Difference between revisions of "Complete manual 2"
From Gender and Tech Resources
(→Chapter 2: Safe spaces) |
(→Fixing gender gap in tech) |
||
| (120 intermediate revisions by 4 users not shown) | |||
| Line 5: | Line 5: | ||
Safe spaces can be understood as spaces that are created though explicit community agreement, or through implicit sharing of values. They enable members of a group to flourish, empower themselves and create community. Safe environments for discussion and awareness-raising have played a key role in many women's liberation movements. | Safe spaces can be understood as spaces that are created though explicit community agreement, or through implicit sharing of values. They enable members of a group to flourish, empower themselves and create community. Safe environments for discussion and awareness-raising have played a key role in many women's liberation movements. | ||
| − | + | As explained by integrated security trainer, Sandra Ljubinkovic, safe spaces are important for any integrated approach to security because they enable an environment that support people to express their emotions without fearing any judgment: “Creating a safe space is crucial for creating a sense of physical safety as well as a sense of confidence in a group. It is important for participants who usually have no time to relax to feel comfortable and enjoy simple things. And if they live in a country where their lives are in danger it is even more crucial to make sure that they feel physically safe. Safe space in a group means a space to feel comfortable and speak openly and freely about feelings, challenges, and emotions as they may arise. In the workshops where issues personally affect people (whether those are physical, emotional, or spiritual threats and challenges), participants may have strong emotions as they do their own inner work facing their own oppression, privilege, anger, hurt, pain and suffering”. | |
| − | + | Safe spaces can be temporary and take place during a one time event or training, they can also become permanent spaces when collectives or organisations embed the basic principles of safeness, support, respect and inclusiveness in their own space management. | |
| − | You might assume that the online communities you create or take part in through social media, | + | Whatever format or style is used, a safe space should allow allow women and trans* persons to access and learn about technology and related fields without having to fear sexist language and attitudes, being challenged, mocked or mansplained. There are many possible event formats and styles which can support the creation of safe spaces, both online and offline, to allow women, trans* and other groups to communicate and exchange in a nurturing and welcoming environment. |
| + | |||
| + | You might assume that the online communities you create or take part in through social media, discussion lists and chat channels are inherently democratic, non-hierarchical, participatory and relatively safe. However online spaces often reproduce the same hierarchies, privileges and power relations that exist in society, in the offline world. | ||
It's important to be mindful of this and to think through ways to mitigate and limit these downsides in order to get the best out of our spaces. Using such strategies is about caring for ourselves and for the communities we are part of. Making these issues explicit and visible is also about agency, social justice and feminism, helping us to better shape the spaces we care about, we organise in and within which we grow. | It's important to be mindful of this and to think through ways to mitigate and limit these downsides in order to get the best out of our spaces. Using such strategies is about caring for ourselves and for the communities we are part of. Making these issues explicit and visible is also about agency, social justice and feminism, helping us to better shape the spaces we care about, we organise in and within which we grow. | ||
| − | This section | + | This section, will first look at building safe spaces online for enabling a better and safer collaboration among us through the use of mailing lists, chat, and other collaborative tools such as forums, wikis and pads. It will also look at how to use these tools tactically, in a way that supports the creation and maintenance of safe space. The tools that have been highlighted in this section have been included because they are free and open source, and are designed and administered with increased privacy and security in mind, minimising the amount of traces we leave online. |
| − | + | Second, the section will focus on strategies of resistance in public spaces which are not inherently safe - for instance Twitter and Wikipedia. Those examples are designed to give us insight into how we can create safety online collectively by developing feminist counterspeech, storming and swarming together in order to protect and support each other. | |
| − | + | Finally it will loop back to the offline world and discuss ways to build safe spaces offline in the physical world, such as through women and trans* only or mixed spaces, to learn and Do-it-Together. | |
| − | + | == Collaboration == | |
| − | + | === Mailing lists === | |
| − | + | Mailing lists are one of the oldest forms of social networks, allowing a group to discuss and organise, to exchange information, video, audio and images. A mailing list is a list of addresses to which the same information is sent simultaneously. The most common types of mailing lists are announcement lists and discussion lists. | |
| − | + | If you have decided within your group that you need a secure communication channel and that you do not want to use corporate services, there are some good alternative services to choose from, often recommended for human rights defenders. Riseup, Aktivix and Autistici/Inventati (A/I Collective) are all free services that prioritise security and user privacy. Riseup in particular has many feminist- and queer-oriented lists and is therefore a great place to host your mailing list. On their website you can also have a look at the lists that already exist. | |
| − | + | '''Riseup lists:''' https://lists.riseup.net/www/ | |
| − | + | '''Aktivix lists:''' https://lists.aktivix.org/mailman/listinfo | |
| − | + | ||
| − | + | ||
| − | + | '''Autistici lists:''' http://www.autistici.org/en/services/lists.html | |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | If you or your organisation has your own server you can also install your own software for managing mailing list and ensure that all your communications remains hosted and safe in your own machine and can not be intercepted by unintended third parties. More information at: https://en.wikipedia.org/wiki/Category:Free_mailing_list_software | |
| − | + | ==== Open or closed? ==== | |
| − | + | Once you are ready to create your mailing list you need to decide whether it will be open or closed. | |
| − | + | '''Open:''' An open list allows anyone to subscribe, and then once they have joined the list, to receive announcements or participate in the discussion. Subscription can either be automatic, or it can be approved by a moderator. This type of mailing list is good for reaching out to your potential allies, contributors and followers and keeping them update about your activities. | |
| − | + | '''Closed:''' Another option is to keep your mailing list closed. In a closed list, membership is limited, and all subscribers require approval before they can join the list. It's possible to have a list that is publicised - ie that everyone knows about - but still closed. This type of list is useful when you want to discuss sensitive or personal topics and be sure that all members in the conversation are trustworthy. | |
| − | + | Note that sometimes the archives of a list can be made public to anyone on the web, and will also therefore end up on search engines (like Google). Check if keeping a list open to new subscriptions automatically implies that the archives of the list will be made publicly available, or if they will only be accessible to those who have the subscription password. Sometimes you can choose whether you keep the archives public or not. | |
| + | |||
| + | If you intend to talk about sensitive issues (and talking about gender related topics is often a sensitive issue!) or if trust within the group is important for creating your safe space, you might want to set up a closed list and to keep your archives closed. If you do choose to leave your archives accessible, it is important to inform everyone subscribed to the list that any delicate topic or personal detail that pops up in your discussions will be potentially visible to anybody. | ||
| + | |||
| + | '''Encrypted lists:''' If you want a high level of security, there is also the possibility of encrypting mailing lists. However, it is important to understand that this requires every participants to the list to already use encryption software like PGP or GPG. This type of list, based on software called Schleuder (http://schleuder2.nadir.org/) and developed by Nadir.org, is designed to serve as a tool for group communication, but this time with a strong emphasis on security. | ||
==== Policies ==== | ==== Policies ==== | ||
| − | Agreeing on a mailing list policy from the start will save you a lot of time and difficult conversations. | + | Agreeing on a mailing list policy - a set of do's and don'ts for the list - from the start will save you a lot of time and possibly difficult conversations. Even on a closed list, publishing your policy - which should include the ways in which moderation takes place and how to report violations of the policy, - can be helpful in creating the online safe space you want everyone to feel comfortable in. Your policy can address tensions like the fact that being free to expressing emotion is an important feminist principle, but losing your temper and attacking someone you don't agree with on the list is not ok. In the end any good mailing list policy will set its own rules for achieving a correct balance between freedom of expression and opinion and impeding flames and racist, sexist, or homophobic attacks for instance to take place within the list. |
| + | |||
| + | Having a visible and explicit policy sends a strong message about the value of maintaining the mailing list as a safe space. It can also help you to decide who can be added to your list and who not. To make sure that the policy does not get forgotten, you can regularly remind subscribers about it, with a link at the end of each mail you send out. | ||
| + | |||
| + | '''Relevant links:''' | ||
| + | * Sample mailing list policies that can be adapted and used for your own purposes: for women-only communities (http://geekfeminism.wikia.com/wiki/Statement_of_purpose/Women-only_communities) and for communities including men (http://geekfeminism.wikia.com/wiki/Statement_of_purpose/Communities_including_men). | ||
| + | |||
| + | ==== Administration ==== | ||
| + | |||
| + | '''Administrating a list:''' involves handling subscriptions and moderating content. You can choose how many administrators you want your list to have. Be aware that if your list suddenly becomes very chatty, this might be too demanding for just one person. Besides that, any communication tool including many members should not rely on only one person for administration duties. Take into account that this person could have problems, disapear or simply become abusive because of their power. Because of this, you should include more people helping with administration and moderation duties. A list can also be collectively managed and you can distribute those responsibilities among members of the list. | ||
| + | |||
| + | '''Moderating a list:''' as a general rule, moderation has three main goals. First, a well-moderated community will be more productive and efficient in generating and distributing valuable information and knowledge to its members (subscribers). Second, good moderation will increase the accessibility and openness of online communities by enabling respectful dialogue among its members. Finally, it will lessen the demands on the infrastructure, as well as on the list members. | ||
| + | |||
| + | Remember that any online safe space will apply the basic principles of ''net etiquette'' and that any good administrator, moderator and mailing list policy should review, adapt and include those principles in their core social norms and values and ask members of the list to discuss, understand and accept those. In a nutshell net etiquette requires users to: be nice, learn internet acronyms, keep messages brief, do not shout, protect personal information, help others, and to not send mails if feeling angry! (For more information see: http://www.networketiquette.net/ and https://en.wikipedia.org/wiki/Etiquette_in_technology) | ||
| + | |||
| + | ==== Mailing list examples ==== | ||
| + | |||
| + | Before setting up your own mailing lists, you might want to engage with some of the established mailing lists focused on gender and technology. for example: | ||
| + | |||
| + | Open Mailing lists: | ||
| + | |||
| + | '''Take Back the Tech!:''' the mailing list associated with the collaborative campaign to reclaim information and communication technologies (ICT) to end violence against women (VAW). To register: https://lists.takebackthetech.net/mailman/listinfo/takebackthetech | ||
| + | |||
| + | '''FemTechNet:''' is a network of scholars, students, and artists who work on, with, and at the borders of technology, science, and feminism in a variety of fields including Science and Technology Studies (STS), Media and Visual Studies, Art, Women’s, Queer, and Ethnic Studies. To register: http://femtechnet.newschool.edu/mailman/listinfo/femtechnet | ||
| + | |||
| + | '''Queer Feminism Geek:''' is a network of feminist, queer and trans* hackers, makers, geeks and artists who organise activities and assemblies at the Computer Chaos Camp and Congress. To register: https://lists.riseup.net/www/subscribe/queerfeministgeeks | ||
| + | |||
| + | '''Subscription after endorsement by others on the list:''' | ||
| + | |||
| + | '''Fembot:''' is a network of scholars and students who focus on gender, media & technology. To register: https://lists.uoregon.edu/mailman/listinfo/fembot | ||
| + | |||
| + | '''Femmehack:''' is a list created to organise a Global Feminist Hackathon that took place past 23th of May 2015 in loving memory of Sabeen Mahmud, a Woman Human Right Defender shot to death in Pakistan: https://f3mhack.org | ||
| + | |||
| + | '''TransHackFeminist:''' is a list that was created after the first THF convergence in 2014 where intersectional feminists, queer and trans* people of all genders met to better understand, use and ultimately develop free and liberating technologies for social dissent. It gathers members from all the over the world and uses Spanish and English to communicate: http://transhackfeminist.noblogs.org/files/2015/01/THF_report_Eng.pdf | ||
| − | + | '''Closed mailing lists:''' | |
| − | + | '''Gender and Technology Institute Participants:''' The GTI list is a closed list of people who participated in the Gender and Technology Institute that took place past December 2014, inasmuch as it is opened to people trained by Tactical Technology Collective to privacy and digital security from a gender perspective. | |
| − | + | '''Ada camp:''' is a closed list that is dedicated to speaking about issues related to women in open source. It is composed of the people who participated in Ada Camp: https://adacamp.org/ | |
| − | + | ||
=== Chat with IRC === | === Chat with IRC === | ||
| − | Internet Relay Chat (IRC) is a chat service | + | Internet Relay Chat (IRC) is a chat service which can be hosted on different servers and accessed through different user clients. It provides the ability to set up channels or chatrooms which allow many people to contribute to a discussion in real time. IRC also gives you the option to encrypt your communication. You can’t embed video, audio or pictures, but you can link to them. |
| − | IRC can take a little time to get used depending on the skills in your group. | + | While IRC can be a great tool for facilitating collaboration, there are things to bear in mind if you decide to use it. First, IRC can take a little time to get used to, depending on the skills in your group. Second, developing relationships across a purely text-based channel such as IRC can be challenging. Writing is not easy for everyone; and some in the group might not be using their mother tongue. |
| − | There are several ways to chat through an IRC network. The easiest way to start out is to | + | '''Accessing IRC through your browser:''' There are several ways to chat through an IRC network. The easiest way to start out is to access an IRC network directly through your browser, such as one from Indymedia (https://irc.indymedia.nl/) or Freenode (https://webchat.freenode.net/). You can get set up immediately by creating a nickname and a channel, which you can then give to your colleagues to connect with you. |
| − | + | '''Accessing IRC through a chat client:''' Connecting to an IRC network through your browser is, however, not the most secure option out there. If you are a more advanced user, or if you have already tested out IRC out and think it will work for your group, it can be better to access your chosen IRC network from a chat client. | |
| − | There are | + | There are a few different chat clients which you can choose from, including Jitsi and Pidgin. You can read more about these clients and how to use them on Tactical Tech's Security in-a-Box: Jitsi (https://securityinabox.org/en/guide/jitsi/windows) ; Pidgin (https://securityinabox.org/en/guide/pidgin/windows). |
| − | + | '''How to use a network:''' Advice and instructions on using an IRC network can be found on Freenode (https://freenode.net/using_the_network.shtml), Autistici (https://www.autistici.org/en/stuff/man_irc), and Indymedia (http://docs.indymedia.org/view/Sysadmin/IrcHowTo). The last two also allow us to anonymise our connections through Tor. | |
| − | + | '''Facilitating a meeting:''' Once you start an IRC meeting, it is useful to appoint a facilitator to keep track of time. This person might also be in charge of making sure the discussion sticks to the topics at hand. In order to create a welcoming environment and a safe space, acknowledging and valuing the voice of everyone is key on IRC. When you start a conversation, take time to greet people - in particular newcomers. When facilitating a conversation: | |
| + | |||
| + | * Set a time limit and stick to it because IRC meetings can be very tiring. | ||
| − | + | * You might decide that people should be given turns to speak in order to ensure that everyone has space to express themselves. You can simply assign turns in alphabetical order of nicknames (or any order you want to give) for each of the points addressed. This can help structure the conversation and stop one person or a small group of people dominating the conversation. | |
| − | + | * IRC can go very fast, particularly if there are many people involved in the discussion. Getting everyone to slow down and read all the inputs can decrease frustration. | |
| + | |||
| + | * It can be useful to end your input with “over” or "done", so everyone knows when you have stopped speaking. | ||
| + | |||
| + | Whatever the facilitation methods you choose, communicate them explicitly to all the participants beforehand, for example in the email where you invite people to join the meeting. | ||
| − | + | === Forums, Wikis and Etherpads=== | |
| − | + | Chat services and mailing lists can be extremely useful, but they will only take you so far. When it comes to managing collaboration between people living in different places, you will probably find yourself looking for something with more functionality. | |
| − | + | '''Internet forums:''' One of the oldest tools used for public discussions online are internet forums, where discussions can be hosted over time and are at least temporarily archived. What really distinguishes a forum from a mailing list or IRC chat is that it has a tree-like structure and can contain a number of sub discussions, each with a different topic. | |
| − | + | '''Wikis:''' If you are looking for a tool to collaboratively write a text with many sections, or even to create the initial structure and content for a website, a wiki can be a useful tool. A wiki is a web application that allows for hierarchical structuring of content and tracks the edits and additions of the users, easily allowing you to revert changes, and move and delete content. | |
| − | + | Both forums and wikis need to be hosted on a server, so you'll need to know how to set one up and manage it. | |
| − | + | '''Etherpads''': For collaborating in real-time on documents, Etherpads are a great resource. They are also a good alternative to corporate services like Google Docs, and are far more effective for co-editing text than, for example, sending mails back and forth. The main thing you need to check for in an etherpad is that it is hosted with an encrypted connection (via SSL). A list of such etherpads can be found here: https://github.com/ether/etherpad-lite/wiki/Sites-that-run-Etherpad-Lite. | |
| − | + | * To '''create a new etherpad''' (ie, a new document that you are going to collaborate on), you need to decide on the name of the URL. Because each pad is open to anyone who has the URL, you should give each pad a long and inventive name, so that it can't be easily guessed. For example: https://pad.riseup.net/p/feminists is not secure. A more complicated URL such as https://pad.riseup.net/p/FeministsRockAndTheyWillBeDoingGreatThingsToghether is much more secure. Once the etherpad has been created you can send the URL to your friends and colleagues to start collaborating on a document. | |
| − | If you | + | * If you are worried about your etherpad being found by others, you can also consider a '''password-protected pad'''. For more on this, see: https://www.protectedtext.com/ |
| − | There | + | * Etherpads allow you be anonymous, use a pseudonym or use your real name. There is a colour-based system that differentiates the contributions of each participants on the Etherpad, so you can always see who is contributing what. |
| − | + | == Safe spaces in the public sphere == | |
| + | There are many spaces which will feel inherently unsafe either because they explicitly or implicitly exclude women and trans* people, or because they harbour bigots. There are a number of ways to counter the vulnerability and intimidation we might feel online. One is through caring for our personal and collective safety, through using security -and privacy- enabling tools and techniques and managing safely our online identities. Another is shaping with others methods to reclaim and stay safe in the public sphere. Organising collective actions can be a powerful act of resistance, bringing attention and visibility to the situation and in turn helping to bring about transformation. | ||
| − | + | '''Feminist counterspeech''' - creating counter-narratives online, or "talking back" - is one strategy for making sexism visible and for responding to online attacks and harassment. It can be an effective tactic to create a sense of belonging and make visible the effectiveness of collective feminist actions online. There are many examples of feminist counterspeech in action - many of which you have probably seen and appreciated. The Everyday Sexism Project (https://twitter.com/everydaysexism), for example, catalogues instances of sexism experienced by women on a day-to-day basis; or Byefelipe (https://instagram.com/byefelipe/), the Instagram account which reposts abuse my men who turn hostile when rejected. Feminist counterspeech can also include tactics to enable the inclusion and visibility of women's contributions to knowledge platforms such as Wikipedia. | |
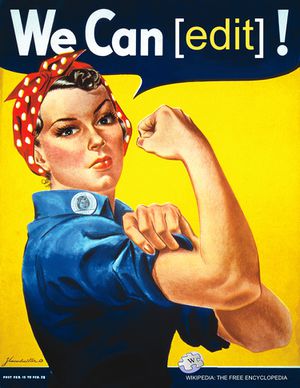
=== Storming Wikipedia === | === Storming Wikipedia === | ||
| − | + | There have been many studies that have criticised the way in which knowledge is produced on Wikipedia. A 2010 survey (https://web.archive.org/web/20100414165445/http://wikipediasurvey.org/docs/Wikipedia_Overview_15March2010-FINAL.pdf) conducted by the United Nations University found that only 13% of Wikipedia contributors identified as female. The fact that Wikipedia’s contributors are mostly men in their twenties and thirties, and disproportionately western, are important factors that influence content. | |
| − | + | Women who have played a significant role in history are also often missing from Wikipedia, and feminist, queer and trans* content is often challenged. | |
| − | + | The lack of gender and cultural diversity in the content on Wikipedia demands creative responses. Because of this partnerships, research, community organizing, socio-cultural and technical interventions should all be considered. | |
| + | |||
| + | '''Storming Wikipedia''' or organising '''Edit-a-thons''' are two possible interventions. These enable participants to learn collectively how to edit and change content to better reflect their communities and histories. Learning how to edit Wikipedia can seem daunting, so collectively editing and creating pages is a great way to confront fears; to Do-It-With-Others (DIWO) in a safe space. Besides you will learn about the Wikipedia community values and principles and how such a large community-driven effort has, through the development of bottom-up social rules, become the most important encyclopedia in the world. All together, Wikipedia remains an important space worth investigating and reclaiming! | ||
| + | |||
| + | Organising a wikistorming involves gathering a group of friends (and friends of friends) who want to learn or already know how to edit Wikipedia, and identify a safe space in which to hold the event. It can be held in someone’s home, in a community centre, at an art centre or at a community organisation. Wikistorming can (and should) of course be organised for any day, but Ada Lovelace Day in mid-October and International Women's Day on March 8 are two specific days on which such gatherings often happen. A wikistorming can last for half to a whole day. Before the wikistorming or as part of it, decide which Wikipedia entries you want create or which existing page you want to edit. Be realistic in your goals and don't put too many edits on your agenda! To edit Wikipedia carefully takes time. | ||
| + | |||
| + | '''Relevant links:''' | ||
| + | * Advice on organising a wikistorming: http://femtechnet.newschool.edu/wikistorming | ||
| + | * Great examples of wiki storming: https://blog.wikimedia.org/2015/03/05/wikipedia-edit-a-thons-international-womens-day/ | ||
| + | * Lectures about the gender gap in wikipedia and how to overcome it: https://meta.wikimedia.org/wiki/Gender_gap | ||
[[File:We Can Edit.jpg|thumbnail|center]] | [[File:We Can Edit.jpg|thumbnail|center]] | ||
| − | === | + | === Dealing with Trolls === |
| + | Women and trans* persons who begin to grow a following and have influence online might experience what Kathy Siera describes as a “koolaid point” (http://seriouspony.com/trouble-at-the-koolaid-point/). This is a point at which a certain group of people decide that you have too much influence, and make it their mission to silence you or discredit you. This is commonly referred to as 'trolling' - although it is more often than not targeted, discriminatory in nature and hate-based. A troll's tactics can include anything from sending constant derogatory and belittling messages, to editing and distributing images, and even making threats. | ||
| − | + | ''Block or engage?'' | |
| − | There are two key ways you can deal with trolls | + | There are two key ways you can deal with trolls. One is to '''block''' them and then '''report''' them to the platform you are using. The other is to engage with them. The decision on which way to go depends on what you want to achieve. |
| − | + | '''Blocking''' trolls can sometimes be effective, and can allow you to continue with your work unimpeded. Projects like Block Together (https://blocktogether.org/) and Block Bot (http://www.theblockbot.com/sign_up) were developed to help people who are harassed share their blocklists with each other. | |
| − | + | When trolls are really committed to harassing you, however, blocking doesn't really help. A determined troll can create numerous different profiles (called “sock puppet accounts”) to continue the harassment, and this means your blocking has to keep up with their new account generation. This quickly becomes very tedious. | |
| − | + | Historically, platforms like Twitter and Facebook have not handled '''reports of intimidation and violence''' very well. However, this is beginning to change, as they recognise the severity of problem and see how it deters people with important voices from using their services. | |
| − | + | You might consider the alternative - '''engaging''' the trolls who are harassing you. One way to do this is to try and enter into rational arguments with them and interrogate their views. Another way is to try to shame them, or to use humour to deflate their egos. Effective engagement with trolls can actually help to generate debate and public interest around the act of harassment, and can involve others online in discussions about safe spaces, violence, sexism and online behaviour. It can also be a source of empowerment for the subjects of trolling: seeing others laugh at your harasser can be very uplifting. | |
| − | + | '''Swarming''' can be another way to drown out the voices of the harassers. This can be done in retro style by creating communities of support with your allies in social media spaces where you are likely to encounter harassment. When someone is being targeted, others can quickly be alerted and bombard the harasser with messages. The content of that message is up to you: it could be scolding, educational, or loving. Another option is: instead of directing messages towards the harasser, the swarm can fill the victim's content stream with lots of new content in order to quickly make the negative, violent content disappear into online history. | |
| − | + | If you want to engage with trolls, or try “swarming”, you might prefer to stay anonymous to avoid having your real identity trolled. Setting up a network of second accounts to do your troll-response work can be a good idea for your organisation or your community of friends. It might be easier too, psychologically, to say some of the things you want to trolls, than you would if the comments were linked to your main identity. And it is more performative: you can create any kind of identity you want and style it with an avatar, a funny name, a character etc. | |
| − | + | ||
| − | + | However, while battling the trolls in the old-fashioned human way can be fun and eye-opening, it can also be a time waster. Another option to consider is automation using '''bots'''. For this you need to do some coding, or you can work with freely available code that someone has already uploaded on a software repository such as Github. | |
| − | + | ===== Bots against trolls ===== | |
| − | + | A bot is a piece of software that runs an automated task over the internet, performing tasks much faster than we can. | |
| − | + | There are many different types of bots. There's the spambot, for example, which harvests email addresses and contact information; and there are also the 1800 approved bots on the English Wikipedia, which help to semi-automate the editing of Wikipedia pages. Bots can post content, gather information and click on things. Twitter is also filled with bots which use algorithms to harvest information and tweet. Many of these are humorous and random - for example @twoheadlines, which grabs random news headlines and combines them to create funny combinations. | |
| − | + | A bot can be programmed to document trolls' activities, or talk to them, so that you don't have to. The possibilities outlined below apply mainly to Twitter; however some of these ideas can be used across other platforms as well. | |
| − | + | '''The data-gathering bot:''' quietly scans Twitter and gathers up tweets, usernames and any other available information you have programmed it to collect. It places this information in a file for you. This bot can be useful for understanding what kind of content is out there, and for doing a first-stage analysis of abuse. Foxxydoxing is such an example; it is intended to help you analyse who your harassers are (https://github.com/DeepLab/FoxyDoxxing). | |
| − | + | '''The simple talking bot:''' if you follow the #gamergate hashtag on Twitter, you will see a bot called @everyethics which tweets different humorous reasons for the #gamergate trolling, ridiculing the claim that the major trolling which has been called "Gamergate" was not about attacking women in gaming but about “ethics in game journalism”. While this bot could be seen as spam, it was actually clearly a strategy to undermine and make fun of the trolls. | |
| − | + | '''The retweet bot:''' is programmed to scan Twitter for a list (created by you) of specific words, phrases or hashtags, and to retweet those. This would be a strategy for documenting and publicising Twitter abuse. Here's an example of such a bot you can download and install yourself (https://lilithlela.cyberguerrilla.org/?p=17418). | |
| + | |||
| + | '''The autotweet bot:''' is similar to the retweet bot except that every time it finds a tweet with one of the words, phrases or hashtags you have programmed it to look for, it will tweet a pre-written tweet directed at that user. These bots get shut down much faster now, as was shown by @fembot, which was programmed to automatically respond to racist and sexist tweets. @fembot was blocked after only 75 tweets. | ||
| + | |||
| + | '''The data-gathering bot in combination with the talking bot:''' in this example the data-gathering bot finds the users according to your search terms, and compiles them for you to read over, check for accuracy and remove any false positives. Alongside the data-gathering bot, you can have a talking bot or a team of talking bots which can tweet whatever you want to those users. The campaign Zero Trollerance (https://zerotrollerance.guru) used this method, employing 160 talking bots which enrolled 3000 identified trolls in a self-help program and then sent them humorous motivational messages and video clips over a period of one week. | ||
| + | |||
| + | If you are considering creating bots to work for you to fight online bigotry and harassment, there are some things you need to watch out for. Twitter is not against bots and if you just want to create a bot that scans information from Twitter for you to analyse, or a bot that just tweets out to no one in particular, you will likely not encounter any problems. However if you want to tweet @ other Twitter users, you have to take into account Twitter's policy against spam. | ||
| + | |||
| + | Also keep in mind that language is slippery and if you want to tackle violence against women and trans* persons online, you will have to be very careful about what kind of language you search for. For example, every time someone uses the word “bitch” on Twitter to intimidate or harass a someone, there are probably at least five other people using it to tell their friend how much they love them or talk about the latest celebrity affair. The best way to figure out which language is being used for harm is to crowdsource it from people who have been harassed and then do a number of tests, pulling tweets from Twitter and then analysing the results yourself. | ||
| + | |||
| + | Read more of this section, including how to set up Twitter accounts to be bots for you: | ||
| + | |||
| + | Relevant links: | ||
| + | * Simple bots you can download and test out yourself with a little patience, from Lilith Lela: https://lilithlela.cyberguerrilla.org/?p=9247 | ||
| + | * How to evade Twitter's spam filters with your bot: https://gendersec.tacticaltech.org/wiki/index.php/Step_2#Evading_Twitter.27s_spam_filters | ||
| + | * Twitter's guide to Automation Rules and Best Practices (https://support.twitter.com/articles/76915-automation-rules-and-best-practices). | ||
| + | * Video global Voices "Do We Feed the Trolls?"ː https://www.youtube.com/watch?feature=player_detailpage&v=YRZTeea9ohM | ||
| + | * How the Zero Trollerance bot army worked: http://www.telegraph.co.uk/technology/social-media/11535405/How-do-you-stop-Twitter-trolls-Unleash-a-robot-swarm-to-troll-them-back.html | ||
=== Supporting others === | === Supporting others === | ||
| − | + | It can feel daunting to know what to do when you see someone experiencing online violence, and sometimes in trying to help you can inadvertently worsen the situation. Knowing how to act in the best possible way is our individual and collective responsibility in helping to create a safe space online for everyone. If you are someone who wants to support a disadvantaged group but is not part of that group (men are allies when it comes to women's rights issues), it's important to speak out and say “NO”, in a public space, to online harassment and violence. Otherwise, the culture of impunity to online harassment will continue. Now when your friends or allies are being harassed and/or attacked online, there are some best practices you can follow: | |
| − | + | '''Offer quick support:''' When someone is being attacked or harassed, try to be quick in bringing in support. If you are close to the person under attack, offer immediate assistance. Bear in mind that this person might feel overwhelmed and might not have a clear set of instructions in mind about how to best supported. Remain quiet, attentive and patient and try to not create any extra pressure or stress. In the event of doxing - where confidential info has been released on the internet about that person - you might want to offer a safe space (a home) if the person does not feel safe in their own home. You can also offer to moderate your friend's Twitter feed or blog comments to allow her/them to take a break from it. | |
| − | If you | + | '''Speak out:''' If you do not know the person well, you can at least speak out against what is happening. It's not enough to simply send a private email or a tweet to the person who is under attack telling them that you think this kind of behaviour is unacceptable (sometimes, if the person under attack is being flooded with tweets and mails, it's even better not to write at all). Instead, speak out about it in your networks and raise your voice against such behaviour. You can, for instance, commend publicly the work that the person under attack has been doing. Don't be silent, especially if you are a colleague or a team-mate. Make your voice resonate online - particularly if you are a man! Here is a great exemple of Jay Smooth calling On Men To Challenge Anti-Feminist Internet Trolls (https://vimeo.com/44117178) |
| − | If you | + | '''Organise collectively:''' If you want to have more impact, think about crafting a "collective action" as those are often more effective than individual actions. Gather a group of friends, and friends of friends, for a Twitter storming, for instance. This will show to the person under attack that you and others care and that such acts are not OK. |
| − | + | '''Write a solidarity statement:''' If you are part of an organisation or network, you can write a solidarity statement that explicitly says you condemn online gender-based violence and harassment. Having feminists review the statement of solidarity is a best practice. If it's a person from your organisation who has been under attack, make sure she/they read the solidarity statement before it is released. You can also prepare an organisational policy in advance on what to do if someone is under attack. If you have a policy and specific steps to follow when such a situation occurs, chances are you will do less harm and be more effective in your response. see for instance Tor Solidarity against online harassment (https://blog.torproject.org/blog/solidarity-against-online-harassment). | |
| − | + | '''Talk to the media:''' Depending on the nature and context of the situation, you might want to speak out through the media and highlight the gendered and sexist nature of online attacks. It's always best practice to consult the persons targeted before speaking to the mainstream media. If you do not know the person personally, go through the web of trust - your trusted online network. Thinking about the harm and added stress that the person can go through if they are made visible in the mainstream media is something that you should carefully assess. Consider especially that this is not about you: this is about fighting sexism online and supporting others! | |
| − | + | '''Resources for support:''' | |
| − | + | *'''Block Bot:''' (http://www.theblockbot.com/sign_up) will block known harassers and trolls on Twitter for you. | |
| − | + | *'''Block Together:''' (https://blocktogether.org/) allows you to share your block lists with others on Twitter. | |
| − | + | *'''Foxxydoxing:''' (http://foxydoxxing.com/) scripts to help you analyze the connections between your attackers on Twitter and a wonderful graphic story to explain how it works. | |
| − | ''' | + | *'''Crash override network: ''' (http://www.crashoverridenetwork.com/) a support network and assistance group for victims and targets of unique forms of online harassment, composed entirely of experienced survivors. They work preventatively and reactively with survivors during episodes of harassment to keep them safe and provide them with the means to reduce harm and rebuild, as well as disempower their harassers. |
| − | + | *'''The Online Abuse Prevention Initiative (OAPI): ''' is a nonprofit organization dedicated to reducing and mitigating online abuse through the study and analysis of abuse patterns, the creation of anti-harassment tools and resources and collaboration with key tech companies seeking to better support their communities. It works in collaboration with the Crash Overide network (http://onlineabuseprevention.org/) | |
| − | + | *'''Zero Trollerance:''' (https://zerotrollerance.guru) a humorous, video-based self-help program for sexist Twitter trolls. You can send your Twitter trolls links to individual videos or to the main website zerotrollerance.guru. You can also contact @ztrollerance on Twitter to do it for you. | |
| − | + | *'''HeartMobː''' is a platform for real-time support to individuals experiencing online harassment and empowers bystanders to act. Visit their Kickstarter project to know more about the initiative (https://www.kickstarter.com/projects/4096561/heartmob). | |
| − | + | *'''Trollbusters:''' (http://www.troll-busters.com/) still in development, this tool plans to counteract Twitter abuse by flooding your timelines with love messages. | |
| + | |||
| + | === Documenting violence === | ||
| + | |||
| + | Besides directly supporting and showing solidarity with people subjected to violence, you can also populate and contribute to the documentation of instances of online violence and harassment. Those initiatives are key in order to show the extent of the problem and to make visible some of the structural aspects of violence in societies. | ||
| + | |||
| + | '''Resources for documentation:''' | ||
| + | |||
| + | * APC's '''Take back the Tech:''' has collected more than 500 stories of women who have experienced violence online. These stories were gathered using the open source platform called Ushahidi. The data visualisation can be see here: https://www.takebackthetech.net/mapit/ . The overall results of those who have participated in this exercise show that women between 18 and 30 who are using Facebook are most likely to be under online threat (http://www.genderit.org/articles/mapping-strategy-disclose-online-violence-against-women). | ||
| + | |||
| + | * '''GenderIT.org:''' emerged from APC's Women’s Rights Programme’s advocacy work in information and communications technologies. The need to have examples of national policy, gender-sensitive language, tools for lobbying, and an understanding of the impact of poor or positive policy all within easy access has been expressed by ICT advocates and policy makers alike (http://www.genderit.org/). | ||
| + | |||
| + | * '''The Geek Feminism Wiki''' has been documenting sexist incidents in geek communities. To see the timeline of incidents: (http://geekfeminism.wikia.com/index.php?title=Timeline_of_incidents). You can also check out their resource pages for allies supporting support women in geek communitiesː (http://geekfeminism.wikia.com/wiki/Resources_for_men) | ||
| + | |||
| + | * '''Women, Action, and the Media (WAM!)''' has written a report on online violence on Twitter (https://womenactionmedia.org/cms/assets/uploads/2015/05/wam-twitter-abuse-report.pdf/) and created a Twitter Harassment Reporting Tool (https://womenactionmedia.wufoo.com/forms/wam-twitter-harassment-reporting-tool/). | ||
| + | |||
| + | * '''Breaking the circle''' is an international campaign to raise awareness on the fact that gender violence is a problem that concerns both men and women, which focus on the role of men and include them as agents of change. They have developed a series of tools and information that will help us spread the message and raise awareness (http://en.breakingthecircle.org/). | ||
| + | |||
| + | * '''Crowdmaps in Indiaː''' After the Delhi Gang Rape there was a lot of interest in how tech could be used to address the issue of sexual violence against women in offline spaces. These initiatives emerged from spaces where tech meets gender in order to see how tech can be used to tackle gender based violence gender problems. See for instance Harassmap in Bombay (www.akshara.crowdmap.com ) and the Safecity -Pin the creep (www.safecity.in) and the 'Safetipin' app for safely auditing public spaces. | ||
| + | |||
| + | * '''Macholandː''' This french platform wants to voice actions, embedded in the public, media and political speech, driven by citizens who refuse to see sexism spread massively without reacting. Each user can participate and propose an action that pin with humor brands, organizations and public figures (http://macholand.fr/) | ||
| + | |||
| + | * '''Feminist Frequencyː''' This project includes the video series Tropes vs. Women, created by Anita Sarkeesian with Bitch magazine to examine common tropes in depictions of women in film, television and video games, with a particular focus on science fiction. Videos produced in this series include “The Manic Pixie Dream Girl”, “Women in Refrigerators” and “The Smurfette Principle” (http://feministfrequency.com/) | ||
== Safe spaces offline == | == Safe spaces offline == | ||
| − | + | Many of the principles of creating and maintaining safe spaces online can also be applied offline. As noted in the introduction of this chapter, safe spaces can either be temporary and take place during a one time event or training or can also become permanent spaces where collectives or organisations embed the basic principles of safety, support, respect and inclusiveness in their own space management. | |
| − | + | In the case of security and privacy training, you also need to consider how participants can best learn skills to protect themselves when the topics themselves can be frightening or overwhelming. The environment also has to be suited to the participants share stories about threats they have been facing online and offline. Those stories can be very traumatic and personal and should be handled carefully, but at the same time they are a very important part of the process of developing security and privacy strategies. | |
| − | + | The difficulties in defining what a "safe space" should look like are inherent in the fact that you are bringing a diversity of people together, who might be considered to be part of the same community but who all have different histories, contexts and needs. What one person might find politically, socially or personally threatening might mean very little to another. And everyone will of course also come with different experiences and levels of knowledge and skills with regard to technology. | |
| − | + | It is important to be aware that, in struggling to perfect a safe space, one always runs the risk of creating instead yet another form of social control and pressure to conform to a particular image of what, for example, a woman or trans* person is or should be. | |
| − | + | === Boundaries === | |
| − | * | + | When trying to create a safe space, you might encounter the issue of who is included and who is excluded from it. It can very divisive, as it will often touch on people's strongly held sense of their political, personal, sexual and social identities. Issues of sexual orientation and gender identity will likely come up. Some will prefer a women and trans* only environment, some will feel that this opens up an opportunity for external attacks on the whole project by adversarial forces, while some will feel that cis-men friends and colleagues are being unfairly excluded, and feel resentful. If you are having a debate about this, some things to consider are: |
| − | * Who do we want to include, influence or support? Specifically women and trans* or also potential | + | |
| − | + | * Is there an agreed framework and rules of engagement? How do we define "woman" and "trans*"? How do we define "safe"? | |
| + | * Who do we want to include, influence or support? Specifically women and trans* persons, or also potential allies? | ||
* How important versus how contentious? Is it worth alienating some people from the group? How can we frame the debate to avoid alienating people who don't agree with the decision? | * How important versus how contentious? Is it worth alienating some people from the group? How can we frame the debate to avoid alienating people who don't agree with the decision? | ||
* How will the decision affect the actual experience of people within the space? | * How will the decision affect the actual experience of people within the space? | ||
| − | * Do we have all the skills we need to deliver this project among our networks or will we need specific additional skills? Where will we get them? | + | * Do we have all the skills we need to deliver this project among our networks, or will we need specific additional skills? Where will we get them? |
| − | * How will the space be | + | * How will the space be organised to promote equal participation, especially if cis-men are included? |
| − | It's important to remember that building offline spaces is resource- and labour-intensive and often many compromises have to be made. It may be a good idea to try to identify as early as possible which values are shared, important, and relevant to the event so that you can constantly remember to prioritise those and de-prioritise less important or potentially divisive issues. | + | It's important to remember that building offline spaces is resource- and labour-intensive, and often many compromises have to be made. It may be a good idea to try to identify as early as possible which values are shared, important, and relevant to the event, so that you can constantly remember to prioritise those and de-prioritise less important or potentially divisive issues. |
| − | Building offline spaces is easiest and most successful when you're clear about what you're trying to do and how you plan to go about it. The second thing which must be considered is exactly what the event is intended to achieve. | + | Building offline spaces is easiest and most successful when you're clear about what you're trying to do and how you plan to go about it. The second thing which must be considered is exactly what the event is intended to achieve. For example: |
| − | * Skills: How can we learn to do xyz? | + | * '''Skills:''' How can we learn to do xyz? |
| − | * Advocacy: How do we change the culture of tech sectors to be more amenable for women and trans* persons, and/or let the world know that they are great at tech? | + | * '''Advocacy:''' How do we change the culture of tech sectors to be more amenable for women and trans* persons, and/or let the world know that they are great at tech? |
| − | * Support, networking and boundary-crossing: What does it mean to be a woman or trans* person in tech? How can women from different places or sectors come together to spark off new ideas and practices? How can we support each other as women and trans* persons in tech? | + | * '''Support, networking and boundary-crossing:''' What does it mean to be a woman or trans* person in tech? How can women from different places or sectors come together to spark off new ideas and practices? How can we support each other as women and trans* persons in tech? |
| − | + | Different aims will inform different safe space policies. For instance, it's difficult advocating for change in the male-dominated tech sector if you haven't invited cis-men to hear what you want to say - but you might prefer to discuss *how* to do this in a women and trans*-only environment first. If, on the other hand, you are advocating for engagement with technology to women and trans* persons and mainly want free, honest and mutually supportive discussions or skills-sharing, then in this case, a women and trans* only environment suggests itself. | |
| − | With skills workshops, there is research to suggest that women and trans* persons learn tech skills best with each other so these workshops have a very clear and communicable reason for being exclusive. Another possibility | + | With skills workshops, there is research to suggest that women and trans* persons learn tech skills best with each other, so these workshops have a very clear and communicable reason for being exclusive. Another possibility is to run an event twice, once for women and trans* participants and once for open participation. This can have the positive side-effect of enabling others to experience a safe space methodology and thereby change their own practices in the spaces they organise, but it will be clearly more time consuming. |
=== Choosing a format that fits === | === Choosing a format that fits === | ||
| − | Once you have settled the basic questions | + | Once you have settled the basic questions on what your event is for and who you want to invite, it's time to think about the format of your event. Deciding which format to use can be helped by your answers to some key questions: |
| − | * What are you trying to do | + | * What are you trying to do? Which format will support this activity best? |
| − | * What are participants' needs, existing skills, experience and preferences | + | * What are the participants' needs, existing skills, experience and preferences? |
| − | * What physical spaces are available, what will they allow you to do, what resources do you have? | + | * What physical spaces are available, what will they allow you to do, and what resources do you have? |
* What are your human and organisational resources - how much can you take on? | * What are your human and organisational resources - how much can you take on? | ||
| − | There are many different ways of organising | + | There are many different ways of organising events. Some of the most popular in FLOSS and tech-related communities are: |
| − | * Un-Conference: | + | * '''Un-Conference''': helps people to make connections, share knowledge, collaborate and inspire each other. To take part, participants are encouraged to give a presentation, create a discussion, or even chair a debate (http://lanyrd.com/blog/2012/unconference-howto/ ; http://openspaceworld.org/wp2/what-is/). This format can be relatively egalitarian and relatively easy to organise (no messing about with programmes, scheduling and advanced prep) but you should watch out for the tyranny of structurelessness. Thy can also be extremely intimidating and therefore exclusionary towards less experienced or skilled participants; and can be stressful if you need to organise tech or other resources for specific activities in advance. |
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | ||
| − | + | * '''Workshop''': transferring skills or knowledge in an interactive session. There are many possible workshop methodologies. Selecting a workshop format is very much about being clear about what you want to achieve. Workshops can be a good format for building skills or for maker and design activities. For instance in Pakistan Hamara Internet is a campaign by Digital Rights Foundation that seeks to raise awareness about violence against women online through various workshops. It literally means ‘Our Internet’ in English and works to impart digital security tips and training to women and bridge the gender digital divide in Pakistan (http://hamarainternet.org/). | |
| − | + | * '''Hackathon:''' With its general motto "programming till someone drops from exhaustion", hack events can mix different groups - like NGOs with hackers - to come up with new approaches to building technology for that group. For instance IGNITE (Women Fueling Science and Technology from the Global Fund for Women International) organised a global Hackathon called #hackgirlsrights. This 24-hour, multi-country coding event, targeted girl coders which collaborate to develop a website or application that address specific challenge facing girls and young women (http://ignite.globalfundforwomen.org/gallery/ignite-international-girls-hackathon). On the past 23th of April 2015, another global feminist hackaton called femhack was organised around the world in loving memory of Woman Human Rights Defender Sabeen Mahmud (https://f3mhack.org). You can read more about how to run a hackathon here: (http://globalvoicesonline.org/2012/11/23/hackathons-in-droves-how-is-a-hackathon-organised/) | |
| + | |||
| + | * '''Sprint:''' A sprint is a gathering of people involved in a specific project to further the focused development of some aspect of the project, such as working on sections of code, writing manuals or books, etc. These are effective at getting a lot done quickly for code and manuals (less so for other forms of writing), but can be exhausting and emotionally demanding - make sure you keep food and drink coming! To read more about sprints, visit wikipedia: (https://en.wikipedia.org/wiki/Sprint_(software_development) and Flossmanuals: (http://www.flossmanuals.org/service/booksprints). To note for instance that this manual was edited during an editorial sprintǃ | ||
| + | |||
| + | * '''Seminar:''' A seminar brings together a small group for recurring meetings which focus on a particular subject. In a seminar, everyone actively participates, or offers information or training on specific topics. On the one hand, this kind of structured activity supports people with less experience or confidence; planning for tech/resource support is fairly straightforward; and people know what to expect. On the other hand, the event can be experienced as overly structured and lacking spontaneity for more experienced participants; more 'top-down'; and requires more organisational effort in advance. Check out for instance The documentation of the Feminist Server Summit which consisted in a feminist review of mesh- cloud- autonomous- and D.I.Y. servers (http://vj14.constantvzw.org/r/about). | ||
| + | |||
| + | More stable kinds of safe spaces for experimenting and learning technology include: | ||
| + | |||
| + | * '''Hacklab, hackerspace or makerspaceː''' These are community spaces with hardware and/or tools - great for people to "get their hands dirty" and play around with anything - from taking computers apart to installing Linux to making music with bananas or building a radio out of razorblades and wire. Read more about hacklabs and hackerspaces here: "Hacklabs and Hackerspaces: Shared Machine Workshops":(http://www.coredem.info/IMG/pdf/pass11_an-2.pdf). You can also visit the following portalsː (http://makerspace.com/) (http://hackerspaces.org/) | ||
| + | |||
| + | * '''Feminist hackerspace:''' Those vary in shape, form, and size. What often unites them is a set of boundaries that are decided on collectively (who can be a member, who can be a guest, what are the policies, etc.) and an explicit belief in feminist principles. Feminist hackerspaces provide a place to work on individual and collective projects in a supportive environment. To know more about feminist hackerspaces you might want to visit the website Mz Baltazar’s Laboratory in Vienna (http://www.mzbaltazarslaboratory.org/), The Mothership Hackermoms in Berkeley (http://mothership.hackermoms.org/), Double Union in San Francisco (https://www.doubleunion.org/) and FemHack in Montreal (http://foufem.wiki.orangeseeds.org/). | ||
| + | |||
| + | For sharing skills, setting up a feminist hackerspace, or choosing an unconference, workshop or seminar format makes a lot of sense. For advocacy and networking events, the choice is not so obvious. Advocacy events can be some of the most challenging as it's easy to spend the entire day "re-inventing the wheel" with people who are new to the questions. If you have participants from diverse backgrounds in your advocacy event, it could be best to go with a more structured format. Unconferences and hackathons work best with activists or experienced practitioners who are used to a high level of self-determination, and who have a shared understanding of the implicit rules and structures of the space. Having said that, it can work well to try more open formats anyway, but be prepared for some skilled facilitating to make it a safe and fun space for both experienced and less experienced participants. Sometimes a mixed approach is what's needed - and some experimentation! | ||
| + | |||
| + | === Fixing gender gap in tech === | ||
| + | |||
| + | In order to get some inspiration we list below a selection of initiatives specially oriented at getting more women in ICT and technological related fields. | ||
| + | |||
| + | * '''Asikana Network (Zambia)ː''' is a group of females aiming to empower women in ICT related fields by changing mindsets and eliminating negative stereotypes attached to girls and women in ICT (http://asikananetwork.org/). | ||
| + | * '''Akirachix (Kenya)ː''' is an african wide network of women in technology to make tech and to inspire and mentor other women to be technologists (akirachix.com). | ||
| + | * '''Donestech (Spain)ː''' is a cyberfeminist and activist research group which develops also workshops and audiovisual productions in relation to gender and ICT access, uses of and desires. Lelacoders project is about studying and making visible the presence of women in the development of computer sciences, free software and hacker cultures (www.donestech.net) (https://n-1.cc/g/donestech+lelacoders). | ||
| + | * '''Feminist Approach to Technology (India)ː''' mission is to empower women by enhancing women’s awareness, interest and participation in technology (http://fat-net.org/). | ||
| + | * '''Flossie (UK)ː''' runs a conference and also skills workshops and it is intended to combine advocacy, boundary-crossing, support and skills-sharing bringing together women involved in digital arts with coders, artists, and makers (http://www.flossie.org/). | ||
| + | * '''Speakerinnenn (Germany)ː''' aim is to increase the visibility of women in the field of public speaking. With the help of our list it will be easier for organisers to find female experts to speak at their events (http://speakerinnen.org/). | ||
| + | * '''The Ada initiative (Global)ː''' organises AdaCamp, a series of conferences dedicated to increasing women’s participation in open technology and culture: open source software, Wikipedia and other wiki-related projects, open knowledge and education, open government and open data, open hardware and appropriate technology (https://adacamp.org/). | ||
=== Codes of conduct === | === Codes of conduct === | ||
| − | It's important, especially in mixed environments, to think about what's acceptable | + | It's important, especially in mixed environments, to think about what's acceptable conduct in the space and what isn't. In order for this to have any practical effect, it's also important to think about what you'll do if individuals breach this - or when things go wrong generally. You can find plenty of information and example policies on the Geek Feminism Conference anti-harassment/Adoption page (http://geekfeminism.wikia.com/wiki/Conference_anti-harassment/Adoption) |
| − | Make sure your participants understand | + | Make sure your participants understand the policy and how it relates to their own conduct. It can be useful to make time in your schedule at the beginning of the event to share your policy, and reach consensus with the group on how to maintain a safe space over the days of the event. |
| − | Your | + | Your code of conduct should be about preventing aggressive behaviour and not about trying to police how people identify, communicate or present themselves. It's also worth remembering that people who are struggling in a culturally unfamiliar environment can become confrontational more easily than they usually would. There may be many reasons why a participant might be struggling to communicate positively at any given moment. It's key to remain calm and to provide a non-judgmental space for the expression of emotions like anger or frustration. Because of this, a code of conduct should also include some people that will be assigned to receive feedback if any problem takes place. They should be good facilitators or moderators and be calm and patient. We are different, let's celebrate it, even when it's difficult to do! |
| − | Last not least, your code of conduct should include an agreement about how participants will respect | + | Last not least, your code of conduct should include an agreement about how participants will respect other participants' '''right to privacy'''. Some general guidelines could include the following: |
| − | * Don't take or circulate sound, video or photos without permission | + | * '''Don't take or circulate sound, video or photos without permission'''. If anyone present faces significant external risk then don't take photos at all unless participants have given express permission and an opportunity to cover their identity. |
| − | * If you wish to record the event, prepare formal consent forms telling people exactly what audio-visual records are being made and how they will be stored | + | * If you wish to record the event, '''prepare formal consent forms''' telling people exactly what audio-visual records are being made and how they will be stored, used, licensed and ask for clear consent with a signature. |
| − | * Don't share details of anyone's participation, speech or actions on social media without their express permission. | + | * '''Don't share details of anyone's participation''', speech or actions on social media without their express permission. |
| − | === | + | === How safe is the space? === |
| − | As a | + | As a check-list, here are some questions that can help you assess whether a space is safe or not. |
| − | * What is the history of the space? | + | * '''Background:''' What is the history of the space? Who started it and why? How many women and trans* persons have been involved? |
| − | *Who has | + | * '''Participation:''' Who has stopped participating in the space since it was founded, and why? Is it mostly women who have left? |
| − | * Does the space | + | * '''Policies:''' Does the space have policies? If so, what kind? Are the policies regularly put in practice? Ask members in the space, particularly women. |
| − | + | * '''New people:''' How does the space welcome newcomers? The first time you went to the space, did you get a tour? Did people say hello? Were the people in the space friendly? | |
| − | * How | + | * '''Regular assemblies:''' Are there regular meetings (assemblies) that offer possibilities to raise concerns, to suggest collective projects, to suggest the organisation of workshops, to discuss the space (its cleanliness, etc.), to present yourself, etc.? |
| − | * Are there regular meetings (assemblies) that | + | * '''Language:''' Is the language and vocabulary used on the website and in the space explicitly feminist? Read the website carefully, or go and see for yourself what the space looks like. |
| − | * Is the language and vocabulary used on the website and in the space explicitly feminist? Read the website carefully, or go and see for yourself | + | * '''Trust:''' Do you know people who you trust in the space or do you know friends of friends? The web of trust can be very useful here. |
| − | * | + | * '''Access:''' Who can go into the space and under which conditions? This should be made explicit on the website, otherwise ask. |
| − | + | * '''Accessibility:''' Is the space itself easily accessible? In which part of town is it located? Are there bathrooms? What are the opening hours? Who has access to the keys of the space? | |
| − | * Is | + | * '''Cost:''' How much does it cost to become a member? Is there a sliding scale policy? |
| − | * How much does it cost to become a member? Is there a sliding scale policy? | + | |
| − | No space is | + | No space is perfect; a safe space should always, however, at least provide an environment and a set of boundaries in which to meet up, talk, and address and raise difficult issues. If you feel the space has potential and you want to get involved, don't be shy! |
| − | + | '''Relevant links:''' | |
| + | |||
| + | '''* Integrated Security Manual:''' (http://www.integratedsecuritymanual.org/) a resource for planning, convening, and hosting your workshop which prioritize your participants' emotional and physical well-being. | ||
| + | |||
| + | '''* Level Up:''' (https://www.level-up.cc/resources-for-trainers) resources for digital security trainers and organisers of these trainings too. | ||
Latest revision as of 08:32, 4 June 2015
Contents
Chapter 2: Safe spaces
Safe spaces can be understood as spaces that are created though explicit community agreement, or through implicit sharing of values. They enable members of a group to flourish, empower themselves and create community. Safe environments for discussion and awareness-raising have played a key role in many women's liberation movements.
As explained by integrated security trainer, Sandra Ljubinkovic, safe spaces are important for any integrated approach to security because they enable an environment that support people to express their emotions without fearing any judgment: “Creating a safe space is crucial for creating a sense of physical safety as well as a sense of confidence in a group. It is important for participants who usually have no time to relax to feel comfortable and enjoy simple things. And if they live in a country where their lives are in danger it is even more crucial to make sure that they feel physically safe. Safe space in a group means a space to feel comfortable and speak openly and freely about feelings, challenges, and emotions as they may arise. In the workshops where issues personally affect people (whether those are physical, emotional, or spiritual threats and challenges), participants may have strong emotions as they do their own inner work facing their own oppression, privilege, anger, hurt, pain and suffering”.
Safe spaces can be temporary and take place during a one time event or training, they can also become permanent spaces when collectives or organisations embed the basic principles of safeness, support, respect and inclusiveness in their own space management.
Whatever format or style is used, a safe space should allow allow women and trans* persons to access and learn about technology and related fields without having to fear sexist language and attitudes, being challenged, mocked or mansplained. There are many possible event formats and styles which can support the creation of safe spaces, both online and offline, to allow women, trans* and other groups to communicate and exchange in a nurturing and welcoming environment.
You might assume that the online communities you create or take part in through social media, discussion lists and chat channels are inherently democratic, non-hierarchical, participatory and relatively safe. However online spaces often reproduce the same hierarchies, privileges and power relations that exist in society, in the offline world.
It's important to be mindful of this and to think through ways to mitigate and limit these downsides in order to get the best out of our spaces. Using such strategies is about caring for ourselves and for the communities we are part of. Making these issues explicit and visible is also about agency, social justice and feminism, helping us to better shape the spaces we care about, we organise in and within which we grow.
This section, will first look at building safe spaces online for enabling a better and safer collaboration among us through the use of mailing lists, chat, and other collaborative tools such as forums, wikis and pads. It will also look at how to use these tools tactically, in a way that supports the creation and maintenance of safe space. The tools that have been highlighted in this section have been included because they are free and open source, and are designed and administered with increased privacy and security in mind, minimising the amount of traces we leave online.
Second, the section will focus on strategies of resistance in public spaces which are not inherently safe - for instance Twitter and Wikipedia. Those examples are designed to give us insight into how we can create safety online collectively by developing feminist counterspeech, storming and swarming together in order to protect and support each other.
Finally it will loop back to the offline world and discuss ways to build safe spaces offline in the physical world, such as through women and trans* only or mixed spaces, to learn and Do-it-Together.
Collaboration
Mailing lists
Mailing lists are one of the oldest forms of social networks, allowing a group to discuss and organise, to exchange information, video, audio and images. A mailing list is a list of addresses to which the same information is sent simultaneously. The most common types of mailing lists are announcement lists and discussion lists.
If you have decided within your group that you need a secure communication channel and that you do not want to use corporate services, there are some good alternative services to choose from, often recommended for human rights defenders. Riseup, Aktivix and Autistici/Inventati (A/I Collective) are all free services that prioritise security and user privacy. Riseup in particular has many feminist- and queer-oriented lists and is therefore a great place to host your mailing list. On their website you can also have a look at the lists that already exist.
Riseup lists: https://lists.riseup.net/www/
Aktivix lists: https://lists.aktivix.org/mailman/listinfo
Autistici lists: http://www.autistici.org/en/services/lists.html
If you or your organisation has your own server you can also install your own software for managing mailing list and ensure that all your communications remains hosted and safe in your own machine and can not be intercepted by unintended third parties. More information at: https://en.wikipedia.org/wiki/Category:Free_mailing_list_software
Open or closed?
Once you are ready to create your mailing list you need to decide whether it will be open or closed.
Open: An open list allows anyone to subscribe, and then once they have joined the list, to receive announcements or participate in the discussion. Subscription can either be automatic, or it can be approved by a moderator. This type of mailing list is good for reaching out to your potential allies, contributors and followers and keeping them update about your activities.
Closed: Another option is to keep your mailing list closed. In a closed list, membership is limited, and all subscribers require approval before they can join the list. It's possible to have a list that is publicised - ie that everyone knows about - but still closed. This type of list is useful when you want to discuss sensitive or personal topics and be sure that all members in the conversation are trustworthy.
Note that sometimes the archives of a list can be made public to anyone on the web, and will also therefore end up on search engines (like Google). Check if keeping a list open to new subscriptions automatically implies that the archives of the list will be made publicly available, or if they will only be accessible to those who have the subscription password. Sometimes you can choose whether you keep the archives public or not.
If you intend to talk about sensitive issues (and talking about gender related topics is often a sensitive issue!) or if trust within the group is important for creating your safe space, you might want to set up a closed list and to keep your archives closed. If you do choose to leave your archives accessible, it is important to inform everyone subscribed to the list that any delicate topic or personal detail that pops up in your discussions will be potentially visible to anybody.
Encrypted lists: If you want a high level of security, there is also the possibility of encrypting mailing lists. However, it is important to understand that this requires every participants to the list to already use encryption software like PGP or GPG. This type of list, based on software called Schleuder (http://schleuder2.nadir.org/) and developed by Nadir.org, is designed to serve as a tool for group communication, but this time with a strong emphasis on security.
Policies
Agreeing on a mailing list policy - a set of do's and don'ts for the list - from the start will save you a lot of time and possibly difficult conversations. Even on a closed list, publishing your policy - which should include the ways in which moderation takes place and how to report violations of the policy, - can be helpful in creating the online safe space you want everyone to feel comfortable in. Your policy can address tensions like the fact that being free to expressing emotion is an important feminist principle, but losing your temper and attacking someone you don't agree with on the list is not ok. In the end any good mailing list policy will set its own rules for achieving a correct balance between freedom of expression and opinion and impeding flames and racist, sexist, or homophobic attacks for instance to take place within the list.
Having a visible and explicit policy sends a strong message about the value of maintaining the mailing list as a safe space. It can also help you to decide who can be added to your list and who not. To make sure that the policy does not get forgotten, you can regularly remind subscribers about it, with a link at the end of each mail you send out.
Relevant links:
- Sample mailing list policies that can be adapted and used for your own purposes: for women-only communities (http://geekfeminism.wikia.com/wiki/Statement_of_purpose/Women-only_communities) and for communities including men (http://geekfeminism.wikia.com/wiki/Statement_of_purpose/Communities_including_men).
Administration
Administrating a list: involves handling subscriptions and moderating content. You can choose how many administrators you want your list to have. Be aware that if your list suddenly becomes very chatty, this might be too demanding for just one person. Besides that, any communication tool including many members should not rely on only one person for administration duties. Take into account that this person could have problems, disapear or simply become abusive because of their power. Because of this, you should include more people helping with administration and moderation duties. A list can also be collectively managed and you can distribute those responsibilities among members of the list.
Moderating a list: as a general rule, moderation has three main goals. First, a well-moderated community will be more productive and efficient in generating and distributing valuable information and knowledge to its members (subscribers). Second, good moderation will increase the accessibility and openness of online communities by enabling respectful dialogue among its members. Finally, it will lessen the demands on the infrastructure, as well as on the list members.
Remember that any online safe space will apply the basic principles of net etiquette and that any good administrator, moderator and mailing list policy should review, adapt and include those principles in their core social norms and values and ask members of the list to discuss, understand and accept those. In a nutshell net etiquette requires users to: be nice, learn internet acronyms, keep messages brief, do not shout, protect personal information, help others, and to not send mails if feeling angry! (For more information see: http://www.networketiquette.net/ and https://en.wikipedia.org/wiki/Etiquette_in_technology)
Mailing list examples
Before setting up your own mailing lists, you might want to engage with some of the established mailing lists focused on gender and technology. for example:
Open Mailing lists:
Take Back the Tech!: the mailing list associated with the collaborative campaign to reclaim information and communication technologies (ICT) to end violence against women (VAW). To register: https://lists.takebackthetech.net/mailman/listinfo/takebackthetech
FemTechNet: is a network of scholars, students, and artists who work on, with, and at the borders of technology, science, and feminism in a variety of fields including Science and Technology Studies (STS), Media and Visual Studies, Art, Women’s, Queer, and Ethnic Studies. To register: http://femtechnet.newschool.edu/mailman/listinfo/femtechnet
Queer Feminism Geek: is a network of feminist, queer and trans* hackers, makers, geeks and artists who organise activities and assemblies at the Computer Chaos Camp and Congress. To register: https://lists.riseup.net/www/subscribe/queerfeministgeeks
Subscription after endorsement by others on the list:
Fembot: is a network of scholars and students who focus on gender, media & technology. To register: https://lists.uoregon.edu/mailman/listinfo/fembot
Femmehack: is a list created to organise a Global Feminist Hackathon that took place past 23th of May 2015 in loving memory of Sabeen Mahmud, a Woman Human Right Defender shot to death in Pakistan: https://f3mhack.org
TransHackFeminist: is a list that was created after the first THF convergence in 2014 where intersectional feminists, queer and trans* people of all genders met to better understand, use and ultimately develop free and liberating technologies for social dissent. It gathers members from all the over the world and uses Spanish and English to communicate: http://transhackfeminist.noblogs.org/files/2015/01/THF_report_Eng.pdf
Closed mailing lists:
Gender and Technology Institute Participants: The GTI list is a closed list of people who participated in the Gender and Technology Institute that took place past December 2014, inasmuch as it is opened to people trained by Tactical Technology Collective to privacy and digital security from a gender perspective.
Ada camp: is a closed list that is dedicated to speaking about issues related to women in open source. It is composed of the people who participated in Ada Camp: https://adacamp.org/
Chat with IRC
Internet Relay Chat (IRC) is a chat service which can be hosted on different servers and accessed through different user clients. It provides the ability to set up channels or chatrooms which allow many people to contribute to a discussion in real time. IRC also gives you the option to encrypt your communication. You can’t embed video, audio or pictures, but you can link to them.
While IRC can be a great tool for facilitating collaboration, there are things to bear in mind if you decide to use it. First, IRC can take a little time to get used to, depending on the skills in your group. Second, developing relationships across a purely text-based channel such as IRC can be challenging. Writing is not easy for everyone; and some in the group might not be using their mother tongue.
Accessing IRC through your browser: There are several ways to chat through an IRC network. The easiest way to start out is to access an IRC network directly through your browser, such as one from Indymedia (https://irc.indymedia.nl/) or Freenode (https://webchat.freenode.net/). You can get set up immediately by creating a nickname and a channel, which you can then give to your colleagues to connect with you.
Accessing IRC through a chat client: Connecting to an IRC network through your browser is, however, not the most secure option out there. If you are a more advanced user, or if you have already tested out IRC out and think it will work for your group, it can be better to access your chosen IRC network from a chat client.
There are a few different chat clients which you can choose from, including Jitsi and Pidgin. You can read more about these clients and how to use them on Tactical Tech's Security in-a-Box: Jitsi (https://securityinabox.org/en/guide/jitsi/windows) ; Pidgin (https://securityinabox.org/en/guide/pidgin/windows).
How to use a network: Advice and instructions on using an IRC network can be found on Freenode (https://freenode.net/using_the_network.shtml), Autistici (https://www.autistici.org/en/stuff/man_irc), and Indymedia (http://docs.indymedia.org/view/Sysadmin/IrcHowTo). The last two also allow us to anonymise our connections through Tor.
Facilitating a meeting: Once you start an IRC meeting, it is useful to appoint a facilitator to keep track of time. This person might also be in charge of making sure the discussion sticks to the topics at hand. In order to create a welcoming environment and a safe space, acknowledging and valuing the voice of everyone is key on IRC. When you start a conversation, take time to greet people - in particular newcomers. When facilitating a conversation:
- Set a time limit and stick to it because IRC meetings can be very tiring.
- You might decide that people should be given turns to speak in order to ensure that everyone has space to express themselves. You can simply assign turns in alphabetical order of nicknames (or any order you want to give) for each of the points addressed. This can help structure the conversation and stop one person or a small group of people dominating the conversation.
- IRC can go very fast, particularly if there are many people involved in the discussion. Getting everyone to slow down and read all the inputs can decrease frustration.
- It can be useful to end your input with “over” or "done", so everyone knows when you have stopped speaking.
Whatever the facilitation methods you choose, communicate them explicitly to all the participants beforehand, for example in the email where you invite people to join the meeting.
Forums, Wikis and Etherpads
Chat services and mailing lists can be extremely useful, but they will only take you so far. When it comes to managing collaboration between people living in different places, you will probably find yourself looking for something with more functionality.
Internet forums: One of the oldest tools used for public discussions online are internet forums, where discussions can be hosted over time and are at least temporarily archived. What really distinguishes a forum from a mailing list or IRC chat is that it has a tree-like structure and can contain a number of sub discussions, each with a different topic.
Wikis: If you are looking for a tool to collaboratively write a text with many sections, or even to create the initial structure and content for a website, a wiki can be a useful tool. A wiki is a web application that allows for hierarchical structuring of content and tracks the edits and additions of the users, easily allowing you to revert changes, and move and delete content.
Both forums and wikis need to be hosted on a server, so you'll need to know how to set one up and manage it.
Etherpads: For collaborating in real-time on documents, Etherpads are a great resource. They are also a good alternative to corporate services like Google Docs, and are far more effective for co-editing text than, for example, sending mails back and forth. The main thing you need to check for in an etherpad is that it is hosted with an encrypted connection (via SSL). A list of such etherpads can be found here: https://github.com/ether/etherpad-lite/wiki/Sites-that-run-Etherpad-Lite.
- To create a new etherpad (ie, a new document that you are going to collaborate on), you need to decide on the name of the URL. Because each pad is open to anyone who has the URL, you should give each pad a long and inventive name, so that it can't be easily guessed. For example: https://pad.riseup.net/p/feminists is not secure. A more complicated URL such as https://pad.riseup.net/p/FeministsRockAndTheyWillBeDoingGreatThingsToghether is much more secure. Once the etherpad has been created you can send the URL to your friends and colleagues to start collaborating on a document.
- If you are worried about your etherpad being found by others, you can also consider a password-protected pad. For more on this, see: https://www.protectedtext.com/
- Etherpads allow you be anonymous, use a pseudonym or use your real name. There is a colour-based system that differentiates the contributions of each participants on the Etherpad, so you can always see who is contributing what.
Safe spaces in the public sphere
There are many spaces which will feel inherently unsafe either because they explicitly or implicitly exclude women and trans* people, or because they harbour bigots. There are a number of ways to counter the vulnerability and intimidation we might feel online. One is through caring for our personal and collective safety, through using security -and privacy- enabling tools and techniques and managing safely our online identities. Another is shaping with others methods to reclaim and stay safe in the public sphere. Organising collective actions can be a powerful act of resistance, bringing attention and visibility to the situation and in turn helping to bring about transformation.
Feminist counterspeech - creating counter-narratives online, or "talking back" - is one strategy for making sexism visible and for responding to online attacks and harassment. It can be an effective tactic to create a sense of belonging and make visible the effectiveness of collective feminist actions online. There are many examples of feminist counterspeech in action - many of which you have probably seen and appreciated. The Everyday Sexism Project (https://twitter.com/everydaysexism), for example, catalogues instances of sexism experienced by women on a day-to-day basis; or Byefelipe (https://instagram.com/byefelipe/), the Instagram account which reposts abuse my men who turn hostile when rejected. Feminist counterspeech can also include tactics to enable the inclusion and visibility of women's contributions to knowledge platforms such as Wikipedia.
Storming Wikipedia
There have been many studies that have criticised the way in which knowledge is produced on Wikipedia. A 2010 survey (https://web.archive.org/web/20100414165445/http://wikipediasurvey.org/docs/Wikipedia_Overview_15March2010-FINAL.pdf) conducted by the United Nations University found that only 13% of Wikipedia contributors identified as female. The fact that Wikipedia’s contributors are mostly men in their twenties and thirties, and disproportionately western, are important factors that influence content.
Women who have played a significant role in history are also often missing from Wikipedia, and feminist, queer and trans* content is often challenged.
The lack of gender and cultural diversity in the content on Wikipedia demands creative responses. Because of this partnerships, research, community organizing, socio-cultural and technical interventions should all be considered.
Storming Wikipedia or organising Edit-a-thons are two possible interventions. These enable participants to learn collectively how to edit and change content to better reflect their communities and histories. Learning how to edit Wikipedia can seem daunting, so collectively editing and creating pages is a great way to confront fears; to Do-It-With-Others (DIWO) in a safe space. Besides you will learn about the Wikipedia community values and principles and how such a large community-driven effort has, through the development of bottom-up social rules, become the most important encyclopedia in the world. All together, Wikipedia remains an important space worth investigating and reclaiming!
Organising a wikistorming involves gathering a group of friends (and friends of friends) who want to learn or already know how to edit Wikipedia, and identify a safe space in which to hold the event. It can be held in someone’s home, in a community centre, at an art centre or at a community organisation. Wikistorming can (and should) of course be organised for any day, but Ada Lovelace Day in mid-October and International Women's Day on March 8 are two specific days on which such gatherings often happen. A wikistorming can last for half to a whole day. Before the wikistorming or as part of it, decide which Wikipedia entries you want create or which existing page you want to edit. Be realistic in your goals and don't put too many edits on your agenda! To edit Wikipedia carefully takes time.
Relevant links:
- Advice on organising a wikistorming: http://femtechnet.newschool.edu/wikistorming
- Great examples of wiki storming: https://blog.wikimedia.org/2015/03/05/wikipedia-edit-a-thons-international-womens-day/
- Lectures about the gender gap in wikipedia and how to overcome it: https://meta.wikimedia.org/wiki/Gender_gap
Dealing with Trolls
Women and trans* persons who begin to grow a following and have influence online might experience what Kathy Siera describes as a “koolaid point” (http://seriouspony.com/trouble-at-the-koolaid-point/). This is a point at which a certain group of people decide that you have too much influence, and make it their mission to silence you or discredit you. This is commonly referred to as 'trolling' - although it is more often than not targeted, discriminatory in nature and hate-based. A troll's tactics can include anything from sending constant derogatory and belittling messages, to editing and distributing images, and even making threats.
Block or engage?
There are two key ways you can deal with trolls. One is to block them and then report them to the platform you are using. The other is to engage with them. The decision on which way to go depends on what you want to achieve.
Blocking trolls can sometimes be effective, and can allow you to continue with your work unimpeded. Projects like Block Together (https://blocktogether.org/) and Block Bot (http://www.theblockbot.com/sign_up) were developed to help people who are harassed share their blocklists with each other.
When trolls are really committed to harassing you, however, blocking doesn't really help. A determined troll can create numerous different profiles (called “sock puppet accounts”) to continue the harassment, and this means your blocking has to keep up with their new account generation. This quickly becomes very tedious.
Historically, platforms like Twitter and Facebook have not handled reports of intimidation and violence very well. However, this is beginning to change, as they recognise the severity of problem and see how it deters people with important voices from using their services.
You might consider the alternative - engaging the trolls who are harassing you. One way to do this is to try and enter into rational arguments with them and interrogate their views. Another way is to try to shame them, or to use humour to deflate their egos. Effective engagement with trolls can actually help to generate debate and public interest around the act of harassment, and can involve others online in discussions about safe spaces, violence, sexism and online behaviour. It can also be a source of empowerment for the subjects of trolling: seeing others laugh at your harasser can be very uplifting.
Swarming can be another way to drown out the voices of the harassers. This can be done in retro style by creating communities of support with your allies in social media spaces where you are likely to encounter harassment. When someone is being targeted, others can quickly be alerted and bombard the harasser with messages. The content of that message is up to you: it could be scolding, educational, or loving. Another option is: instead of directing messages towards the harasser, the swarm can fill the victim's content stream with lots of new content in order to quickly make the negative, violent content disappear into online history.
If you want to engage with trolls, or try “swarming”, you might prefer to stay anonymous to avoid having your real identity trolled. Setting up a network of second accounts to do your troll-response work can be a good idea for your organisation or your community of friends. It might be easier too, psychologically, to say some of the things you want to trolls, than you would if the comments were linked to your main identity. And it is more performative: you can create any kind of identity you want and style it with an avatar, a funny name, a character etc.
However, while battling the trolls in the old-fashioned human way can be fun and eye-opening, it can also be a time waster. Another option to consider is automation using bots. For this you need to do some coding, or you can work with freely available code that someone has already uploaded on a software repository such as Github.
Bots against trolls
A bot is a piece of software that runs an automated task over the internet, performing tasks much faster than we can.
There are many different types of bots. There's the spambot, for example, which harvests email addresses and contact information; and there are also the 1800 approved bots on the English Wikipedia, which help to semi-automate the editing of Wikipedia pages. Bots can post content, gather information and click on things. Twitter is also filled with bots which use algorithms to harvest information and tweet. Many of these are humorous and random - for example @twoheadlines, which grabs random news headlines and combines them to create funny combinations.
A bot can be programmed to document trolls' activities, or talk to them, so that you don't have to. The possibilities outlined below apply mainly to Twitter; however some of these ideas can be used across other platforms as well.
The data-gathering bot: quietly scans Twitter and gathers up tweets, usernames and any other available information you have programmed it to collect. It places this information in a file for you. This bot can be useful for understanding what kind of content is out there, and for doing a first-stage analysis of abuse. Foxxydoxing is such an example; it is intended to help you analyse who your harassers are (https://github.com/DeepLab/FoxyDoxxing).
The simple talking bot: if you follow the #gamergate hashtag on Twitter, you will see a bot called @everyethics which tweets different humorous reasons for the #gamergate trolling, ridiculing the claim that the major trolling which has been called "Gamergate" was not about attacking women in gaming but about “ethics in game journalism”. While this bot could be seen as spam, it was actually clearly a strategy to undermine and make fun of the trolls.
The retweet bot: is programmed to scan Twitter for a list (created by you) of specific words, phrases or hashtags, and to retweet those. This would be a strategy for documenting and publicising Twitter abuse. Here's an example of such a bot you can download and install yourself (https://lilithlela.cyberguerrilla.org/?p=17418).
The autotweet bot: is similar to the retweet bot except that every time it finds a tweet with one of the words, phrases or hashtags you have programmed it to look for, it will tweet a pre-written tweet directed at that user. These bots get shut down much faster now, as was shown by @fembot, which was programmed to automatically respond to racist and sexist tweets. @fembot was blocked after only 75 tweets.
The data-gathering bot in combination with the talking bot: in this example the data-gathering bot finds the users according to your search terms, and compiles them for you to read over, check for accuracy and remove any false positives. Alongside the data-gathering bot, you can have a talking bot or a team of talking bots which can tweet whatever you want to those users. The campaign Zero Trollerance (https://zerotrollerance.guru) used this method, employing 160 talking bots which enrolled 3000 identified trolls in a self-help program and then sent them humorous motivational messages and video clips over a period of one week.
If you are considering creating bots to work for you to fight online bigotry and harassment, there are some things you need to watch out for. Twitter is not against bots and if you just want to create a bot that scans information from Twitter for you to analyse, or a bot that just tweets out to no one in particular, you will likely not encounter any problems. However if you want to tweet @ other Twitter users, you have to take into account Twitter's policy against spam.
Also keep in mind that language is slippery and if you want to tackle violence against women and trans* persons online, you will have to be very careful about what kind of language you search for. For example, every time someone uses the word “bitch” on Twitter to intimidate or harass a someone, there are probably at least five other people using it to tell their friend how much they love them or talk about the latest celebrity affair. The best way to figure out which language is being used for harm is to crowdsource it from people who have been harassed and then do a number of tests, pulling tweets from Twitter and then analysing the results yourself.
Read more of this section, including how to set up Twitter accounts to be bots for you:
Relevant links:
- Simple bots you can download and test out yourself with a little patience, from Lilith Lela: https://lilithlela.cyberguerrilla.org/?p=9247
- How to evade Twitter's spam filters with your bot: https://gendersec.tacticaltech.org/wiki/index.php/Step_2#Evading_Twitter.27s_spam_filters
- Twitter's guide to Automation Rules and Best Practices (https://support.twitter.com/articles/76915-automation-rules-and-best-practices).
- Video global Voices "Do We Feed the Trolls?"ː https://www.youtube.com/watch?feature=player_detailpage&v=YRZTeea9ohM
- How the Zero Trollerance bot army worked: http://www.telegraph.co.uk/technology/social-media/11535405/How-do-you-stop-Twitter-trolls-Unleash-a-robot-swarm-to-troll-them-back.html
Supporting others
It can feel daunting to know what to do when you see someone experiencing online violence, and sometimes in trying to help you can inadvertently worsen the situation. Knowing how to act in the best possible way is our individual and collective responsibility in helping to create a safe space online for everyone. If you are someone who wants to support a disadvantaged group but is not part of that group (men are allies when it comes to women's rights issues), it's important to speak out and say “NO”, in a public space, to online harassment and violence. Otherwise, the culture of impunity to online harassment will continue. Now when your friends or allies are being harassed and/or attacked online, there are some best practices you can follow:
Offer quick support: When someone is being attacked or harassed, try to be quick in bringing in support. If you are close to the person under attack, offer immediate assistance. Bear in mind that this person might feel overwhelmed and might not have a clear set of instructions in mind about how to best supported. Remain quiet, attentive and patient and try to not create any extra pressure or stress. In the event of doxing - where confidential info has been released on the internet about that person - you might want to offer a safe space (a home) if the person does not feel safe in their own home. You can also offer to moderate your friend's Twitter feed or blog comments to allow her/them to take a break from it.
Speak out: If you do not know the person well, you can at least speak out against what is happening. It's not enough to simply send a private email or a tweet to the person who is under attack telling them that you think this kind of behaviour is unacceptable (sometimes, if the person under attack is being flooded with tweets and mails, it's even better not to write at all). Instead, speak out about it in your networks and raise your voice against such behaviour. You can, for instance, commend publicly the work that the person under attack has been doing. Don't be silent, especially if you are a colleague or a team-mate. Make your voice resonate online - particularly if you are a man! Here is a great exemple of Jay Smooth calling On Men To Challenge Anti-Feminist Internet Trolls (https://vimeo.com/44117178)
Organise collectively: If you want to have more impact, think about crafting a "collective action" as those are often more effective than individual actions. Gather a group of friends, and friends of friends, for a Twitter storming, for instance. This will show to the person under attack that you and others care and that such acts are not OK.
Write a solidarity statement: If you are part of an organisation or network, you can write a solidarity statement that explicitly says you condemn online gender-based violence and harassment. Having feminists review the statement of solidarity is a best practice. If it's a person from your organisation who has been under attack, make sure she/they read the solidarity statement before it is released. You can also prepare an organisational policy in advance on what to do if someone is under attack. If you have a policy and specific steps to follow when such a situation occurs, chances are you will do less harm and be more effective in your response. see for instance Tor Solidarity against online harassment (https://blog.torproject.org/blog/solidarity-against-online-harassment).
Talk to the media: Depending on the nature and context of the situation, you might want to speak out through the media and highlight the gendered and sexist nature of online attacks. It's always best practice to consult the persons targeted before speaking to the mainstream media. If you do not know the person personally, go through the web of trust - your trusted online network. Thinking about the harm and added stress that the person can go through if they are made visible in the mainstream media is something that you should carefully assess. Consider especially that this is not about you: this is about fighting sexism online and supporting others!
Resources for support:
- Block Bot: (http://www.theblockbot.com/sign_up) will block known harassers and trolls on Twitter for you.
- Block Together: (https://blocktogether.org/) allows you to share your block lists with others on Twitter.
- Foxxydoxing: (http://foxydoxxing.com/) scripts to help you analyze the connections between your attackers on Twitter and a wonderful graphic story to explain how it works.
- Crash override network: (http://www.crashoverridenetwork.com/) a support network and assistance group for victims and targets of unique forms of online harassment, composed entirely of experienced survivors. They work preventatively and reactively with survivors during episodes of harassment to keep them safe and provide them with the means to reduce harm and rebuild, as well as disempower their harassers.
- The Online Abuse Prevention Initiative (OAPI): is a nonprofit organization dedicated to reducing and mitigating online abuse through the study and analysis of abuse patterns, the creation of anti-harassment tools and resources and collaboration with key tech companies seeking to better support their communities. It works in collaboration with the Crash Overide network (http://onlineabuseprevention.org/)
- Zero Trollerance: (https://zerotrollerance.guru) a humorous, video-based self-help program for sexist Twitter trolls. You can send your Twitter trolls links to individual videos or to the main website zerotrollerance.guru. You can also contact @ztrollerance on Twitter to do it for you.
- HeartMobː is a platform for real-time support to individuals experiencing online harassment and empowers bystanders to act. Visit their Kickstarter project to know more about the initiative (https://www.kickstarter.com/projects/4096561/heartmob).
- Trollbusters: (http://www.troll-busters.com/) still in development, this tool plans to counteract Twitter abuse by flooding your timelines with love messages.
Documenting violence
Besides directly supporting and showing solidarity with people subjected to violence, you can also populate and contribute to the documentation of instances of online violence and harassment. Those initiatives are key in order to show the extent of the problem and to make visible some of the structural aspects of violence in societies.
Resources for documentation:
- APC's Take back the Tech: has collected more than 500 stories of women who have experienced violence online. These stories were gathered using the open source platform called Ushahidi. The data visualisation can be see here: https://www.takebackthetech.net/mapit/ . The overall results of those who have participated in this exercise show that women between 18 and 30 who are using Facebook are most likely to be under online threat (http://www.genderit.org/articles/mapping-strategy-disclose-online-violence-against-women).
- GenderIT.org: emerged from APC's Women’s Rights Programme’s advocacy work in information and communications technologies. The need to have examples of national policy, gender-sensitive language, tools for lobbying, and an understanding of the impact of poor or positive policy all within easy access has been expressed by ICT advocates and policy makers alike (http://www.genderit.org/).
- The Geek Feminism Wiki has been documenting sexist incidents in geek communities. To see the timeline of incidents: (http://geekfeminism.wikia.com/index.php?title=Timeline_of_incidents). You can also check out their resource pages for allies supporting support women in geek communitiesː (http://geekfeminism.wikia.com/wiki/Resources_for_men)
- Women, Action, and the Media (WAM!) has written a report on online violence on Twitter (https://womenactionmedia.org/cms/assets/uploads/2015/05/wam-twitter-abuse-report.pdf/) and created a Twitter Harassment Reporting Tool (https://womenactionmedia.wufoo.com/forms/wam-twitter-harassment-reporting-tool/).
- Breaking the circle is an international campaign to raise awareness on the fact that gender violence is a problem that concerns both men and women, which focus on the role of men and include them as agents of change. They have developed a series of tools and information that will help us spread the message and raise awareness (http://en.breakingthecircle.org/).
- Crowdmaps in Indiaː After the Delhi Gang Rape there was a lot of interest in how tech could be used to address the issue of sexual violence against women in offline spaces. These initiatives emerged from spaces where tech meets gender in order to see how tech can be used to tackle gender based violence gender problems. See for instance Harassmap in Bombay (www.akshara.crowdmap.com ) and the Safecity -Pin the creep (www.safecity.in) and the 'Safetipin' app for safely auditing public spaces.
- Macholandː This french platform wants to voice actions, embedded in the public, media and political speech, driven by citizens who refuse to see sexism spread massively without reacting. Each user can participate and propose an action that pin with humor brands, organizations and public figures (http://macholand.fr/)
- Feminist Frequencyː This project includes the video series Tropes vs. Women, created by Anita Sarkeesian with Bitch magazine to examine common tropes in depictions of women in film, television and video games, with a particular focus on science fiction. Videos produced in this series include “The Manic Pixie Dream Girl”, “Women in Refrigerators” and “The Smurfette Principle” (http://feministfrequency.com/)
Safe spaces offline
Many of the principles of creating and maintaining safe spaces online can also be applied offline. As noted in the introduction of this chapter, safe spaces can either be temporary and take place during a one time event or training or can also become permanent spaces where collectives or organisations embed the basic principles of safety, support, respect and inclusiveness in their own space management.
In the case of security and privacy training, you also need to consider how participants can best learn skills to protect themselves when the topics themselves can be frightening or overwhelming. The environment also has to be suited to the participants share stories about threats they have been facing online and offline. Those stories can be very traumatic and personal and should be handled carefully, but at the same time they are a very important part of the process of developing security and privacy strategies.
The difficulties in defining what a "safe space" should look like are inherent in the fact that you are bringing a diversity of people together, who might be considered to be part of the same community but who all have different histories, contexts and needs. What one person might find politically, socially or personally threatening might mean very little to another. And everyone will of course also come with different experiences and levels of knowledge and skills with regard to technology.
It is important to be aware that, in struggling to perfect a safe space, one always runs the risk of creating instead yet another form of social control and pressure to conform to a particular image of what, for example, a woman or trans* person is or should be.
Boundaries
When trying to create a safe space, you might encounter the issue of who is included and who is excluded from it. It can very divisive, as it will often touch on people's strongly held sense of their political, personal, sexual and social identities. Issues of sexual orientation and gender identity will likely come up. Some will prefer a women and trans* only environment, some will feel that this opens up an opportunity for external attacks on the whole project by adversarial forces, while some will feel that cis-men friends and colleagues are being unfairly excluded, and feel resentful. If you are having a debate about this, some things to consider are:
- Is there an agreed framework and rules of engagement? How do we define "woman" and "trans*"? How do we define "safe"?
- Who do we want to include, influence or support? Specifically women and trans* persons, or also potential allies?
- How important versus how contentious? Is it worth alienating some people from the group? How can we frame the debate to avoid alienating people who don't agree with the decision?
- How will the decision affect the actual experience of people within the space?
- Do we have all the skills we need to deliver this project among our networks, or will we need specific additional skills? Where will we get them?
- How will the space be organised to promote equal participation, especially if cis-men are included?
It's important to remember that building offline spaces is resource- and labour-intensive, and often many compromises have to be made. It may be a good idea to try to identify as early as possible which values are shared, important, and relevant to the event, so that you can constantly remember to prioritise those and de-prioritise less important or potentially divisive issues.
Building offline spaces is easiest and most successful when you're clear about what you're trying to do and how you plan to go about it. The second thing which must be considered is exactly what the event is intended to achieve. For example:
- Skills: How can we learn to do xyz?
- Advocacy: How do we change the culture of tech sectors to be more amenable for women and trans* persons, and/or let the world know that they are great at tech?
- Support, networking and boundary-crossing: What does it mean to be a woman or trans* person in tech? How can women from different places or sectors come together to spark off new ideas and practices? How can we support each other as women and trans* persons in tech?
Different aims will inform different safe space policies. For instance, it's difficult advocating for change in the male-dominated tech sector if you haven't invited cis-men to hear what you want to say - but you might prefer to discuss *how* to do this in a women and trans*-only environment first. If, on the other hand, you are advocating for engagement with technology to women and trans* persons and mainly want free, honest and mutually supportive discussions or skills-sharing, then in this case, a women and trans* only environment suggests itself.
With skills workshops, there is research to suggest that women and trans* persons learn tech skills best with each other, so these workshops have a very clear and communicable reason for being exclusive. Another possibility is to run an event twice, once for women and trans* participants and once for open participation. This can have the positive side-effect of enabling others to experience a safe space methodology and thereby change their own practices in the spaces they organise, but it will be clearly more time consuming.
Choosing a format that fits
Once you have settled the basic questions on what your event is for and who you want to invite, it's time to think about the format of your event. Deciding which format to use can be helped by your answers to some key questions:
- What are you trying to do? Which format will support this activity best?
- What are the participants' needs, existing skills, experience and preferences?
- What physical spaces are available, what will they allow you to do, and what resources do you have?
- What are your human and organisational resources - how much can you take on?
There are many different ways of organising events. Some of the most popular in FLOSS and tech-related communities are:
- Un-Conference: helps people to make connections, share knowledge, collaborate and inspire each other. To take part, participants are encouraged to give a presentation, create a discussion, or even chair a debate (http://lanyrd.com/blog/2012/unconference-howto/ ; http://openspaceworld.org/wp2/what-is/). This format can be relatively egalitarian and relatively easy to organise (no messing about with programmes, scheduling and advanced prep) but you should watch out for the tyranny of structurelessness. Thy can also be extremely intimidating and therefore exclusionary towards less experienced or skilled participants; and can be stressful if you need to organise tech or other resources for specific activities in advance.
- Workshop: transferring skills or knowledge in an interactive session. There are many possible workshop methodologies. Selecting a workshop format is very much about being clear about what you want to achieve. Workshops can be a good format for building skills or for maker and design activities. For instance in Pakistan Hamara Internet is a campaign by Digital Rights Foundation that seeks to raise awareness about violence against women online through various workshops. It literally means ‘Our Internet’ in English and works to impart digital security tips and training to women and bridge the gender digital divide in Pakistan (http://hamarainternet.org/).
- Hackathon: With its general motto "programming till someone drops from exhaustion", hack events can mix different groups - like NGOs with hackers - to come up with new approaches to building technology for that group. For instance IGNITE (Women Fueling Science and Technology from the Global Fund for Women International) organised a global Hackathon called #hackgirlsrights. This 24-hour, multi-country coding event, targeted girl coders which collaborate to develop a website or application that address specific challenge facing girls and young women (http://ignite.globalfundforwomen.org/gallery/ignite-international-girls-hackathon). On the past 23th of April 2015, another global feminist hackaton called femhack was organised around the world in loving memory of Woman Human Rights Defender Sabeen Mahmud (https://f3mhack.org). You can read more about how to run a hackathon here: (http://globalvoicesonline.org/2012/11/23/hackathons-in-droves-how-is-a-hackathon-organised/)
- Sprint: A sprint is a gathering of people involved in a specific project to further the focused development of some aspect of the project, such as working on sections of code, writing manuals or books, etc. These are effective at getting a lot done quickly for code and manuals (less so for other forms of writing), but can be exhausting and emotionally demanding - make sure you keep food and drink coming! To read more about sprints, visit wikipedia: (https://en.wikipedia.org/wiki/Sprint_(software_development) and Flossmanuals: (http://www.flossmanuals.org/service/booksprints). To note for instance that this manual was edited during an editorial sprintǃ
- Seminar: A seminar brings together a small group for recurring meetings which focus on a particular subject. In a seminar, everyone actively participates, or offers information or training on specific topics. On the one hand, this kind of structured activity supports people with less experience or confidence; planning for tech/resource support is fairly straightforward; and people know what to expect. On the other hand, the event can be experienced as overly structured and lacking spontaneity for more experienced participants; more 'top-down'; and requires more organisational effort in advance. Check out for instance The documentation of the Feminist Server Summit which consisted in a feminist review of mesh- cloud- autonomous- and D.I.Y. servers (http://vj14.constantvzw.org/r/about).
More stable kinds of safe spaces for experimenting and learning technology include:
- Hacklab, hackerspace or makerspaceː These are community spaces with hardware and/or tools - great for people to "get their hands dirty" and play around with anything - from taking computers apart to installing Linux to making music with bananas or building a radio out of razorblades and wire. Read more about hacklabs and hackerspaces here: "Hacklabs and Hackerspaces: Shared Machine Workshops":(http://www.coredem.info/IMG/pdf/pass11_an-2.pdf). You can also visit the following portalsː (http://makerspace.com/) (http://hackerspaces.org/)
- Feminist hackerspace: Those vary in shape, form, and size. What often unites them is a set of boundaries that are decided on collectively (who can be a member, who can be a guest, what are the policies, etc.) and an explicit belief in feminist principles. Feminist hackerspaces provide a place to work on individual and collective projects in a supportive environment. To know more about feminist hackerspaces you might want to visit the website Mz Baltazar’s Laboratory in Vienna (http://www.mzbaltazarslaboratory.org/), The Mothership Hackermoms in Berkeley (http://mothership.hackermoms.org/), Double Union in San Francisco (https://www.doubleunion.org/) and FemHack in Montreal (http://foufem.wiki.orangeseeds.org/).
For sharing skills, setting up a feminist hackerspace, or choosing an unconference, workshop or seminar format makes a lot of sense. For advocacy and networking events, the choice is not so obvious. Advocacy events can be some of the most challenging as it's easy to spend the entire day "re-inventing the wheel" with people who are new to the questions. If you have participants from diverse backgrounds in your advocacy event, it could be best to go with a more structured format. Unconferences and hackathons work best with activists or experienced practitioners who are used to a high level of self-determination, and who have a shared understanding of the implicit rules and structures of the space. Having said that, it can work well to try more open formats anyway, but be prepared for some skilled facilitating to make it a safe and fun space for both experienced and less experienced participants. Sometimes a mixed approach is what's needed - and some experimentation!
Fixing gender gap in tech
In order to get some inspiration we list below a selection of initiatives specially oriented at getting more women in ICT and technological related fields.
- Asikana Network (Zambia)ː is a group of females aiming to empower women in ICT related fields by changing mindsets and eliminating negative stereotypes attached to girls and women in ICT (http://asikananetwork.org/).
- Akirachix (Kenya)ː is an african wide network of women in technology to make tech and to inspire and mentor other women to be technologists (akirachix.com).
- Donestech (Spain)ː is a cyberfeminist and activist research group which develops also workshops and audiovisual productions in relation to gender and ICT access, uses of and desires. Lelacoders project is about studying and making visible the presence of women in the development of computer sciences, free software and hacker cultures (www.donestech.net) (https://n-1.cc/g/donestech+lelacoders).
- Feminist Approach to Technology (India)ː mission is to empower women by enhancing women’s awareness, interest and participation in technology (http://fat-net.org/).
- Flossie (UK)ː runs a conference and also skills workshops and it is intended to combine advocacy, boundary-crossing, support and skills-sharing bringing together women involved in digital arts with coders, artists, and makers (http://www.flossie.org/).
- Speakerinnenn (Germany)ː aim is to increase the visibility of women in the field of public speaking. With the help of our list it will be easier for organisers to find female experts to speak at their events (http://speakerinnen.org/).
- The Ada initiative (Global)ː organises AdaCamp, a series of conferences dedicated to increasing women’s participation in open technology and culture: open source software, Wikipedia and other wiki-related projects, open knowledge and education, open government and open data, open hardware and appropriate technology (https://adacamp.org/).
Codes of conduct
It's important, especially in mixed environments, to think about what's acceptable conduct in the space and what isn't. In order for this to have any practical effect, it's also important to think about what you'll do if individuals breach this - or when things go wrong generally. You can find plenty of information and example policies on the Geek Feminism Conference anti-harassment/Adoption page (http://geekfeminism.wikia.com/wiki/Conference_anti-harassment/Adoption)
Make sure your participants understand the policy and how it relates to their own conduct. It can be useful to make time in your schedule at the beginning of the event to share your policy, and reach consensus with the group on how to maintain a safe space over the days of the event.
Your code of conduct should be about preventing aggressive behaviour and not about trying to police how people identify, communicate or present themselves. It's also worth remembering that people who are struggling in a culturally unfamiliar environment can become confrontational more easily than they usually would. There may be many reasons why a participant might be struggling to communicate positively at any given moment. It's key to remain calm and to provide a non-judgmental space for the expression of emotions like anger or frustration. Because of this, a code of conduct should also include some people that will be assigned to receive feedback if any problem takes place. They should be good facilitators or moderators and be calm and patient. We are different, let's celebrate it, even when it's difficult to do!
Last not least, your code of conduct should include an agreement about how participants will respect other participants' right to privacy. Some general guidelines could include the following:
- Don't take or circulate sound, video or photos without permission. If anyone present faces significant external risk then don't take photos at all unless participants have given express permission and an opportunity to cover their identity.
- If you wish to record the event, prepare formal consent forms telling people exactly what audio-visual records are being made and how they will be stored, used, licensed and ask for clear consent with a signature.
- Don't share details of anyone's participation, speech or actions on social media without their express permission.
How safe is the space?
As a check-list, here are some questions that can help you assess whether a space is safe or not.
- Background: What is the history of the space? Who started it and why? How many women and trans* persons have been involved?
- Participation: Who has stopped participating in the space since it was founded, and why? Is it mostly women who have left?
- Policies: Does the space have policies? If so, what kind? Are the policies regularly put in practice? Ask members in the space, particularly women.
- New people: How does the space welcome newcomers? The first time you went to the space, did you get a tour? Did people say hello? Were the people in the space friendly?
- Regular assemblies: Are there regular meetings (assemblies) that offer possibilities to raise concerns, to suggest collective projects, to suggest the organisation of workshops, to discuss the space (its cleanliness, etc.), to present yourself, etc.?
- Language: Is the language and vocabulary used on the website and in the space explicitly feminist? Read the website carefully, or go and see for yourself what the space looks like.
- Trust: Do you know people who you trust in the space or do you know friends of friends? The web of trust can be very useful here.
- Access: Who can go into the space and under which conditions? This should be made explicit on the website, otherwise ask.
- Accessibility: Is the space itself easily accessible? In which part of town is it located? Are there bathrooms? What are the opening hours? Who has access to the keys of the space?
- Cost: How much does it cost to become a member? Is there a sliding scale policy?
No space is perfect; a safe space should always, however, at least provide an environment and a set of boundaries in which to meet up, talk, and address and raise difficult issues. If you feel the space has potential and you want to get involved, don't be shy!
Relevant links:
* Integrated Security Manual: (http://www.integratedsecuritymanual.org/) a resource for planning, convening, and hosting your workshop which prioritize your participants' emotional and physical well-being.
* Level Up: (https://www.level-up.cc/resources-for-trainers) resources for digital security trainers and organisers of these trainings too.