Linux security
From Gender and Tech Resources
This page contains some basic security measures specifically for people getting started with linux. Knowing your way around a bit on the kinky linux command-line is required for easily doing these steps. If you run into trouble, find us on IRC.
Contents
Setting up root mail
Debian with MATE comes with the exim mailserver installed. If you don't like exim, install postfix (if you install the one, the other is uninstalled).
- Exim uses the Sendmail design model where a single binary controls all the facilities of the MTA. This monolithic design is inherently less secure due to the lack of binary separation between the individual components of the system. Exim separates processes and has well-defined stages where it gains or loses privileges.
- Postfix has a modular design to improve security over Qmail. A master daemon (a background process) launches other smaller processes with limited privileges that do specific tasks related to the various stages of mail delivery. The modular approach limits the effects of attacks.
- Sendmail is the default MTA shipped with many Linux distribution sets and is the most well-known. It is easy to configure but had the most security loopholes, partly because it was designed long before hackers started attacking email systems. Developers fix most security issues quickly, but because it has the most number of users, it is still the biggest target for hackers.
To install postfix:
$ sudo apt-get install postfix
icedove
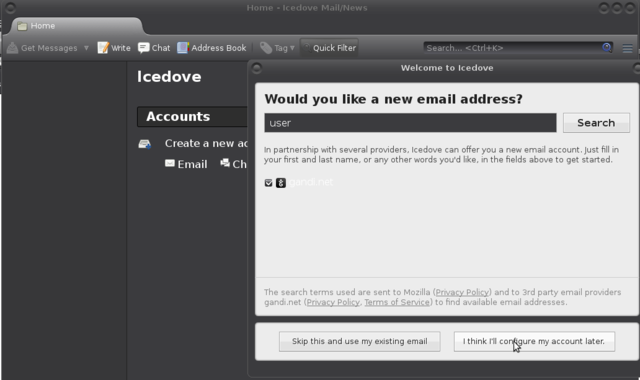
The wizard of Icedove (Thunderbird) does not allow directly for setting up local mail adresses. Choose "I think I'll configure my account later.":
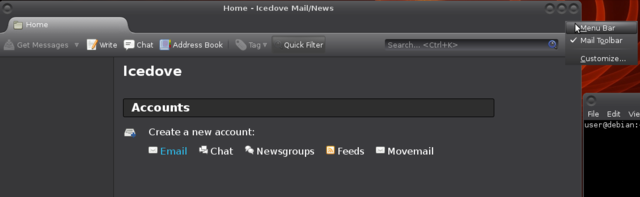
Make the menu appear, and choose the big Movemail link (all the way to the right of the blue email):
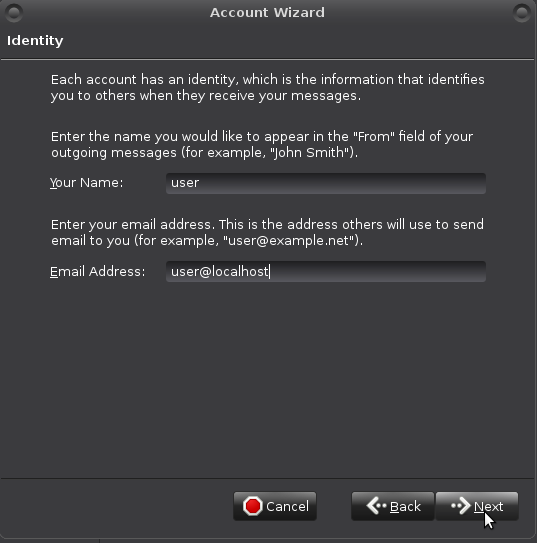
Fill in "Identity" data like so:
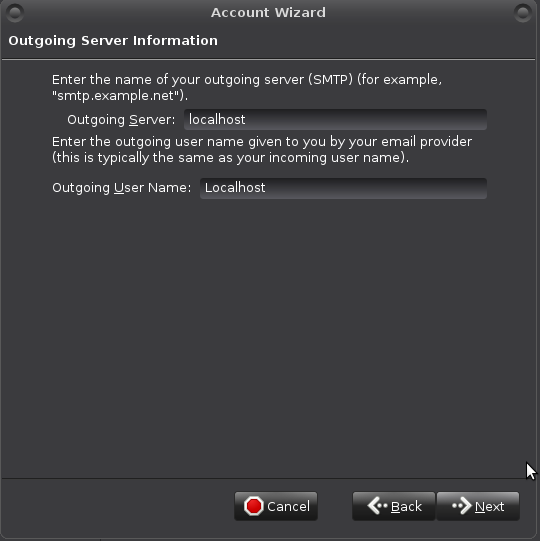
Outgoing Server Information like so (will be revisited):
Your "Account Name":
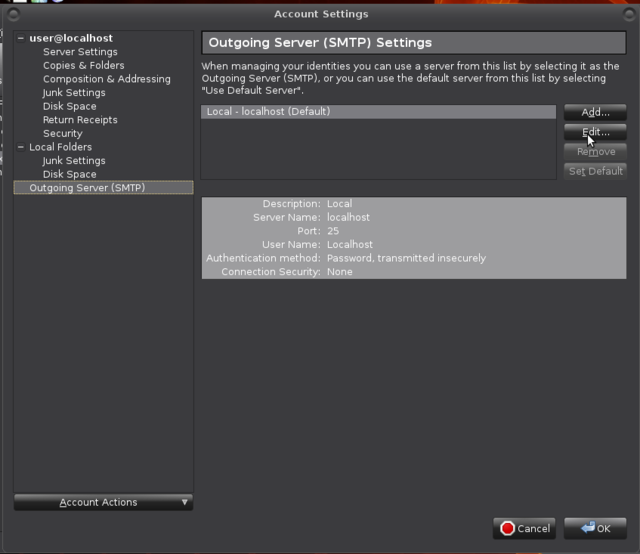
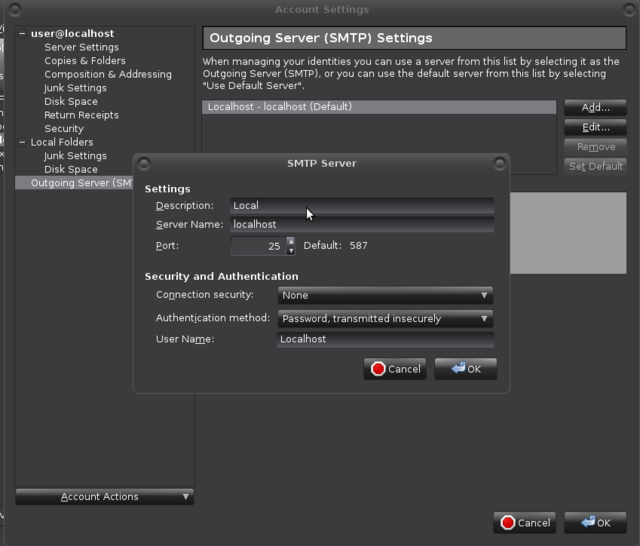
If all went well the account has appeared. Revisit SMTP settings: Edit > Account Settings -> Outgoing Server (SMTP) -> Edit
Set Port 25:
You may already have messages for user. Maybe not for root yet.
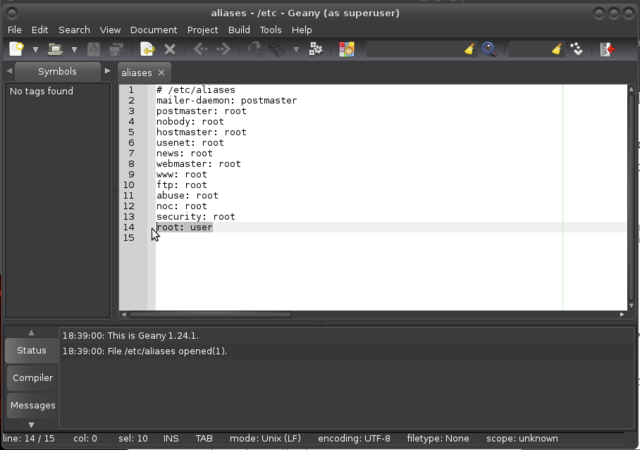
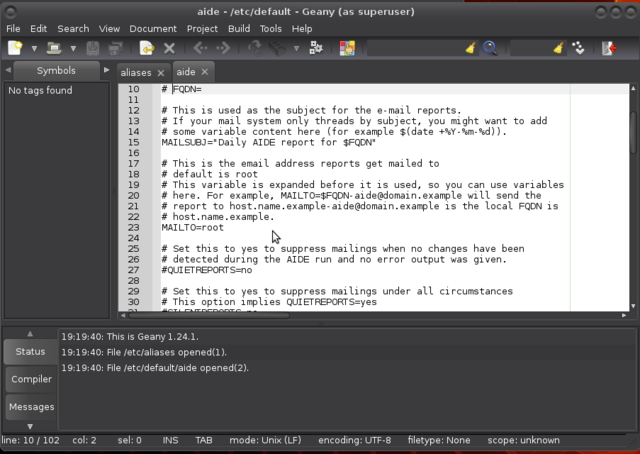
Open /etc/aliases with your favourite editor (vi, vim, nano, geany):
$ sudo geany /etc/aliases
And make sure there is a root: username, username being *your* username of course, and a postmaster: root line in the file.
mutt
Installing intrusion detection
You can use a firewall, keep your system softwares up to date, stop all unrequired services, use long and difficult passwords and password managers, and more (see below), there is still a chance that some intruder might get into your system.
When intruders penetrate your system there is a great chance that they will want to make their presence as quiet as possible. To do so, they are most likely to replace some common binaries such as ls, netstat or ps with versions that will not make their presence visible. For example, ls can be replaced with an ls version that won't show the files they created, netstat will not show connections that are used by the intruder, and ps will hide processes the intruder runs. To detect changes like that in your system, you can set up intrusion detection with for example aide or tripwire.
Aide and Tripwire are both File Integrity Agents (FIAs). A FIA monitors the integrity and state of the files and objects on your machine. If it detects changes to those files, then it alerts the administrator that an unauthorised access or change has taken place. FIAs usually take a hash of all files to be monitored using an algorithm like MD5. The snapshot is periodically checked against the current hash of the file and any variations alerted on.
One of the key differences between Tripwire and Aide is their commercial status. Tripwire was originally a free, open source product and is now a commercial product but a free version (branched in 2000) is still being developed at http://sourceforge.net/projects/tripwire/. Aide is entirely open source and licensed via the GPL and much, much easier in its configuration. Tripwire offers extended features that make it more secure than Aide, but storing aide databases on an encrypted filesystem on another machine (or an external drive) can be considered good enough to not need need tripwire's extended feature(s) and opt for aide instead. Not that you can't sign the databases AND put them on another machine or external drive.
In hostile environments such as server environments, using a FIA makes sense only if it is installed, fully configured and initialised at the very first boot after an installation from scratch, before ever connecting to the internet or doing anything else. It takes only one attack to install a backdoor. Installing aide or tripwire after such an event would guarantee that the backdoor remains just as open as the day an intruder installed it.
aide
To install aide on a debian based system:
$ sudo apt-get install aide
Open up /etc/default/aide with your favourite editor to change who to send its reports to:
$ sudo geany /etc/default/aide
Initialise (this can take some time):
$ sudo aideinit
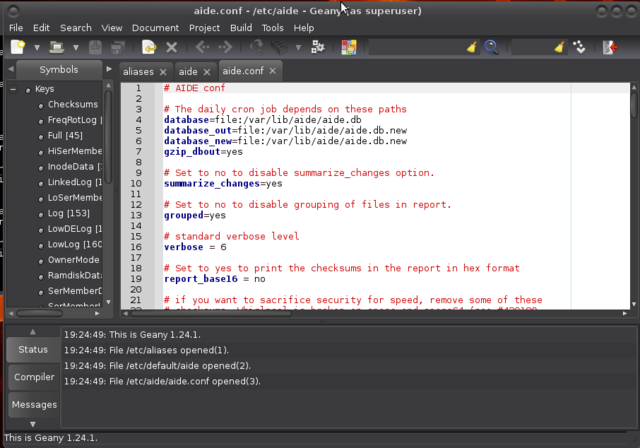
Most of aide configuration can be found in /etc/aide/aide.conf. This file is pretty well documented and default rules are quite decent. Aide aims at reporting files that changed since the last snapshot (stored in /var/lib/aide/aide.db). In hostile environments, a good security measure is to keep the database file on a floppy disk, cdrom or external disk. If you have such a device, you can copy the current snapshot to it and use the snapshot from that device during later runs of aide.
Before making modifications to the configuration file, make a backup first:
$ sudo cp /etc/aide/aide.conf /etc/aide/aide.conf.old
So let say that you have a copy of aide.db on an external disk. To use that snapshot, you can change database=file:/var/lib/aide/aide.db to database=file:/media/user/drive/aide/aide.db:
Read through the file to acquaint yourself with aide. By default, changes in Binaries and Libraries directories are checked. Those are matched to the BinLib rule, which basically checks for any changes in permissions, ownership, modification, access and creation date, size change, md5 and sha1 signature, inode, number of links and block count. Then, it also checks for modifications in the log files against the rule Logs. Because log files tend to grow, you cannot use a signature there and you also have to ask aide not to check for size modification (S).
On debian alikes, aide is run on a daily basis through the script /etc/cron.daily/aide. Default settings in /etc/default/aide tells aide to update it's database. Using database_out value in /etc/aide/aide.conf, aide is going to output a new database any time it runs in /var/lib/aide/aide.db.new if you kept the default settings.
Any time you will install new packages, change some configuration settings ..., run:
$ sudo /etc/cron.daily/aide
And check in the report that any modifications were only done to files you intended to modify and that added files are only coming from packages you have just installed and copy the new database to whatever place your database points to. Great way to learn about linux and non-intended changes too.
tripwire
Managing passwords
Using a password manager allows you to load passwords in your clipboard, making it hard to catch it with a keylogger (just in case). And all good password managers allow you to generate passwords, making the passwords independent from your personal preferences and harder to crack. One of the easiest password managers is a GUI tool called keepassx:
$ sudo apt-get install keepassx
It will appear in your menu. A "first steps" tutorial can be found here http://keepass.info/help/base/firststeps.html
Recommendations:
- Keep the database on a removable medium like an encrypted USB stick.
- Use a second encrypted stick to keep a backup of that database on.
- For added security, set up the database to use a password as well as a keyfile.
- Try to always close off the application. It uses a lockfile to prevent access by other processes. Quitting the application removes it. If not, and whenever you get a message that you cannot open your database, check on the USB in the directory where the database resides that there isn't a lockfile blocking access. If there is a lockfile while the database is not open for you, just delete the lockfile.
- On rare occasions a database is truly corrupted. That backup on that other stick, phew. :D
If you want to try your hand at cracking your own (current and new) passwords, try one of these http://sectools.org/tag/pass-audit/
Turning camera off
Intruders can gain access to their victims’ computers with remote-access Trojans (RATs) – malware that gives an intruder administrative control over its targeted computers, including, in this case, the ability to remotely control webcams. It’s an invisibly-installed malware program spread via email attachment or by tricking victims into visiting a booby-trapped site.
Tape the camera. It may even be possible to turn it off in BIOS (depending on your version).
Better yet, if you know what driver module is controlling the webcam, you can disable the driver with modprobe -r.
Check with:
$ lsmod | grep "uvc"
If stuff like this appears, your webcam device uses an uvc driver http://www.ideasonboard.org/uvc/:
uvcvideo 79005 0 videobuf2_vmalloc 12816 1 uvcvideo videobuf2_core 47787 1 uvcvideo videodev 126451 3 uvcvideo,v4l2_common,videobuf2_core media 18305 2 uvcvideo,videodev usbcore 195340 7 uvcvideo,ums_realtek,usb_storage,ehci_hcd,ehci_pci,usbhid,xhci_hcd
To disable the cam:
$ sudo modprobe -r uvcvideo
To enable the cam:
$ sudo modprobe uvcvideo
If not an uvcvideo driver, try $ sudo lsmod | grep "video" and use the modinfo command to find out more about a particular module:
$ sudo modinfo [modulename]
Then replace the "uvcvideo" in the above modprobe command with the name of your driver module.
To disable the webcam at boot (if file not exists, create it):
$ sudo geany /etc/modprobe.d/blacklist.conf
At bottom of the file add this line: blacklist uvcvideo (or the name of your driver instead of "uvcvideo").
Save the file and reboot. Your webcam is no longer functioning.
Turning microphone off
Open the alsa control panel for muting the microphone:
$ sudo alsamixer
You can also use the same modprobe enabling/disabling method as used above for webcam. This page may be helpful for finding your driver module: http://alsa.opensrc.org/ALSA_modules.
Using a firewall
With a firewall, you can:
- Log hosts scanning services that aren't running
- Limit the services that programs can connect to
- Segregate the local network into trust segments (LAN, DMZ, and Internet)
- Redirect ports to the hosts providing the service (NAT).
If you have a single machine only the first two would be of interest. These are also the two that are most likely to cause issues for a beginning user.
ufw and gufw
In mint and ubuntu, a firewall is installed, but is disabled by default. Usually it's better to turn it on. Especially on mobile devices like laptops, which sometimes connect to other networks than your own.
The firewall is called Uncomplicated Firewall (ufw), and can be operated from the terminal (Menu > Accessories > Terminal):
$ sudo ufw enable
Type your password when prompted; this will remain entirely invisible, not even asterisks will show, which is normal. Uncomplicated Firewall (ufw) has a sensible set of default settings (profile), which are fine for the vast majority of home users. So unless you have special wishes: you're done!
You can check the status of the firewall with this command:
$ sudo ufw status verbose
If you wish, you can install a GUI frontend to ufw, called gufw:
$ sudo apt-get install gufw
And it'll be in your menu items (the icon in mint is a brick wall).
netfilter and iptables
Safer browsing
It is clear that browsing has the most low cost attack vectors for data theft by hackers, tracking by corporations and for governmental spying. Safer browsing is a good investment all around.
Choose your browser carefully
(also see note about evercookie and Opera)
Configuring browsers
Browser extensions
Checks and balances
Encryption
For an overview of encryption concepts see encrypting everything and for application of concepts in useful tools Object encryption on linux and Anonymising your traffic with linux.
Configure sysctl (*)
Traffic monitoring
Backups
tar
gzip
bzip2
Backup to removable media
Backup over ssh
Backup with rsync
Backup with unison
Audit your setup
Resources
General
- Linux security http://www.linuxsecurity.com/
Debian
- Security information https://www.debian.org/security/
- Securing Debian Manual https://www.debian.org/doc/manuals/securing-debian-howto/index.en.html
Ubuntu
- Ubuntu security notices http://www.ubuntu.com/usn/
- Basic Ubuntu Security Guide, Desktop Edition https://wiki.ubuntu.com/BasicSecurity