Difference between revisions of "Surveillance"
From Gender and Tech Resources
m (→Sharing of data) (Tag: VisualEditor) |
|||
| (23 intermediate revisions by one other user not shown) | |||
| Line 2: | Line 2: | ||
The prisoners in the Panopticon could thus never know whether they were being surveilled, meaning that they have to, if they want to avoid running the risk of severe punishment, assume that they were being watched at all times. Thus, the Panopticon functioned as an effective tool of social control even when it wasn’t being staffed by a single guard. | The prisoners in the Panopticon could thus never know whether they were being surveilled, meaning that they have to, if they want to avoid running the risk of severe punishment, assume that they were being watched at all times. Thus, the Panopticon functioned as an effective tool of social control even when it wasn’t being staffed by a single guard. | ||
| + | |||
| + | This page is an ongoing effort and forever under construction. | ||
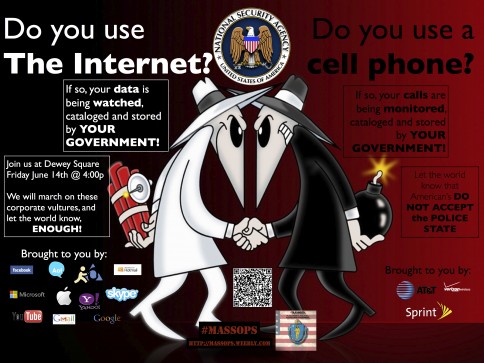
[[File:Spy_vs_spy_by_xxweareanonymousxx-d6b9mkt.jpg|484px|thumb|right|http://xxweareanonymousxx.deviantart.com/art/Spy-Vs-Spy-381721997]] | [[File:Spy_vs_spy_by_xxweareanonymousxx-d6b9mkt.jpg|484px|thumb|right|http://xxweareanonymousxx.deviantart.com/art/Spy-Vs-Spy-381721997]] | ||
== Technocracy == | == Technocracy == | ||
| − | The logic of this system is, in a limited sense, highly logical: past elites were unable to maintain control due to human mistakes and unpredictabilities. The thinking behind a technocracy is that machines make no mistakes. The large tech companies have all discussed this openly at large conferences. Money is a symbol of energy, and the erection of the mass surveillance grid is not for the purpose of security or preventing 'terrorism'. <ref>NSA Surveillance is about Control & Leverage, not Security http://www.juancole.com/2014/01/surveillance-leverage-security.html | + | The logic of this system is, in a limited sense, highly logical: past elites were unable to maintain control due to human mistakes and unpredictabilities. The thinking behind a technocracy is that machines make no mistakes (this is a weakness of theirs). The large tech companies have all discussed this openly at large conferences. Money is a symbol of energy, and the erection of the mass surveillance grid is not for the purpose of security or preventing 'terrorism'. <ref>NSA Surveillance is about Control & Leverage, not Security http://www.juancole.com/2014/01/surveillance-leverage-security.html</ref> |
| − | </ref> | + | == Surveillance == |
| + | === Dragnet surveillance === | ||
| + | Every citizen on this planet is subject to mass surveillance. This includes data that does not, by itself, identify individuals, but sits in various databases until analysts do a search for a particular name. Then network analysts connect within two degrees and surveil others. | ||
| + | |||
| + | There are important details about these programs that need to be filled in. A large amount of information is supposedly already in the public domain but consists mainly of presentations with a kazillion names in 'em (that can easily be altered). This page attempts to make sense of the spaghetti. | ||
| + | |||
| + | === Targeted surveillance === | ||
| + | Journalists and observers working on reporting on projects like national security, leaks, environmental issues, activist coverage, demonstration coverage, waste and abuse in governments, human rights, crime, may be targeted by state and private actors. Scenarios where people are being followed require a bit more thinking than installing and using tools on our machines. | ||
== Legalities == | == Legalities == | ||
| Line 15: | Line 24: | ||
==== Executive Order 12333 (EO12333) ==== | ==== Executive Order 12333 (EO12333) ==== | ||
Executive Order 12333 - 1.13 allows the FBI to provide the NSA with "technical assistance" in the United States, i.e. to collect metadata about American citizens by collaborating with "foreign intelligence" and law enforcement services. <ref>Meet the Spies Doing the NSA’s Dirty Work http://foreignpolicy.com/2013/11/21/meet-the-spies-doing-the-nsas-dirty-work/ | Executive Order 12333 - 1.13 allows the FBI to provide the NSA with "technical assistance" in the United States, i.e. to collect metadata about American citizens by collaborating with "foreign intelligence" and law enforcement services. <ref>Meet the Spies Doing the NSA’s Dirty Work http://foreignpolicy.com/2013/11/21/meet-the-spies-doing-the-nsas-dirty-work/ | ||
| − | </ref> By using telecom companies the US government can circumvent controls and accountability that don't apply to companies. All major telecom companies have worked closely and secretly with government spying since their inceptions. | + | </ref> By using telecom companies the US government can circumvent controls and accountability that don't apply to companies. All major telecom companies have worked closely and secretly with government spying since their inceptions. |
| + | |||
| + | ==== Plausible Deniability ==== | ||
| + | |||
| + | Plausible deniability began under Central Intelligence Agency (CIA) director Allen Dulles <ref>Spywriter: Plausible deniability http://spywriter.com/robots/plaus_denial.html</ref>.'' The CIA black ops division undertakes dangerous and usually what would be considered illegal missions that are not officially sanctioned by the US administration so that the administration, which usually benefits from such missions, can safely disavow any knowledge of them in the event of their publically uncovered success or failure. The administration is in the position of plausible deniability towards the CIA's actions'' <ref>Urban dictionary: http://www.urbandictionary.com/define.php?term=plausible%20deniability</ref>. | ||
== Intelligence == | == Intelligence == | ||
| Line 49: | Line 62: | ||
PRISM is part of the overall NSA surveillance effort - a program authorised in the united states under the FISA Amendments Act (FAA), now located in Section 702 of the FISA, that allows the NSA to collect communications of specifically identified foreign targets. | PRISM is part of the overall NSA surveillance effort - a program authorised in the united states under the FISA Amendments Act (FAA), now located in Section 702 of the FISA, that allows the NSA to collect communications of specifically identified foreign targets. | ||
| − | When people in the rest of the world use the net, they are effectively using US-based services, making them a legal target for US intelligence. Supposedly the NSA has no "direct access" to the servers of companies through PRISM - other agencies, like the FBI, collect the data. Emails, chat--video, voice, photos, stored data, VoIP, file transfers, video conferencing, notifications of target activity--logins, etc, online social networking details, and special requests are collected from nine major Silicon Valley technology companies: Facebook, Google, Yahoo, Microsoft, PalTalk, Skype, YouTube, Apple, and AOL. | + | When people in the rest of the world use the net, they are effectively using US-based services, making them a legal target for US intelligence. Supposedly the NSA has no "direct access" to the servers of companies through PRISM - other agencies, like the FBI, collect the data. Emails, chat--video, voice, photos, stored data, VoIP, file transfers, video conferencing, notifications of target activity--logins, etc, online social networking details, and special requests are collected from nine major Silicon Valley technology companies: Facebook, Google, Yahoo, Microsoft, PalTalk, Skype, YouTube, Apple, and AOL. <ref> |
| + | What is known about NSA's PRISM program http://electrospaces.blogspot.nl/2014/04/what-is-known-about-nsas-prism-program.html | ||
| + | </ref> | ||
==== Upstream collection ==== | ==== Upstream collection ==== | ||
| Line 57: | Line 72: | ||
* Unilateral cable tapping operations | * Unilateral cable tapping operations | ||
The five biggest collection programs of the Special Source Operations division are DANCINGOASIS, SPINNERET, MOONLIGHTPATH, INCENSER and AZUREPHOENIX. The largest cable tapping program appears to be DANCINGOASIS (DGO) <ref>NSA's largest cable tapping program: DANCINGOASIS http://electrospaces.blogspot.nl/2014/05/nsas-largest-cable-tapping-program.html | The five biggest collection programs of the Special Source Operations division are DANCINGOASIS, SPINNERET, MOONLIGHTPATH, INCENSER and AZUREPHOENIX. The largest cable tapping program appears to be DANCINGOASIS (DGO) <ref>NSA's largest cable tapping program: DANCINGOASIS http://electrospaces.blogspot.nl/2014/05/nsas-largest-cable-tapping-program.html | ||
| − | </ref>. It could be that DANCINGOASIS is another umbrella program encompassing various smaller sub-programs. | + | </ref>. It could be that DANCINGOASIS is another umbrella program encompassing various smaller sub-programs. |
| + | |||
| + | Upstream collection also includes data from MUSCULAR in a joint operation with the GCHQ. | ||
Internet data collected by Upstream programs can be processed and searched though the XKEYSCORE indexing and analysing system. BOUNDLESS INFORMANT tracks the international intelligence gathering techniques of the NSA. | Internet data collected by Upstream programs can be processed and searched though the XKEYSCORE indexing and analysing system. BOUNDLESS INFORMANT tracks the international intelligence gathering techniques of the NSA. | ||
| Line 65: | Line 82: | ||
XKEYSCORE is reported to receive unfiltered internet communication sessions ('full-take') from WEALTHYCLUSTER2. The session data is stored for a short period of time: content is buffered for 3 to 5 days (sometimes shorter or sometimes longer, depending on the amount of traffic), and metadata for up to 30 days. In other words, XKEYSCORE creates a rolling buffer that is continually being rewritten. This buffering enables analysts to perform federated queries using so-called "soft selectors", like keywords, against the body texts of e-mail and chat messages, digital documents, and spreadsheets in English, Arabic and Chinese. XKEYSCORE also allows analysts to look for the usage of encryption, the use of a VPN or the TOR network, and a number of other things that could lead to a target. | XKEYSCORE is reported to receive unfiltered internet communication sessions ('full-take') from WEALTHYCLUSTER2. The session data is stored for a short period of time: content is buffered for 3 to 5 days (sometimes shorter or sometimes longer, depending on the amount of traffic), and metadata for up to 30 days. In other words, XKEYSCORE creates a rolling buffer that is continually being rewritten. This buffering enables analysts to perform federated queries using so-called "soft selectors", like keywords, against the body texts of e-mail and chat messages, digital documents, and spreadsheets in English, Arabic and Chinese. XKEYSCORE also allows analysts to look for the usage of encryption, the use of a VPN or the TOR network, and a number of other things that could lead to a target. | ||
| − | Analysts can create so-called 'fingerprints', rules that contain search terms (especially all the correlated identities of a certain target https://www.emptywheel.net/2014/04/09/fingerprints-and-the-phone-dragnets-secret-correlations-order/) that are automatically executed by the system. Some examples of XKeyscore fingerprints were disclosed by German regional television on July 3, 2014 | + | Analysts can create so-called 'fingerprints', rules that contain search terms (especially all the correlated identities of a certain target <ref>Fingerprints and the Phone Dragnet’s Secret “Correlations” Order https://www.emptywheel.net/2014/04/09/fingerprints-and-the-phone-dragnets-secret-correlations-order/ |
| − | + | </ref>) that are automatically executed by the system. Some examples of XKeyscore fingerprints were disclosed by German regional television on July 3, 2014 <ref>Example of XKEYSCORE fingerprinting rules http://daserste.ndr.de/panorama/xkeyscorerules100.txt</ref>, who presented them as excerpts of source code. | |
| − | + | ||
| − | The epochal batch of leaks on TAO's hacking unit and ANT division catalog used is typical COMINT. <ref>Leaksource: NSA’s ANT Division Catalog of Exploits for Nearly Every Major Software/Hardware/Firmware http://leaksource.info/2013/12/30/nsas-ant-division-catalog-of-exploits-for-nearly-every-major-software-hardware-firmware/</ref>. See [[Digital threats, detection, protection and (counter) moves#Targeted_surveillance| | + | ==== Tailored Access Operations (TAO) ==== |
| + | The epochal batch of leaks on TAO's hacking unit and ANT division catalog used is typical COMINT. <ref>Leaksource: NSA’s ANT Division Catalog of Exploits for Nearly Every Major Software/Hardware/Firmware http://leaksource.info/2013/12/30/nsas-ant-division-catalog-of-exploits-for-nearly-every-major-software-hardware-firmware/</ref>. See [[Digital threats, detection, protection and (counter) moves#Targeted_surveillance|targeted surveillance threats]] for some examples. | ||
=== DEA === | === DEA === | ||
| Line 76: | Line 93: | ||
The Hemisphere Project is coordinated from the Los Angeles Clearinghouse and is funded by the US Office of National Drug Control Policy (ONDCP) and DEA. Hemisphere provides electronic call detail records (CDRs) in response to federal, state, and local administrative/grand jury subpoenas. In effect, it is mass surveillance conducted by US telephone company AT&T in collaboration with the DEA (AT&T supplying DEA officials with metadata from a database of telephone calls dating back to 1987). | The Hemisphere Project is coordinated from the Los Angeles Clearinghouse and is funded by the US Office of National Drug Control Policy (ONDCP) and DEA. Hemisphere provides electronic call detail records (CDRs) in response to federal, state, and local administrative/grand jury subpoenas. In effect, it is mass surveillance conducted by US telephone company AT&T in collaboration with the DEA (AT&T supplying DEA officials with metadata from a database of telephone calls dating back to 1987). | ||
| + | |||
| + | * AT&T & Verizon eager to get on their knees for the NSA https://www.propublica.org/article/nsa-spying-relies-on-atts-extreme-willingness-to-help | ||
| + | * How they connected the dots, supporting documents https://www.propublica.org/article/a-trail-of-evidence-leading-to-atts-partnership-with-the-nsa | ||
=== CIA === | === CIA === | ||
| Line 116: | Line 136: | ||
</ref>, now in use by CIA, DEA, DIA, FBI, and NSA. There seems to be no oversight. | </ref>, now in use by CIA, DEA, DIA, FBI, and NSA. There seems to be no oversight. | ||
| − | === | + | === MUSCULAR === |
| + | MUSCULAR is one of at least four other similar programs that rely on a trusted 2nd party, programs which together are known as WINDSTOP. MUSCULAR is jointly run by the NSA and GCHQ. It operates via an access point outside the United States, and relies on an unnamed telecommunications operator to provide secret access for the NSA and the GCHQ. | ||
== (Counter) moves == | == (Counter) moves == | ||
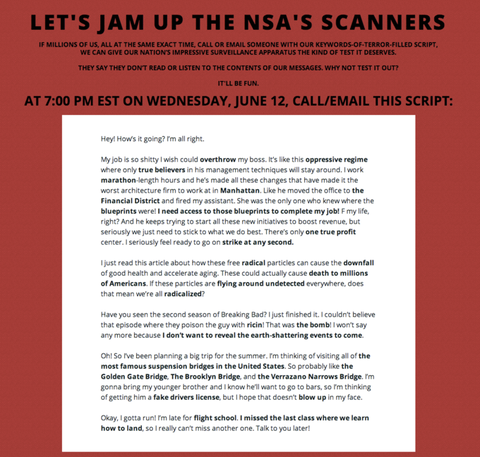
[[File:Operationtrollthensa.png|480px|thumb|right|http://trollthensa.com/]] | [[File:Operationtrollthensa.png|480px|thumb|right|http://trollthensa.com/]] | ||
| + | |||
| + | === Communications privacy folly === | ||
| + | In reply to a request for comments on Mexico law revisions – Warrantless Real-time Cell phone Geolocation Data Surveillance, Cryptome comments - This is the short version of why there can be no solution to preventing communication systems abuse <ref>Communications Privacy Folly http://cryptome.org/2012/06/comms-folly.htm</ref>. | ||
| + | |||
| + | Knowing that, what if we make spying on us as expensive as possible using '''lawful''' techniques and tools? | ||
=== Understanding and minimising our digital shadows === | === Understanding and minimising our digital shadows === | ||
The internet is a great space to explore, learn, speak up, listen and communicate with people across the world. Unfortunately, the internet has also become a space where people who challenge the dominant discourse often find themselves under attack. These attacks can be very personal - enabled by the fact that there is often a lot of personal information about us on the internet. | The internet is a great space to explore, learn, speak up, listen and communicate with people across the world. Unfortunately, the internet has also become a space where people who challenge the dominant discourse often find themselves under attack. These attacks can be very personal - enabled by the fact that there is often a lot of personal information about us on the internet. | ||
| − | To strengthen our defences against these kinds of attacks, it’s a good idea to start by our assessing our | + | To strengthen our defences against these kinds of attacks, it’s a good idea to start by our assessing our digital shadows. These shadows - can tell a story about us: who we are, where we live and hang out, what we are interested in, and who our friends and colleagues are. For more on that see [[Step 1#Understanding_and_minimising_our_digital_shadows|Understanding and minimising our digital shadows]]. |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
=== Controlled folly === | === Controlled folly === | ||
| − | + | And continued from there, what if we make spying on us as expensive as possible using lawful techniques and tools? And if need be we invent new (GNU and creative commons licensed) techniques and tools? <ref>Portal - 'Still Alive' https://www.youtube.com/watch?v=Y6ljFaKRTrI</ref> | |
| + | |||
| + | As Cory Doctorow writes: ''There is no legal or technical mechanism by which code that is designed to be modified by its users can co-exist with a rule that says that code must treat its users as adversaries and seek to prevent them from running prohibited code. ''<ref>What David Cameron just proposed would endanger every Briton and destroy the IT industry http://boingboing.net/2015/01/13/what-david-cameron-just-propos.html | ||
</ref> | </ref> | ||
| − | + | ||
| − | + | See [[Scenario planning]] to prepare for some [[roleplay]], for adding a "red copper armour" for online roleplay see [[Digital threats, detection, protection and (counter) moves]], [[Installing linux]] and [[Linux security|securing]] it as best as you can and fits your context and purpose, and see [[Confusing surveillance systems|confusing of surveillance systems]] for teh lulz. | |
| − | + | ||
| − | + | ||
| − | + | ||
=== Political ecology === | === Political ecology === | ||
| Line 148: | Line 168: | ||
''I think the keyword of systemic change already exists: political ecology. There are many people working in that direction. But the universities, cultural systems, professional association (including unions) and press/media apparatuses are still massively captured by the dream of belonging to the transnational capitalist class, or mired in some vague nostalgia for the klarion calls of yesterday's struggles. Meanwhile our old nettime nemesis, the Californian Ideology, has made tremendous forward strides.'' | ''I think the keyword of systemic change already exists: political ecology. There are many people working in that direction. But the universities, cultural systems, professional association (including unions) and press/media apparatuses are still massively captured by the dream of belonging to the transnational capitalist class, or mired in some vague nostalgia for the klarion calls of yesterday's struggles. Meanwhile our old nettime nemesis, the Californian Ideology, has made tremendous forward strides.'' | ||
| − | ''Just how far will we let it go?'' | + | ''Just how far will we let it go?'' It's that infamous gut/head conversation and it seems the gut is winning, isn't it? |
| + | |||
| + | === Question the surveillance system === | ||
| + | Examples that flew by: | ||
| + | * Why do we upgrade firmware? Many HW installations never add functionality. | ||
| + | * Why doesn't Brazil yank the cable splitter on their sovereign ground at Fortaleza and tell users they did? | ||
| + | * Why doesn't Germany seize the Einstein/Castanet RF illuminators on the roofs of the US, Canadian and British embassies? | ||
| + | * Why doesn't Orange file their threatened lawsuit over the SEA-ME-WE4 data theft? | ||
| + | * Why doesn't Google give us an explanation of where and how the Level Three data theft occurred? | ||
| + | * Why doesn't Apple tell us all the ways TAO has been hacking the iOS and if they're still ongoing? | ||
| + | * Why do only 8 of 24,000 attendees to RSA security conference cancel their attendance? | ||
== Resources == | == Resources == | ||
| − | === News | + | === News & watchdogs === |
* Bugged Planet http://buggedplanet.info/ | * Bugged Planet http://buggedplanet.info/ | ||
* CanaryWatch https://www.canarywatch.org/ | * CanaryWatch https://www.canarywatch.org/ | ||
| Line 172: | Line 202: | ||
* All Watched Over by Machines of Loving Grace http://topdocumentaryfilms.com/all-watched-over-by-machines-of-loving-grace/ | * All Watched Over by Machines of Loving Grace http://topdocumentaryfilms.com/all-watched-over-by-machines-of-loving-grace/ | ||
| − | === Presentations and | + | === Presentations and articles === |
| − | |||
* Dear NSA, let me take care of your slides http://www.slideshare.net/EmilandDC/dear-nsa-let-me-take-care-ou | * Dear NSA, let me take care of your slides http://www.slideshare.net/EmilandDC/dear-nsa-let-me-take-care-ou | ||
| − | ' | + | * Mind-blowing secrets of NSA's security exploit stockpile revealed at last http://www.theregister.co.uk/2015/09/04/nsa_explains_handling_zerodays/ |
| + | |||
| + | === Targeted surveillance === | ||
| + | |||
| + | * Hacking Team: a zero-day market case study https://tsyrklevich.net/2015/07/22/hacking-team-0day-market/ | ||
| + | * NSA QUANTUM Spies with Radio Signals https://cryptome.org/2014/01/nsa-quantum-radio.htm | ||
| + | |||
| + | === Hardware implants === | ||
* Getting Terminal Access to a Cisco Linksys E-1000 https://www.trustwave.com/Resources/SpiderLabs-Blog/Getting-Terminal-Access-to-a-Cisco-Linksys-E-1000/ | * Getting Terminal Access to a Cisco Linksys E-1000 https://www.trustwave.com/Resources/SpiderLabs-Blog/Getting-Terminal-Access-to-a-Cisco-Linksys-E-1000/ | ||
* Oops, I pwned your router https://www.trustwave.com/Resources/SpiderLabs-Blog/Oops,-I-pwned-your-router--Part-One/ | * Oops, I pwned your router https://www.trustwave.com/Resources/SpiderLabs-Blog/Oops,-I-pwned-your-router--Part-One/ | ||
* Hackers create spy plug inspired by the NSA's surveillance kit http://www.dailymail.co.uk/sciencetech/article-2920419/When-USBs-attack-Hackers-create-covert-spy-plug-inspired-NSA-s-Cottonmouth-surveillance-kit.html | * Hackers create spy plug inspired by the NSA's surveillance kit http://www.dailymail.co.uk/sciencetech/article-2920419/When-USBs-attack-Hackers-create-covert-spy-plug-inspired-NSA-s-Cottonmouth-surveillance-kit.html | ||
* Infosec institute: NSA Backdoor Part 2, BULLDOZER: And, Learn How to DIY a NSA Hardware Implant http://resources.infosecinstitute.com/nsa-bios-backdoor-aka-god-mode-malware-part-2-bulldozer/ | * Infosec institute: NSA Backdoor Part 2, BULLDOZER: And, Learn How to DIY a NSA Hardware Implant http://resources.infosecinstitute.com/nsa-bios-backdoor-aka-god-mode-malware-part-2-bulldozer/ | ||
| − | + | ||
| + | === Radio frequency exfiltration === | ||
* Wireless Data Exfiltration - building and using low cost signal intelligence Tools http://www.slideshare.net/warezjoe/ccdc-2012-wireless-data-exfiltration-building-and-using-low-cost-signal-intelligence-devices-v2 | * Wireless Data Exfiltration - building and using low cost signal intelligence Tools http://www.slideshare.net/warezjoe/ccdc-2012-wireless-data-exfiltration-building-and-using-low-cost-signal-intelligence-devices-v2 | ||
* Getting Started with HackRF and GNU Radio https://github.com/mossmann/hackrf/wiki/Getting-Started-with-HackRF-and-GNU-Radio | * Getting Started with HackRF and GNU Radio https://github.com/mossmann/hackrf/wiki/Getting-Started-with-HackRF-and-GNU-Radio | ||
| − | + | ||
| + | === Infected firmware === | ||
* Implementing and Detecting a PCI Rootkit http://www.blackhat.com/presentations/bh-dc-07/Heasman/Paper/bh-dc-07-Heasman-WP.pdf | * Implementing and Detecting a PCI Rootkit http://www.blackhat.com/presentations/bh-dc-07/Heasman/Paper/bh-dc-07-Heasman-WP.pdf | ||
* To Protect And Infect, Part 2 [30c3] https://www.youtube.com/watch?v=vILAlhwUgIU | * To Protect And Infect, Part 2 [30c3] https://www.youtube.com/watch?v=vILAlhwUgIU | ||
| + | |||
| + | === Authorship analysis === | ||
| + | * An Authorship Analysis: Francis Bacon as Shake-speare: http://fly.hiwaay.net/~paul/outline.html | ||
| + | * The jargon file: http://www.comedia.com/hot/jargon-4.4.6/html/ | ||
| + | |||
| + | === Wiretapping === | ||
| + | * University of Pennsylvania Researcher Reports JitterBugs Could Turn Your Keyboard Against You, Steal Data http://www.upenn.edu/pennnews/news/university-pennsylvania-researcher-reports-jitterbugs-could-turn-your-keyboard-against-you-stea (2006) | ||
== Related == | == Related == | ||
| Line 197: | Line 242: | ||
* [[Biometrics]] | * [[Biometrics]] | ||
| − | + | [[Category:How_To]] | |
| + | [[Category:Resources]] | ||
Latest revision as of 15:33, 9 February 2017
A citizenry that’s constantly on guard for secret, unaccountable surveillance is one that’s constantly being remade along the lines the state would prefer. Foucault illustrated this point by reference to a hypothetical prison called the Panopticon. Designed by utilitarian philosopher Jeremy Bentham, the Panopticon is a prison where all cells can be seen from a central tower shielded such that the guards can see out but the prisoners can’t see in.
The prisoners in the Panopticon could thus never know whether they were being surveilled, meaning that they have to, if they want to avoid running the risk of severe punishment, assume that they were being watched at all times. Thus, the Panopticon functioned as an effective tool of social control even when it wasn’t being staffed by a single guard.
This page is an ongoing effort and forever under construction.
Contents
Technocracy
The logic of this system is, in a limited sense, highly logical: past elites were unable to maintain control due to human mistakes and unpredictabilities. The thinking behind a technocracy is that machines make no mistakes (this is a weakness of theirs). The large tech companies have all discussed this openly at large conferences. Money is a symbol of energy, and the erection of the mass surveillance grid is not for the purpose of security or preventing 'terrorism'. [1]
Surveillance
Dragnet surveillance
Every citizen on this planet is subject to mass surveillance. This includes data that does not, by itself, identify individuals, but sits in various databases until analysts do a search for a particular name. Then network analysts connect within two degrees and surveil others.
There are important details about these programs that need to be filled in. A large amount of information is supposedly already in the public domain but consists mainly of presentations with a kazillion names in 'em (that can easily be altered). This page attempts to make sense of the spaghetti.
Targeted surveillance
Journalists and observers working on reporting on projects like national security, leaks, environmental issues, activist coverage, demonstration coverage, waste and abuse in governments, human rights, crime, may be targeted by state and private actors. Scenarios where people are being followed require a bit more thinking than installing and using tools on our machines.
Legalities
The Snowden leaks (see timeline masters of the internet) revealed a massive surveillance program including interception of email and other internet communications and phone call tapping. Some of it appears illegal, while other documents show the US spying on friendly nations during various international summits, and on its citizens. The programs are enabled by two US laws, the Patriot Act[2] and the FISA Amendments Act (FAA)[3], and a side dish called Executive Order 12.333[4]. Although the Foreign Intelligence Surveillance Court oversees such surveillance activities, it operates in secrecy through one-sided procedures that favour the US government.
Executive Order 12333 (EO12333)
Executive Order 12333 - 1.13 allows the FBI to provide the NSA with "technical assistance" in the United States, i.e. to collect metadata about American citizens by collaborating with "foreign intelligence" and law enforcement services. [5] By using telecom companies the US government can circumvent controls and accountability that don't apply to companies. All major telecom companies have worked closely and secretly with government spying since their inceptions.
Plausible Deniability
Plausible deniability began under Central Intelligence Agency (CIA) director Allen Dulles [6]. The CIA black ops division undertakes dangerous and usually what would be considered illegal missions that are not officially sanctioned by the US administration so that the administration, which usually benefits from such missions, can safely disavow any knowledge of them in the event of their publically uncovered success or failure. The administration is in the position of plausible deniability towards the CIA's actions [7].
Intelligence
There are six overarching categories that describe the various ways that intelligence is collected: SIGINT, HUMINT, MASINT, GEOINT, OSINT and IMINT. Of these, SIGINT and HUMINT are considered instrumental in the "war on terror".
SIGINT and security procedures are closely coordinated under what is called the UKUSA Community, or "five eyes": Australia, Canada, New Zealand, the United Kingdom, and the United States.
Signals Intelligence (SIGINT)
Signals intelligence, or SIGINT, is the process of intercepting signals between people (COMINT) or from electronic signals not directly used in communication (ELINT), or communications transmitted electronically such as through radars, radios, and weapon systems. One of the main tools that SIGINT employs is the use of cryptanalysis, which is the process of breaking codes in order to read encrypted information.
The National Security Agency (NSA) is the organisation that is responsible for SIGINT. The NSA SIGINT Strategy 2012-2016 covers all the comsec and crypto initiatives to covertly exploit people, cryptographers, anonymisers, informants, planted spies, security firms, networks, governments, nations [8].
Communications Intelligence (COMINT)
Communications intelligence deals with voice communications commonly over radios. This is used to gather information such as location and identity. It covers all electronic communications in the US and the world "to ensure national security". The NSA at Ft Meade, Maryland has had the most advanced computers in the world since the 60s. Technology is developed and implemented in secret.
Electronic Intelligence (ELINT)
ELINT is divided into Technical ELINT (TechELINT) and Operational ELINT (OpELINT). Technical ELINT obtains signal structure, emission characteristics, modes of operation, emitter functions, and weapons systems associations of such emitters as radars, beacons, jammers, and navigational signals for determining its capabilities and role in a larger system as part of electronic warfare; Operational ELINT focuses on locating specific ELINT targets and determining operational patterns of the systems named Electronic Order of Battle (EOB) for supporting military operational planners and tactical military commanders on the battlefield. And ofcourse there are "counter" programs, existing and under development such as Electronic counter-countermeasures (ECCM) in the US and electronic protective measures (EPM) in Europe, Wild Weasel (alias Iron Hand or SEAD), Smart Dust and Wolfpack.
Human Intelligence (HUMINT)
This is the gathering of information from human sources. Interrogation and elicitation would be classified under this heading.
The Central Intelligence Agency (CIA) is responsible for overseeing the majority of HUMINT operations, although the military (DoD) is often involved in HUMINT as well. Both parties make use of two main tactics, gathering intelligence through interrogations and through conversations with key persons who have access to valuable information. HUMINT sources of information include diplomats, military attaches, prisoners of war, and espionage.
Foreign Instrumentation Signals Intelligence (FISINT)
TELINT (Telemetry Intelligence), later named FISINT (Foreign Instrumentation Signals Intelligence) used for intercepting, processing, and analysis of foreign telemetry is closely related to TechELINT and conducted by DoD.
Operations
NSA
The Special Sources Operation (SSO) gathers information from internet communications through arrangements with internet companies under the program codenamed PRISM, and by Upstream collection (cable tapping).
PRISM
PRISM is part of the overall NSA surveillance effort - a program authorised in the united states under the FISA Amendments Act (FAA), now located in Section 702 of the FISA, that allows the NSA to collect communications of specifically identified foreign targets.
When people in the rest of the world use the net, they are effectively using US-based services, making them a legal target for US intelligence. Supposedly the NSA has no "direct access" to the servers of companies through PRISM - other agencies, like the FBI, collect the data. Emails, chat--video, voice, photos, stored data, VoIP, file transfers, video conferencing, notifications of target activity--logins, etc, online social networking details, and special requests are collected from nine major Silicon Valley technology companies: Facebook, Google, Yahoo, Microsoft, PalTalk, Skype, YouTube, Apple, and AOL. [9]
Upstream collection
FAIRVIEW seems to be the main umbrella program, incorporating many different operations, such as BLARNEY, STORMBREW, and OAKSTAR (yet another umbrella for eight different programs used for collection outside the US), that intercept massive amounts of international Internet traffic by various means, and involves the collection of communications — both their metadata and their content — as they pass through undersea fiber-optic cables in:
- Cooperation with telecommunication companies
- Cooperation with foreign intelligence agencies
- Unilateral cable tapping operations
The five biggest collection programs of the Special Source Operations division are DANCINGOASIS, SPINNERET, MOONLIGHTPATH, INCENSER and AZUREPHOENIX. The largest cable tapping program appears to be DANCINGOASIS (DGO) [10]. It could be that DANCINGOASIS is another umbrella program encompassing various smaller sub-programs.
Upstream collection also includes data from MUSCULAR in a joint operation with the GCHQ.
Internet data collected by Upstream programs can be processed and searched though the XKEYSCORE indexing and analysing system. BOUNDLESS INFORMANT tracks the international intelligence gathering techniques of the NSA.
XKEYSCORE
XKEYSCORE is reported to receive unfiltered internet communication sessions ('full-take') from WEALTHYCLUSTER2. The session data is stored for a short period of time: content is buffered for 3 to 5 days (sometimes shorter or sometimes longer, depending on the amount of traffic), and metadata for up to 30 days. In other words, XKEYSCORE creates a rolling buffer that is continually being rewritten. This buffering enables analysts to perform federated queries using so-called "soft selectors", like keywords, against the body texts of e-mail and chat messages, digital documents, and spreadsheets in English, Arabic and Chinese. XKEYSCORE also allows analysts to look for the usage of encryption, the use of a VPN or the TOR network, and a number of other things that could lead to a target.
Analysts can create so-called 'fingerprints', rules that contain search terms (especially all the correlated identities of a certain target [11]) that are automatically executed by the system. Some examples of XKeyscore fingerprints were disclosed by German regional television on July 3, 2014 [12], who presented them as excerpts of source code.
Tailored Access Operations (TAO)
The epochal batch of leaks on TAO's hacking unit and ANT division catalog used is typical COMINT. [13]. See targeted surveillance threats for some examples.
DEA
Hemisphere
The Hemisphere Project is coordinated from the Los Angeles Clearinghouse and is funded by the US Office of National Drug Control Policy (ONDCP) and DEA. Hemisphere provides electronic call detail records (CDRs) in response to federal, state, and local administrative/grand jury subpoenas. In effect, it is mass surveillance conducted by US telephone company AT&T in collaboration with the DEA (AT&T supplying DEA officials with metadata from a database of telephone calls dating back to 1987).
- AT&T & Verizon eager to get on their knees for the NSA https://www.propublica.org/article/nsa-spying-relies-on-atts-extreme-willingness-to-help
- How they connected the dots, supporting documents https://www.propublica.org/article/a-trail-of-evidence-leading-to-atts-partnership-with-the-nsa
CIA
The National Clandestine Service (NCS) is the branch of the CIA responsible for the collection of HUMINT.
FBI
PRISM
The FBI has its own capacity to monitor phone, email, chats, etc., in addition to whatever NSA shares with them and seems to be doing quite well obtaining what it needs by collecting all the data everywhere via subpoenas, though there are abundant reasons to worry about control functions in FBI’s bulky databases. PRISM, an NSA program, is apparently coordinated through the FBI. [14]
Data Intercept Technology Unit (DITU)
The Data Intercept Technology Unit (DITU) has been described as NSA's Alter Ego in the FBI. It carries out its own signals intelligence operations and is trying to collect huge amounts of email and internet data from U.S. companies — an operation that the NSA once conducted, was reprimanded for, and says it abandoned.
Digital Collection System Network (DCSNet)
The Digital Collection System Network (DCSNet) is a suite of software that collects, sifts and stores phone numbers, phone calls and text messages. The system directly connects FBI wiretapping outposts around the US to a far-reaching private communications network. DCSNet includes at least three collection components, each running on Windows-based computers:
- DCS-3000 (alias Red Hook) handling pen-registers and trap-and-traces, a type of surveillance that collects signaling information -- primarily the numbers dialed from a telephone -- but no communications content. (Pen registers record outgoing calls; trap-and-traces record incoming calls.)
- DCS-6000 (alias Digital Storm) captures and collects the content of phone calls and text messages for full wiretap orders.
- DCS-5000 is used for targeted surveillance wiretaps (targeting spies or terrorists).
DoD
Defense Information Systems Agency (DISA)
The Defense Information Systems Agency (DISA), is a United States Department of Defense (DoD) combat support agency composed of military, federal civilians, and contractors. DISA provides information technology (IT) and communications support to the president, vice president, secretary of defense, the military services, the combatant commands, and any individual or system contributing to the defense of the United States.
GCHQ
During the 1950’s, the uk government became concerned that emanations could be captured and then reconstructed. Obviously, the emanations from a blender aren’t important (at least not then, now they may become important in the "internet of things"), but emanations from an electric encryption device would be. If the emanations were recorded, interpreted, and then played back on a similar device, it would be extremely easy to reveal the content of an encrypted message. Research showed it was possible to capture emanations from a distance, and as a response, the TEMPEST program was started. [15]
MUSCULAR
Appears to be a back-door collection from Google and Yahoo private clouds.
Sharing of data
PROTON/CRISSCROSS/ICREACH
PROTON is a storage and analysis system of telecommunications selectors at the TS/SI/FISA/ORCON/NOFORN level of classification and handling. PROTON is the program name as well as the name of the technology. It has been described as "SAP-like", and is suspected to have started life as a DEA special program.
CRISSCROSS/PROTON is a data sharing system launched in 1990 by the CIA and the DEA. By 1999, the NSA, the Defense Intelligence Agency, and the FBI had gained access to CRISSCROSS and were contributing information to it. As CRISSCROSS continued to expand, it was supplemented with a system called PROTON that enabled analysts to store and examine additional types of data. [16]
After 9/11, the NSA came to view CRISSCROSS/PROTON as insufficient, and believed it was time to build a new and more advanced system to radically increase metadata sharing for HUMINT: ICREACH [17], now in use by CIA, DEA, DIA, FBI, and NSA. There seems to be no oversight.
MUSCULAR
MUSCULAR is one of at least four other similar programs that rely on a trusted 2nd party, programs which together are known as WINDSTOP. MUSCULAR is jointly run by the NSA and GCHQ. It operates via an access point outside the United States, and relies on an unnamed telecommunications operator to provide secret access for the NSA and the GCHQ.
(Counter) moves
Communications privacy folly
In reply to a request for comments on Mexico law revisions – Warrantless Real-time Cell phone Geolocation Data Surveillance, Cryptome comments - This is the short version of why there can be no solution to preventing communication systems abuse [18].
Knowing that, what if we make spying on us as expensive as possible using lawful techniques and tools?
Understanding and minimising our digital shadows
The internet is a great space to explore, learn, speak up, listen and communicate with people across the world. Unfortunately, the internet has also become a space where people who challenge the dominant discourse often find themselves under attack. These attacks can be very personal - enabled by the fact that there is often a lot of personal information about us on the internet.
To strengthen our defences against these kinds of attacks, it’s a good idea to start by our assessing our digital shadows. These shadows - can tell a story about us: who we are, where we live and hang out, what we are interested in, and who our friends and colleagues are. For more on that see Understanding and minimising our digital shadows.
Controlled folly
And continued from there, what if we make spying on us as expensive as possible using lawful techniques and tools? And if need be we invent new (GNU and creative commons licensed) techniques and tools? [19]
As Cory Doctorow writes: There is no legal or technical mechanism by which code that is designed to be modified by its users can co-exist with a rule that says that code must treat its users as adversaries and seek to prevent them from running prohibited code. [20]
See Scenario planning to prepare for some roleplay, for adding a "red copper armour" for online roleplay see Digital threats, detection, protection and (counter) moves, Installing linux and securing it as best as you can and fits your context and purpose, and see confusing of surveillance systems for teh lulz.
Political ecology
In my opinion, the predicament we’re in has been woven of threads that include our evolved neuropsychology, our innate cleverness, our general lack of wisdom, and the technological and cultural structures that we have created around us. We may be able to work our way free of this monkey trap, but not unless we gain insight into our own nature, lovingly nurture the wisdom we need to recognize what we’re doing, and the courage to say “No” to some of it. If we can do that, the problems of nuclear power and all the rest will become much less threatening. Can we accomplish such a radical transformation of human consciousness? We are getting a wake-up call. it’s time for us to heed it, and to do a bit of growing up. ~ Slaying The Hydra [21]
Brian Holmes writes, I don’t think any alternative will be possible until certain realities are faced, not just by fringe figures like ourselves but by much broader swathes of society, and that seems unlikely [22]: Sadly, I must report that up to now, almost no one has been interested. Left-leaning intellectuals are still preoccupied by individual liberation, minority and sectoral rights claims, the ghosts of working-class struggles, and anarchist longings for direct democracy. All of those have been very important, but none of the current oppositional discourses can marshall the sophistication, depth, durability and power to confront the transnational capitalist class. An alternative is not something that one fabricates on the fly, in a study or an artwork or or a hacklab or an affinity group or a church or a social center, even if all of those can be part of it. To make it real would require a large-scale articulation of theory and practice, extending into mainstream institutions even while outstripping and transforming them. Obviously it's easier said than done, but without saying it you can't get anywhere. The silence of the intellectuals is the new treason of the clercs.
I think the keyword of systemic change already exists: political ecology. There are many people working in that direction. But the universities, cultural systems, professional association (including unions) and press/media apparatuses are still massively captured by the dream of belonging to the transnational capitalist class, or mired in some vague nostalgia for the klarion calls of yesterday's struggles. Meanwhile our old nettime nemesis, the Californian Ideology, has made tremendous forward strides.
Just how far will we let it go? It's that infamous gut/head conversation and it seems the gut is winning, isn't it?
Question the surveillance system
Examples that flew by:
- Why do we upgrade firmware? Many HW installations never add functionality.
- Why doesn't Brazil yank the cable splitter on their sovereign ground at Fortaleza and tell users they did?
- Why doesn't Germany seize the Einstein/Castanet RF illuminators on the roofs of the US, Canadian and British embassies?
- Why doesn't Orange file their threatened lawsuit over the SEA-ME-WE4 data theft?
- Why doesn't Google give us an explanation of where and how the Level Three data theft occurred?
- Why doesn't Apple tell us all the ways TAO has been hacking the iOS and if they're still ongoing?
- Why do only 8 of 24,000 attendees to RSA security conference cancel their attendance?
Resources
News & watchdogs
- Bugged Planet http://buggedplanet.info/
- CanaryWatch https://www.canarywatch.org/
- Cryptome http://cryptome.org/
- AllYouEverWantedToKnowAboutTempest http://auriea.org/index.pl/AllYouEverWantedToKnowAboutTempest
- Lux ex Umbra - monitoring Canadian signals intelligence (SIGINT) activities past and present http://luxexumbra.blogspot.ca/
- NSA observer https://www.nsa-observer.net/
- Top Level Communications http://electrospaces.blogspot.fr/
- Watching Them, Watching Us http://www.spy.org.uk/
- WikiLeaks: The Spy Files https://wikileaks.org/the-spyfiles.html
Maps
- Mindmeister NSA map https://www.mindmeister.com/fr/308518551/the-national-security-agency-operates-more-than-500-separate-signals-intelligence-platforms-employs-
Books
- The Shadow Factory, 2008 http://www.bookarmor.com/_files/TSF.pdf
Documentaries
- All Watched Over by Machines of Loving Grace http://topdocumentaryfilms.com/all-watched-over-by-machines-of-loving-grace/
Presentations and articles
- Dear NSA, let me take care of your slides http://www.slideshare.net/EmilandDC/dear-nsa-let-me-take-care-ou
- Mind-blowing secrets of NSA's security exploit stockpile revealed at last http://www.theregister.co.uk/2015/09/04/nsa_explains_handling_zerodays/
Targeted surveillance
- Hacking Team: a zero-day market case study https://tsyrklevich.net/2015/07/22/hacking-team-0day-market/
- NSA QUANTUM Spies with Radio Signals https://cryptome.org/2014/01/nsa-quantum-radio.htm
Hardware implants
- Getting Terminal Access to a Cisco Linksys E-1000 https://www.trustwave.com/Resources/SpiderLabs-Blog/Getting-Terminal-Access-to-a-Cisco-Linksys-E-1000/
- Oops, I pwned your router https://www.trustwave.com/Resources/SpiderLabs-Blog/Oops,-I-pwned-your-router--Part-One/
- Hackers create spy plug inspired by the NSA's surveillance kit http://www.dailymail.co.uk/sciencetech/article-2920419/When-USBs-attack-Hackers-create-covert-spy-plug-inspired-NSA-s-Cottonmouth-surveillance-kit.html
- Infosec institute: NSA Backdoor Part 2, BULLDOZER: And, Learn How to DIY a NSA Hardware Implant http://resources.infosecinstitute.com/nsa-bios-backdoor-aka-god-mode-malware-part-2-bulldozer/
Radio frequency exfiltration
- Wireless Data Exfiltration - building and using low cost signal intelligence Tools http://www.slideshare.net/warezjoe/ccdc-2012-wireless-data-exfiltration-building-and-using-low-cost-signal-intelligence-devices-v2
- Getting Started with HackRF and GNU Radio https://github.com/mossmann/hackrf/wiki/Getting-Started-with-HackRF-and-GNU-Radio
Infected firmware
- Implementing and Detecting a PCI Rootkit http://www.blackhat.com/presentations/bh-dc-07/Heasman/Paper/bh-dc-07-Heasman-WP.pdf
- To Protect And Infect, Part 2 [30c3] https://www.youtube.com/watch?v=vILAlhwUgIU
Authorship analysis
- An Authorship Analysis: Francis Bacon as Shake-speare: http://fly.hiwaay.net/~paul/outline.html
- The jargon file: http://www.comedia.com/hot/jargon-4.4.6/html/
Wiretapping
- University of Pennsylvania Researcher Reports JitterBugs Could Turn Your Keyboard Against You, Steal Data http://www.upenn.edu/pennnews/news/university-pennsylvania-researcher-reports-jitterbugs-could-turn-your-keyboard-against-you-stea (2006)
Related
- Digital threats, detection, protection and (counter) moves
- Timeline masters of the internet
- Covert operations
- Psychological warfare
- Game of drones
- Biometrics