and licensed via the GPL and much, much easier in its configuration. Tripwire offers extended features that make it more secure than Aide, but storing aide databases on an encrypted filesystem on another machine (or an external drive) can be considered good enough to not need tripwire's extended feature(s) and opt for aide instead. Not that you can't sign the databases AND put them on another machine or external drive.
aide
The Advanced Intrusion Detection Environment (GPL), for short aide, is a file integrity checker (FIA). It creates a database from the regular expression rules that it finds from the config file(s). Once this database is initialized it can be used to verify the integrity of the files. It has several message digest algorithms (md5, sha1, rmd160, tiger, crc32, sha256, sha512, whirlpool (additionally with libmhash: gost, haval, crc32b)) that are used to check the integrity of the file. All of the usual file attributes (File type, Permissions, Inode, Uid, Gid, Link name, Size, Block count, Number of links, Mtime, Ctime and Atime) can also be checked for inconsistencies. It can read databases from older or newer versions.
- Website: http://aide.sourceforge.net
- Manual: http://aide.sourceforge.net/stable/manual.html
- Available from repository.
- Example install and configuration of aide on debian: Linux security: Installing intrusion detection
tripwire
Open Source Tripwire is a free software security and data integrity tool useful for monitoring and alerting on specific file change(s) on a range of systems. Open Source Tripwire functions as a host-based intrusion detection system. It is suitable for monitoring a small number of servers where centralized control and reporting is not needed and professional support is not a requirement.
- Website: http://www.tripwire.com
- Mailinglists: http://sourceforge.net/p/tripwire/mailman/
- Available from repository.
- Example install and configuration of tripwire on debian: Linux security: Installing intrusion detection and Linux server security: Installing intrusion detection
Traffic capture
Traffic analysis
kismet
Kismet (GNU GPL) is an 802.11 layer2 wireless network detector, sniffer, and intrusion detection system. Kismet will work with any wireless card which supports raw monitoring (rfmon) mode, and can sniff 802.11b, 802.11a, and 802.11g traffic. Kismet identifies networks by passively collecting packets and detecting standard named networks, detecting (and given time, decloaking) hidden networks, and inferring the presence of nonbeaconing networks via data traffic.
- Website: http://www.kismetwireless.net/
- Documentation: http://www.kismetwireless.net/documentation.shtml
- Forums: http://www.kismetwireless.net/Forum/General/
- Available from repository. Requirements: Libpcap, GPSD, Imagemagick, Expat, GMP. Optional: DBUS (but not required)
wireshark
Wireshark (GNU GPL v2) is a network packet analyzer. A network packet analyzer captures network packets and tries to display that packet data as detailed as possible. A network packet analyzer can be regarded as a measuring device to examine what's going on inside a network cable, just like a voltmeter is used by an electrician to examine what's going on inside an electric cable (but at a higher level, of course). It is developed and maintained by a global team of protocol experts. It used to be known as Ethereal, and was renamed to Wireshark in May 2006.
- Website: http://www.wireshark.org/
- Documentation: https://www.wireshark.org/docs/
- Available from repository.
Packet crafting
hping
Hping3 (GNU GPL v2) is a command-line oriented TCP/IP packet assembler/analyser. The interface is inspired from the ping unix command, but hping isn't only able to send ICMP echo requests. It supports TCP, UDP, ICMP and RAW-IP protocols, has a traceroute mode, the ability to send files between a covered channel, and many other features. hping3 can handle fragmentation, and almost arbitrary packet size and content, using the command line interface.
- Website: http://www.hping.org/
- Documentation: http://www.hping.org/documentation.php
- Available from repository. Requirements: libpcap, Tcl/Tk (Optional)
scapy
Scapy (GNU GPL v2) is a powerful interactive packet manipulation program. It is able to forge or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and replies, etc. It can handle most classical tasks like scanning, tracerouting, probing, unit tests, attacks or network discovery (it can replace hping, 85% of nmap, arpspoof, arp-sk, arping, tcpdump, tethereal, p0f, etc.).
- Website: http://www.secdev.org/projects/scapy/
- Mailinglist: http://news.gmane.org/gmane.comp.security.scapy.general
- Available from repository. Requirements: python.
Port scanning
ipscan
Angry IP Scanner (GNU GPL v2) is an open-source and cross-platform network scanner designed to be fast and simple to use. It scans IP addresses and ports.
- Website: http://angryip.org/
- Documentation: http://angryip.org/documentation/
- FAQ: http://angryip.org/faq/
Vulnerability scanning
tiger
Tiger (GNU GPL) is a security tool that can be use both as a security audit and intrusion detection system. It is a set of scripts that scan a Un*x system looking for security problems, in the same fashion as Dan Farmer's COPS. It was originally developed to provide a check of UNIX systems on the A&M campus that want to be accessed from off campus (clearance through the packet filter). Unlike other tools, Tiger needs only of POSIX tools and is written entirely in shell language.
- Website: http://www.nongnu.org/tiger/
- README: http://cvs.savannah.gnu.org/viewvc/*checkout*/tiger/tiger/README?content-type=text%2Fplain&revision=HEAD
- HOWTO: http://cvs.savannah.gnu.org/viewvc/*checkout*/tiger/tiger/USING?content-type=text%2Fplain&revision=HEAD
- Project page: http://savannah.nongnu.org/projects/tiger
- Available from repository.
Data removal
bleachbit
BleachBit deletes unnecessary files to free valuable disk space, maintain privacy, and remove junk. It removes cache, Internet history, temporary files, cookies, and broken shortcuts. It handles cleaning of Adobe Reader, Bash, Beagle, Epiphany, Firefox, Flash, GIMP, Google Earth, Java, KDE, OpenOffice.org, Opera, RealPlayer, rpmbuild, Second Life Viewer, VIM, XChat, and more. Beyond simply erasing junk files, BleachBit wipes free disk space (to hide previously deleted files for privacy and to improve compression of images), vacuums Firefox databases (to improve performance without deleting data), and securely shreds arbitrary files.
- Website: http://bleachbit.sourceforge.net/
- Documentation: http://bleachbit.sourceforge.net/documentation
- Forums: http://bleachbit.sourceforge.net/forum
- Available from repository.
Password management
keepassx
KeePassX (GNU GPL v2) is a multi-platform port of KeePass, an open source and cross-platform password manager. This utility helps you to manage your passwords in a secure way. You can put all your passwords in one database, which is locked with one master key or a key-disk. This lets users only need to remember one single master password or insert the key-disk to unlock the whole database. The databases are encrypted using the algorithms AES (alias Rijndael) or Twofish using a 256 bit key. KeePassX currently uses same the database file format as the KeePass 1.x (Classic) password manager software for Windows.
- Website: http://www.keepassx.org/
- FAQ: http://www.keepassx.org/faq
- Available from repository. Requirements: Qt library 4.3 or higher, libXtst, X11 with XRandR, Xinerama, and XTest extensions, glibc 2.4
VPN
openvpn
OpenVPN (GNU GPL v2) is a full-featured virtual private network (VPN) solution accomodating a wide range of configurations, including remote access, site-to-site VPNs, WiFi security, and enterprise-scale remote access solutions with load balancing, failover, and fine-grained access-controls. OpenVPN implements OSI layer 2 or 3 secure network extension using the industry standard SSL/TLS protocol, supports flexible client authentication methods based on certificates, smart cards, and/or 2-factor authentication, and allows user or group-specific access control policies using firewall rules applied to the VPN virtual interface.
- Website: https://openvpn.net/
- FAQ: https://community.openvpn.net/openvpn/wiki/FAQ
- HOWTO: https://openvpn.net/index.php/open-source/documentation/howto.html
- Available via repository. Requirements: TUN and/or TAP driver to allow user-space programs to control a virtual point-to-point IP or Ethernet device
Desktop applications
Graphics editors
GIMP
The GNU Image Manipulation Program (GNU GPL v2) is a freely distributed raster graphic editor for photo retouching, image composition and image authoring. It can be used as a simple paint program, an expert quality photo retouching program, an online batch processing system, a mass production image renderer, an image format converter, etc. It also makes the task of screenshots easy. It is designed to be augmented with plug-ins and extensions. The advanced scripting interface allows simple tasks as well as complex image manipulation procedures to scripted.
- Website: http://www.gimp.org/
- Wiki: http://wiki.gimp.org/index.php/Main_Page
- Available from repositories.
- Requirements: gegl and GTK+ (dbus and gvfs are optional)
- GIMP configuration http://www.linuxfromscratch.org/blfs/view/svn/xsoft/gimp.html
Inkscape
Inkscape (GNU GPL v2) is a vector graphics editor with capabilities similar to Illustrator, Freehand, CorelDraw, and Xara X. The interface is designed to conform to GNOME standards. It uses the W3C standard Scalable Vector Graphics (SVG) file format, which is an open, industry-standard XML-based format for vector graphics developed by the W3C organisation. The popularity of this format is growing fast.
Supported SVG features include shapes, paths, text, markers, clones, alpha blending, transforms, gradients, patterns, and grouping. Inkscape also supports Creative Commons meta-data, node editing, layers, complex path operations, bitmap tracing, text-on-path, flowed text, direct XML editing, and more. It imports formats such as JPEG, PNG, TIFF, and others and exports PNG as well as multiple vector-based formats.
- Website: http://www.inkscape.org/
- Community: https://inkscape.org/en/community/
- Requirements: GTK+ version 2.8.x, gtkmm2 => 2.4, boehm-gc Garbage Collection Libraries => 6.4
Xara Xtreme
Xara (GPL) is a general purpose graphics program for Unix platforms including Linux, FreeBSD and (in development) OS X. It is a port of Xara's flagship software package, renowed for being the fastest vector package available, combined with an efficient working environment. May need a bit of tweaking to install.
- Website: http://www.xaraxtreme.org/
- Community: http://www.xaraxtreme.org/community.html
Image processing
gm
GraphicsMagick (MIT X11 style license) provides a collection of tools and libraries which support reading, writing, and manipulating an image in over 88 major formats including important formats like DPX, GIF, JPEG, JPEG-2000, PNG, PDF, PNM, and TIFF. Similar as imagemagick.
Minimalist applications
Text editors
vi and vim
Yes, even if you can't believe it, there are a lot fans of the 30-years-old vi editor (or its more recent, just-15-years-old, best clone & great improvement, vim). No, they are not dinosaurs who don't want to catch up with the times - the community of vi users just keeps growing. Yes, there are definite reasons why the vi/vim editing model is just superior to any other out there. And you don't need to be a Unix whiz to use it, either: vim is available for free for almost any platform out there, and there are plug-ins to get the functionality inside all major IDEs. [1]
- Cheatsheets: vi http://www.lagmonster.org/docs/vi.html, vim http://zzapper.co.uk/vimtips.html
- Editing MediaWiki articles with VIM http://blog.bigsmoke.us/2009/07/10/vim-mediawiki-editing
- Available from repository.
Console-based file managers
Servers often boot to run level 3, which provides no X display, but a good file manager can be crucial to administration.
mc
Midnight Commander is one of the best-known console file managers. Midnight Commander allows you to view two directories, a directory with file attributes, or a directory and file preview at the same time. On curses-based systems file types and permissions are shown by color, but you can specify "slow" and "ASCII-only" display modes from the command line. These are especially valuable for slow connections and on very old systems. Midnight Commander's help system is well-written, and invaluable, as Ctrl and Alt key combinations make up the bulk of functions. Pull-down menus are also available, and some functions are mapped to function keys, listed at the bottom of the display.
Midnight Commander supports FTP, console mouse, and file undeletion (on ext2 filesystems only). Many versions are available for both the console and X Windows. Midnight Commander's consistency between console and X file managers is a strong asset if you'd rather not learn two file managers, or run a console application in an xterm window.
- Website: http://www.midnight-commander.org/
- Documentation: http://www.midnight-commander.org/wiki/doc
vifm
Vifm lets you cut with dd, paste with p, and rename a file with cw. Movement keys are the standard vi hjkl, with h and l ascending and descending the directory tree. The right panel toggles between a display of a second directory and file properties. You can call shell commands from the command line with :!, with %f and %F corresponding to highlighted files in the left and right pane. Vifm also mirrors its treatment of bookmarks, visual file selection, and user-defined macros from vi. Most importantly, :help opens an extensive help file with more options. Like Midnight Commander vifm displays file properties by color, and it can set permissions and ownership; unlike Midnight Commander it does not offer file preview, although pressing Enter or l on a file will open it in vi. :apropos brings up a menu of all matching man pages, from which you can invoke man for the selected entry. If you like vi, try vifm.
- Website: http://vifm.info/
- Documentation: http://vifm.info/vimdoc.shtml
- Manual: http://vifm.info/manual.shtml
ranger
Ranger is a terminal based file manager with vi style keybindings and many features including 'rifle' file opener, previewing, tabs, bookmarks, tagging. ranger is not a two pane file manager like mc or vifm, but uses 'miller columns' showing the directory hierarchy (similar to mac os 'finder'). The centre column is active, the left column the higher level directory, and the right column shows either a deeper directory or file information or preview.
- Website: http://ranger.nongnu.org/
Websearch
surfraw
Shell Users' Revolutionary Front Rage Against the Web, surfraw for short, provides a fast unix command line interface to a variety of popular WWW search engines and other artifacts of power. It reclaims google, altavista, babelfish, dejanews, freshmeat, research index, slashdot and many others from the false-prophet, pox-infested heathen lands of html-forms, placing these wonders where they belong, deep in unix heartland, as god loving extensions to the shell. Surfraw abstracts the browser away from input. Doing so lets it get on with what it's good at. Browsing. Interpretation of linguistic forms is handed back to the shell, which is what it, and human beings are good at. Combined with netscape-remote or incremental text browsers, such as lynx, links or w3m, along with screen a surfraw liberateur is capable of navigating speeds that leave GUI tainted idolaters agape with fear and wonder.
- Website: http://surfraw.alioth.debian.org/
- Usage: http://surfraw.alioth.debian.org/#usage
- List of elvi: http://surfraw.alioth.debian.org/#elvilist
- Available from repository.
vimperator firefox extension
Vimperator is a Firefox browser extension with strong inspiration from the Vim text editor, with a mind towards faster and more efficient browsing. It has similar key bindings and you could call it a modal web browser, as key bindings differ according to which mode you are in. For example, it has a special Hint mode, where you can follow links easily with the keyboard only. Also most functionality is available as commands, typing :back will go back within the current page history, just like hitting the back button in the toolbar. In case you wish to control the web browser without using the mouse.
- Website: http://www.vimperator.org/vimperator (download link to .xpi on page)
mutt
Mutt is a small but very powerful text-based mail client for Unix operating systems.
- Website: http://www.mutt.org/
- FAQ: http://www.fefe.de/muttfaq/faq.html
- Wiki: http://dev.mutt.org/trac/wiki
- Mutt sidebar patch for mutt with folders listed in a sidebar http://www.lunar-linux.org/mutt-sidebar/
- Despising quiche mutt guide http://realprogrammers.com/jump_start/mutt/
- Getting Up and Running With a Sane Mutt Setup http://blog.developwithpassion.com/2013/05/02/getting-up-and-running-with-a-sane-mutt-setup/
mu
With the enormous amounts of e-mail many people gather and the importance of e-mail messages in our daily work-flow, it is very important to be able to quickly deal with all that - in particular, to instantly find that one important e-mail you need right now. For that, mu was created. mu is a tool for dealing with e-mail messages stored in the Maildir-format, on Unix-like systems. mu's main purpose is to help you to find the messages you need, quickly; in addition, it allows you to view messages, extract attachments, create new maildirs,...
- Website: http://www.djcbsoftware.nl/code/mu/
notmuch
Notmuch is a program for searching email. If you've been looking for a fast, global-search and tag-based email system to use within your text editor or in a terminal...If you're the kind of person that gets excited about being able to write shell scripts for exploring and manipulating your email...If you're a developer of an existing email program and would love a good library interface for fast, global search with support for arbitrary tags...If you want the convenience of fast, reliable search of all your email, but don't want to give a 3rd-party access to your email...Then notmuch may be exactly what you've been looking for.
- Website: http://notmuchmail.org/
Library
Development
Development environments
vagrant
Vagrant is for creating and configuring lightweight, reproducible, and portable development environments.
- Website: https://www.vagrantup.com/
- Documentation: http://docs.vagrantup.com/v2/getting-started/index.html
Server administration
File managers
sshfs
SSH Filesystem is a filesystem client based on the SSH File Transfer Protocol. Since most SSH servers already support this protocol it is very easy to set up: i.e. on the server side there's nothing to do. On the client side mounting the filesystem is as easy as logging into the server with ssh.
- Website: http://fuse.sourceforge.net/sshfs.html
- FAQ: http://sourceforge.net/p/fuse/wiki/SshfsFaq/
- Documentation: http://sourceforge.net/p/fuse/wiki/Main_Page/
Intrusion detection
There are two major types of Intrusion Detection Systems: network-based and host-based. Tripwire is host-based and Snort is a network-based IDS/IPS. Two side of a coin working in tandem.
tripwire
Open Source Tripwire is a free software security and data integrity tool useful for monitoring and alerting on specific file change(s) on a range of systems. Open Source Tripwire functions as a host-based intrusion detection system. It is suitable for monitoring a small number of servers where centralized control and reporting is not needed and professional support is not a requirement.
- Website: http://www.tripwire.com
- Mailinglists: http://sourceforge.net/p/tripwire/mailman/
- Available from repository.
snort
Snort (GNU GPL v2) is an open source network intrusion prevention and detection system sing a rule-driven language, which combines the benefits of signature, protocol and anomaly based inspection methods. It can perform real-time traffic analysis, alerting, blocking and packet logging on IP networks. It utilizes a combination of protocol analysis and pattern matching in order to detect anomalies, misuse and attacks. It detects a variety of attacks and probes, such as buffer overflows, stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more. Snort uses a flexible rules language to describe activity that can be considered malicious or anomalous as well as an analysis engine that incorporates a modular plugin architecture. Snort is capable of detecting and responding in real-time, sending alerts, performing session sniping, logging packets, or dropping sessions/packets when deployed in-line.
- Website: http://www.snort.org/
- User's manual: http://manual.snort.org/
- Community: https://www.snort.org/community
- FAQ: https://github.com/vrtadmin/snort-faq/blob/master/README.md
- Available from repository. Requirements: libpcap
Network monitoring
nagios
Nagios (GNU GPL v2) is a host and service monitor designed to inform you of network problems. The monitoring daemon runs periodic checks on hosts and services specified using external "plugins" which return status information to Nagios. When problems are encountered, the daemon can send notifications out to administrative contacts in a variety of different ways (email, instant message, SMS, etc.). Current status information, historical logs, and reports can all be accessed via a web browser. Although Nagios is powerful and flexible, it does require some time for it to be installed and configured correctly.
- Website: http://www.nagios.org/
- Documentation: https://www.nagios.org/documentation/
- Debian tutorials: http://www.debianhelp.co.uk/nagios.htm
- Mailinglists: http://sourceforge.net/p/nagios/mailman/
- Available from repository. Requirements: C compiler
tcpdump
Tcpdump is a common computer network debugging tool that runs under the command line. It allows the user to intercept and display TCP/IP and other packets being transmitted or received over a network to which the computer is attached. This program allows you to dump the traffic on a network. It can be used to print out the headers of packets on a network interface, filter packets that match a certain expression. You can use this tool to track down network problems, to detect "ping attacks" or to monitor network activities.
- Website: http://www.tcpdump.org/
- Available from repository. Requirements: libpcap
Traffic analysis
tcptrace
Tcptrace (GNU GPL) is a tool designed for analysis of TCP dump files. It can tell you detailed information about TCP connections by sifting through dump files. Specifically, tcptrace can produce several different types of output containing information on each connection seen, such as elapsed time, bytes and segments sent and recieved, retransmissions, round trip times, window advertisements, throughput, and more. It can also produce a number of graphs for further analysis.
- Website: http://www.tcptrace.org/
- Manual: http://www.tcptrace.org/manual.html
- FAQ: http://www.tcptrace.org/faq.html
- Mailinglists: http://www.tcptrace.org/maillist.html
System tools
ncdu
NCurses Disk Usage (MIT License) is a disk usage analyzer with an ncurses interface. It is designed to find space hogs on a remote server where you don't have an entire gaphical setup available, but it is a useful tool even on regular desktop systems. Ncdu aims to be fast, simple and easy to use, and should be able to run in any minimal POSIX-like environment with ncurses installed.
- Website: http://dev.yorhel.nl/ncdu
- Manual: http://dev.yorhel.nl/ncdu/man
Backups
rsync
Rsync (GPL v3) is an open source utility that provides fast incremental file transfer. Rsync is a file-copying tool which can copy locally and to/from a remote host. It offers many options to control its behavior, and its remote-update protocol can minimize network traffic to make transferring updates between machines fast and efficient. It is widely used for backups and mirroring and as an improved copy command for everyday use. This package provides both the rsync command line tool and optional daemon functionality.
- Website: http://rsync.samba.org/
- Documentation: http://rsync.samba.org/documentation.html
unison
Unison (GPL v3) is a file-synchronization tool for OSX, Unix, and Windows. Unison is written in OCaml. It allows two replicas of a collection of files and directories to be stored on different hosts (or different disks on the same host), modified separately, and then brought up to date by propagating the changes in each replica to the other. Unison can run on and synchronize between Windows and many UNIX platforms. Unison requires no root privileges, system access or kernel changes to function. Unison can synchronize changes to files and directories in both directions, on the same machine, or across a network using ssh or a direct socket connection. Transfers are optimised using a version of the rsync protocol, making it ideal for slower links. Unison has a clear and precise specification, and is resilient to failure due to its careful handling of the replicas and its private structures.
- Website: http://www.cis.upenn.edu/~bcpierce/unison/
- User manual: http://www.cis.upenn.edu/~bcpierce/unison/docs.html
- Mailinglists: http://www.cis.upenn.edu/~bcpierce/unison/lists.html
Services
Mailing lists
mailman
Mailman is free software for managing electronic mail discussion and e-newsletter lists. Mailman is integrated with the web, making it easy for users to manage their accounts and for list owners to administer their lists.
Related
- Installing linux
- Linux security
- Kinky linux command-line
- Anonymising your traffic with linux
- Clean up all teh things
- Shell scripting
- Encrypting everything
References
- ↑ Why, oh WHY, do those #?@! nutheads use vi? http://www.viemu.com/a-why-vi-vim.html