Difference between revisions of "Detect false mobile antennas"
From Gender and Tech Resources
(→What is a fake cell tower?) |
(→What is a fake cell tower?) |
||
| Line 10: | Line 10: | ||
[[File:Imsi-catcher.png|thumb|none|alt=Esquema torre falsa.|Esquema de una torre falsa de celular (modificado de [http://cybernc.com/les-imsi-catchers/ Henri-Olivier]).]] | [[File:Imsi-catcher.png|thumb|none|alt=Esquema torre falsa.|Esquema de una torre falsa de celular (modificado de [http://cybernc.com/les-imsi-catchers/ Henri-Olivier]).]] | ||
| − | By the way they | + | By the way they work IMSI catcher are considered a "man in the middle" attack <ref>https://en.wikipedia.org/wiki/Man-in-the-middle_attack</ref>. This is defined as an attack that acquires the ability to read, insert and modify at will, messages between two parties without any of them knowing that the link between them has been violated. The attacker should be able to observe and intercept messages between the two victims <ref>https://en.wikipedia.org/wiki/IntermediateAccess </ref> |
There is evidence that such devices have been used for surveillance purposes, for example in Ukraine the mobile phones of those attending a large demonstration were tracked and then massively received a text message stating "Dear subscriber, you have been registered As a participant in a mass disturbance "<ref>https://antivigilancia.org/es/2015/06/la-vigilancia-y-la-protesta-social/ </ref>. In Latin America, it is known that governments like Mexico and Colombia have bought such devices. | There is evidence that such devices have been used for surveillance purposes, for example in Ukraine the mobile phones of those attending a large demonstration were tracked and then massively received a text message stating "Dear subscriber, you have been registered As a participant in a mass disturbance "<ref>https://antivigilancia.org/es/2015/06/la-vigilancia-y-la-protesta-social/ </ref>. In Latin America, it is known that governments like Mexico and Colombia have bought such devices. | ||
Revision as of 13:42, 1 February 2017
Contents
The electromagnetic spectrum
The electromagnetic spectrum or electric radio spectrum is not something material, but the space that is in the air that goes from the ground to the highest part of the sky. In this space, bands frequencies through which airplanes, wi-fi, bluetooth, walkie talkies, radios, telephones communicate are organized. The fact that our phones can be 2G, 3G, 4G means that they are using different bands of the electromagnetic space, through which the information circulates.
For more information about the electromagnetic space: https://imagine.gsfc.nasa.gov/science/toolbox/emspectrum1.html https://en.wikipedia.org/wiki/Electromagnetic_spectrum
What is a fake cell tower?
Fake cell towers (also known as IMSI catcher) are devices designed to intercept the traffic of a mobile phone and track the movements of the user's phone [1] pretending to be a "legitimate" cell tower [2].

By the way they work IMSI catcher are considered a "man in the middle" attack [3]. This is defined as an attack that acquires the ability to read, insert and modify at will, messages between two parties without any of them knowing that the link between them has been violated. The attacker should be able to observe and intercept messages between the two victims [4]
There is evidence that such devices have been used for surveillance purposes, for example in Ukraine the mobile phones of those attending a large demonstration were tracked and then massively received a text message stating "Dear subscriber, you have been registered As a participant in a mass disturbance "[5]. In Latin America, it is known that governments like Mexico and Colombia have bought such devices.
Unfortunately fake cell towers are becoming easier to get and their price can be as low as $ 500. Depending on the model there is evidence that not only can intercept the traffic of a phone but also can also inject malware.
¿Cómo detectarlas?
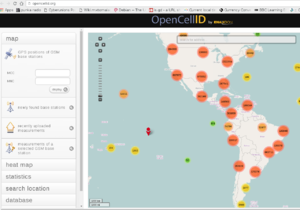
Un primer paso consistiría en poder contar con una base de datos de las torres de celular "legítimas" es decir las que las compañías que proveen estos servicios reconocen y cuentan con los permisos de operación necesarios. Existen algunas bases de datos como:
http://opencellid.org/
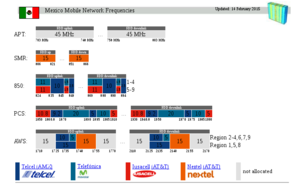
También hay existe información sobre la frecuencia en la que operan: http://www.spectrummonitoring.com/frequencies/frequencies2.html#Mexico
Y del desarrollo de la red GSM:
http://www.spectrummonitoring.com/frequencies/frequencies2.html#Mexico
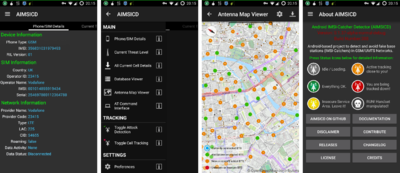
Existen también algunas aplicaciones que se pueden descargar desde el siguiente repositorio libre de apps:
F-Droid es un repositorio de software (o "tienda de aplicaciones") para las aplicaciones de Android, funciona de manera similar a la tienda de Google Play, pero sólo contiene software libre y de código abierto.1 Las aplicaciones pueden buscarse e instalarse desde la página web de F-Droid o directamente desde la aplicación (la cual no está disponible en Google Play store pero puede ser instalada mediante sideloading (transferir fichero desde ordenador a dispositivo móvil).La aplicación de F-Droid actualizará de forma automática las aplicaciones descargadas de este mismo. Además la web ofrece el código fuente de todas las aplicaciones descargables.
Para detectar posibles antenas falsas, puedes descargar desde F-Droid las siguientes aplicaciones:
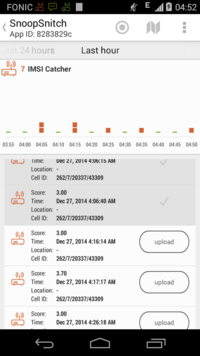
Y desde Google play puedes descargar:
Stingwatch https://www.stingraymappingproject.org/
https://play.google.com/apps/testing/org.stingraymappingproject.sting_watch
¿Como protegerse de las torres falsas de celular?
Si tu teléfono lo permite puedes cambiar sus opciones de configuración para que no se conecte a todas las torres de celular disponibles. Por ejemplo en un celular con Android puedes ir a
Ajustes -> Conexiones inalámbricas y redes -> Más ajustes -> Redes móviles
Y en este punto debes cambiar en
-> Preferencias de red GSM/UTMS
para usar 3G o 4G si te lo permite
-> Operadores de red
Para elegir manualmente la antena a conectar
También si es necesario puedes aislar electro magnéticamente a tu celular, ver por ejemplo: Funda de Faraday para el teléfono[6].
¿Dónde puedo ver más información?
http://wiki.labomedia.org/index.php/GSM
https://quematumovil.pimienta.org/los_imsi-catchers.html- ↑ https://en.wikipedia.org/wiki/IMSI-catcher
- ↑ https://www.eff.org/sls/tech/cell-site-simulators
- ↑ https://en.wikipedia.org/wiki/Man-in-the-middle_attack
- ↑ https://en.wikipedia.org/wiki/IntermediateAccess
- ↑ https://antivigilancia.org/es/2015/06/la-vigilancia-y-la-protesta-social/
- ↑ https://gendersec.tacticaltech.org/wiki/index.php/Funda_de_Faraday_para_el_tel%C3%A9fono_m%C3%B3vil